Studying to be a nurse? Then follow along with this nursing how-to video to learn how to administer an intradermal injection. This injection technique is very common in nursing. Watch and observe the nursing student as she shows you the proper protocol for an intradermal injec ...more
Injecting intramuscularly is a difficult thing to learn and it takes a lot of practice. This instructional medical how to video guides your through the step by step process of giving an intramuscular injection. Watch and read along. It is important to wash your hands before ha ...more
Intra-muscular injection is a simple technique; however, it can lead to serious complications if is not properly performed. This video was produced by the US army and it is one of the most simplified and educative video to teach how to give an injection properly Medical Videos ...more
Learn how to care for your pet with help from VetVid. See how to give your diabetic cat an insulin injection with this video tutorial. In this video, Dr. Mike educates you on the importance of using the proper syringe for your concentration of insulin. He also shows you an ea ...more
Cats are notoriously bad at taking medicine, especially if it comes in the form of a needle. In this clip, Dr. Lauren will teach you how to give your furry friend an injection for things like diabetes and other illnesses. So, follow along to avoid the scratches and do it the e ...more
Not every nurse can get an IV every time, that's why it's important to stay in practice for the proper technique used for inserting a peripheral IV. This is a common medical procedure that all fields related to medicine should know. Even the soldiers in the military are taught ...more
This tutorial will show you how to hack Elder Scrolls IV (4): Oblivion for the PCand give yourself infinite money. You can use this Tutorial as an example on how to hack any game you want!
Do you guys remember those things you hold with your fingers to write stuff down? I think they're called pens, or something like that... In a world that is increasingly more digital, pens and pencils have been relegated to shadows of communication methods. You handwriting and ...more
Hello NullByte! This will be my first How To series. In this tutorial you'll learn what SQL is, what SQL injection is and how it benefits you as a hacker. I strongly recommend learning at least the basics of PHP before attempting to learn/use SQL Injection. list of reference ...more
Welcome back, my hacker apprentices! Although there is a multitude of different hacker types, the one target they all share is the database. I often refer to the database as the hacker's Holy Grail, or the ultimate prize for an effective hack. That's because the database—alm ...more
One of the ultimate goals in hacking is the ability to obtain shells in order to run system commands and own a target or network. SQL injection is typically only associated with databases and their data, but it can actually be used as a vector to gain a command shell. As a les ...more
Ransomware is software that encrypts a victim's entire hard drive, blocking access to their files unless they pay a ransom to the attacker to get the decryption key. In this tutorial, you'll learn how easy it is to use the USB Rubber Ducky, which is disguised as an ordinary fl ...more
Dirty, malformed, and outright mischievous text strings have long been the enemy of interactive website developers. Strings contain any combination of letters, numbers, spaces, and punctuation, and are entered into text boxes on websites by users. These strings in particular c ...more
Welcome back, my novice hackers! You have probably heard of the Panama Papers hack by now. This was a hack of the servers at Mossack Fonseca, a major law firm in Panama. This law firm specializes in assisting the rich and powerful to hide their wealth from taxes and scrutiny ...more
Andre was enjoying the carefree life of a 12-year-old with his friends, riding his bike and playing sports, like all kids that age. Schoolwork wasn't hard for him, and his grades showed that. Then, the headaches began. He lost vision in one eye, symptoms that drove his famil ...more
Osteoarthritis can affect every gender and at any age but it commonly occurs in women than in men. In America there are approximately 27 million Americans aged over 25 who live with osteoarthritis. Osteoarthritis commonly occurs after the age of 45. Men who are under the age ...more
While the security behind WEP networks was broken in 2005, modern tools have made cracking them incredibly simple. In densely populated areas, WEP networks can be found in surprising and important places to this day, and they can be cracked in a matter of minutes. We'll show y ...more
Besside-ng is the hidden gem of the Aircrack-ng suite of Wi-Fi hacking tools. When run with a wireless network adapter capable of packet injection, Besside-ng can harvest WPA handshakes from any network with an active user — and crack WEP passwords outright. Unlike many tools, ...more
The last few months of WikiLeaks controversy has surely peaked your interest, but when viewing the WikiLeaks site, finding what you want is quite a hard task. Despite rumors of easy access via the Kindle and iTunes App Store, there currently is no way to view the leaked docum ...more
Let's face it— most people don't understand Shakespeare's language. If they say they do, they're probably lying. The poetic words of the world's most famous playwright continue to plague school children and college lit. majors alike, but not anymore. SparkNotes, one of the on ...more
Looking to mod GTA 4 for the PS3? Here's how to do it. This video gives you the info and links to get tweaking this already killer game. You will need: a PS3 on Firmware 3.41, an external HDD, a device to hack your PS3. Watch the vid and learn how to hack GTA 4 for PS3.
Here is the "Rolled Over" Achievement. You need a decent vehicle. Then drive to the airport located on the far right of the first island. Jump of the mini ramps until you get five consecutive rolls or flips. When I did the five rolls, it did not give me the achievement until I ...more
The Hyco cold vaporizer. This is a cold vapor unit which can give 50-80 % fuel mileage plus, if done to the instructions on the video. By George Wiseman of Eagle-Research. This device can easily be replicated from parts from a local hardware and automotive store. Just by wat ...more
I have had a lot of people ask me, "How does my neighbor keep getting into my wireless?!". Chances are, these people are all using WEP, a deprecated wireless encryption protocol. Either that, or you are using one weak WPA passphrase. If someone can access your wireless networ ...more
Movies spoiled The Crying Game- The chick's a dudeBlair Witch ProjectReservoir Dogs- Tim Roth is a CopA Beautiful Mind- Ed Harris and Paul Bettany are Russel Crowe's imaginary friendsSixth sense- Bruce Willis dead whole filmUnbreakable- Samuel L Jackson staged all the catastr ...more
Studying to be a nurse? Then one thing you must know how to do is administer an intramuscular injection. Follow along in this nursing how-to video to learn the proper procedure for giving patients an IM injection in the deltoid muscle. Before starting always make sure you have ...more
This gives a variety of cheat codes for Grand Theft Auto IV. Follow this and learn how to hack GTA 4 for the PS3. Cheat at GTA IV. Click through to watch this video on garagetv.be
Are you the expert hacker we're looking for? Do you have a great idea for an article on Null Byte? Do you have a passion to write, and more importantly... teach? We're officially looking for Null Byters on a weekly basis who are willing to take the time to educate the communi ...more
Fads, Fiascoes and Good Stuff in FrontierVille This Week The second in a series of weekly columns. Fads first It’s still St. Patrick’s Day in FrontierVille, but it looks as though its days are numbered. I give it 'til the end of the month. Trees are in full summer leaf and ...more
Use mouse and keyboards to play this game. To move the camera, press and hold the right mouse button. Moving mouse freely moves the helicopter. Acceleration is set in (W) button in keyboard. To slowdown press (S). Rotating left is set in (CTRL) and right in (ALT). Use (CTRL+AL ...more
In this video Dr. Schultz will show you how to control extreme underarm sweating. If you suffer from extreme underarm sweating, despite regular use of antiperspirants, follow these steps: Make an appointment with your doctor so that they can give you a prescription for a topic ...more
Big brother is watching when you're playing around on another system—and big brother is that system. Everything from operating systems to intrusion detection systems to database services are maintaining logs. Sometimes, these are error logs that can show attackers trying vario ...more
In the first part of this series, we learned about darknets, as well as how they came about. But these patches of forgotten Internet are not the oasis of free information you might think. Despite being hidden—or just harder to come across—these networks are no more safe then a ...more
Problem: You're a PC gamer who absolutely loves The Elder Scrolls series and were eagerly anticipating the release of the newest game, Skyrim. But as much as you'd like to pick up the new game, money is tight. What do you do? Solution: Mods! The previous game in the Elder Sc ...more
If you're the proud owner of a Canon EOS DSLR, then you'll be glad to know that you no longer have to use EOS Utility on your computer to enable remote live view shooting with your camera. Now, all you need is your Android equipped smartphone (sorry iPhone users) and a new mob ...more
Get luscious, pillowy, kissable lips—with or without injections. You Will Need * Lip balm with SPF 30 * Sugar * Olive oil * A toothbrush * Lip plumper or cayenne pepper * Petroleum jelly * Lip injections * A lip implant * Vitamin E capsules * Plant-based oils Step 1: Avoid ...more
Last Friday's mission was to accomplish solving HackThisSite, realistic 2. This second mission in a series of realistic simulation missions was designed to be exactly like situations you may encounter in the real world, requesting we help a friend take down a racist hate-group ...more
In this Null Byte, I'm going to teach you about Null Byte Injections. Null Bytes are an older exploit. It works by injecting a "Null Character" into a URL to alter string termination and get information or undesirable output (which is desirable for the malicious user). All l ...more
Another week has passed on the online battlefield as the CISPA legislation continues to grind away at our freedom. Here at Null Byte, we try to keep our community informed and knowledgeable at the same time—and that means creating content for them to learn from. After last we ...more
Last week, we had a great contribution from Christopher Voute, who introduced us all on some of the basic moves in Python. Now, who else will share their knowledge and tackle some of the topics below? If you know a thing or two, don't hesitate to teach us what you've got, bec ...more
There is a vast amount of knowledge out there on computers! In fact, it is so vast that no single person could ever possibly ever learn everything there is to learn about hacking or computers in general. People usually specialize in a certain field: cryptography, computer secu ...more
What is Google Dorking? Well, simply put, "Google Dorking" is just an efficient way to utilise keywords in order to perform very specific searches on a given subject. In this case, one would look for websites/servers that are vulnerable to attacks or are configured improperly ...more
General Tips for Exercising in the Heat -Schedule workouts for the cooler times of the day. -Allow overweight, out of shape or unacclimated kids time to acclimate to the heat. -Schedule timed water and rest breaks every 30 minutes during activities. During these breaks, do ...more
This is my first contribution in an ongoing series on detailing the best free, open source hacking and penetration tools available. My goal is to show you some of the quality tools that IT security experts are using every day in their jobs as network security and pen-testing p ...more
Pull up outside any construction site and you'll see tools scattered about—hammers, jigsaws, nail guns, hydraulic pipe benders—these are the tools of the trade. You would be hard-pressed to build a home or office building with just your hands! On that same page, security profe ...more
In my first installment in this series on professional hacking tools, we downloaded and installed Metasploit, the exploitation framework. Now, we will begin to explore the Metasploit Framework and initiate a tried and true hack. Before we start hacking, let's familiarize ours ...more
WonderHowTo is made up of niche communities called Worlds. If you've yet to join one (or create your own), get a taste below of what's going on in the community. Check in every Wednesday for a roundup of new activities and projects. Thanks to all of our active moderators and ...more
WonderHowTo is made up of niche communities called Worlds. If you've yet to join one (or create your own), get a taste below of what's going on in the community. Check in every Wednesday for a roundup of new activities and projects. Thanks to all of our active moderators and ...more
Warnings i cant be held responsible for any illegal act done by anyone but myself and there are copyrights so notise that taken the trademarks or copyrights are strigtly prohibeted by law and will be punshied by law and i or my partners cant be held responsible for sudo camma ...more
Injecting intramuscularly is a difficult thing to learn and it takes a lot of practice. This instructional medical how to video guides your through the step by step process of selecting a site for an intramuscular injection. Intramuscular injections should be given in areas wh ...more
This video will show you how to get rid of stretch mark scars and acne blemishes. Your treatment options depend on the type and severity of your scarring. One way to improve the appearance of a scar is through a collagen injection, given by your dermatologist. Corticosteroids ...more
APOLOGIZE Hello my masters and colleagues, first of all I would like to apologize for my absence during the past month, to say that i was busy with some projects and decide to leave the white-side for a while and made some visits on the dark-side(every good COP has a dealer f ...more
Auditing websites and discovering vulnerabilities can be a challenge. With RapidScan and UserLAnd combined, anyone with an unrooted Android phone can start hacking websites with a few simple commands. RapidScan does an excellent job of automating the deployment of vulnerabili ...more
Full disclosure — I have almost zero Street Fighter experience. The first time I played the game was at Barcade, way back in ... 2017. Yes, to the shame of gamers everywhere, this reviewer is a Street Fighter noob. Fortunately, my inexperience does nothing to hinder my apprec ...more
The USB Rubber Ducky comes with two software components, the payload script to be deployed and the firmware which controls how the Ducky behaves and what kind of device it pretends to be. This firmware can be reflashed to allow for custom Ducky behaviors, such as mounting USB ...more
After years of telling patients to finish any prescribed course of antibiotics completely, a group of researchers in the UK say it is no longer necessary, and could even be harmful if we want to preserve the antibiotics we can still use. You read correctly, in an analysis pub ...more
Information gathering is one of the most important steps in pentesting or hacking, and it can often be more rewarding to run things on the target itself as opposed to just running scripts against it remotely. With an SQL injection, a hacker can compromise a server and, ultimat ...more
Saying that I was obsessed with Pokémon as a child would be a serious understatement, and even though I'm not the Pokémon fanatic I once was doesn't mean I don't love playing still. However, I do often find myself dumbfounded by all of the new features and characters in each g ...more
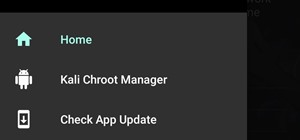
No more carrying around heavy laptops and thousands of Linux Live CDs and USBs to always be ready for pentesting on the fly! I hope you had a good Christmas and happy new year! Update1: Added the section "weaponizing your Android" where I talk about apps and fundamental Kali ...more
Welcome back, my greenhorn hackers, and happy New Year! Now that your heads have recovered from your New Year's Eve regaling, I'd like to grab your attention for just a moment to preview 2015 here at Null Byte. I hope you will add your comments as to what you would like to se ...more