I'm a pretty nice person, so when someone asks me to take a group picture of their friends or family, I can't easily say "no," even if I have somewhere else to be. Even worse—sometimes I'm the one asking, fully knowing just how annoying it can be. Maybe you've been told "no" b ...more
Okay, here we go. Here is the deal. Bam, Knoxville, Dunn, Steve-O, Party Boy, Jeff Tremaine, and myself are dressed in old man faces, but wearing tshirts that say "Beer is Good" and wearing diapers. (Substitute speedos for diapers if you want). We are gathered around Jack Nich ...more
This past Sunday, a group called Gnosis launched a massive hacker attack on Gawker media, one of the web's most popular blog networks (Lifehacker, Gizmodo, Jezebel, io9, Jalopnik, Kotaku, Deadspin and Fleshbot). 1.3 million registered users' passwords were compromised, and 188 ...more
There's a lot of talk going around about Google's new social network and how it's heavily influenced by Facebook, but truth be told, how could they build Google+ without taking a note or two from the world's most popular social network? One thing that's different (and better) ...more
Meet Newstweek, a hidden device engineered to hack news items being read at public WiFi hotspots (cafes, libraries, airports, etc.). Both nefarious and tech-saavy, the ingenious mechanism wasn't fathered by a group of web hackers, but rather a pair of Berlin artists, Julian Ol ...more
Hallelujah, a miracle tool has been released to the world. This Windows/Mac tool is called Spirit and it enables you to jailbreak any iPhone, iPod Touch or iPad quite easily. And Gizmodo is all over it, with an in-depth guide on exactly how to do it. Some of you may be hackin ...more
Social network fatigue sets in when it starts to feel impossible to keep up with all that new content from your friends, followers, and acquaintances on a daily basis. You lose track of stuff you wanted to read more about, and you miss important news from your friends, but are ...more
Want to take advantage of your neighbor's super fast Wi-Fi connection? If they're smart, they probably have it password protected (otherwise you wouldn't be reading this, would you?). But if you have an Android phone, you can get back at them for always parking in your spot an ...more
General Motors (GM) seems to have gone to great lengths to avoid lawsuits as it launches its first hands-off driving system in its soon-to-be-launched Cadillac CT6. As GM makes the Cadillac CT6 available to a limited number of reviewers ahead of its launch this fall, early te ...more
In this project, I'll show you how to make an itty-bitty outdoor BBQ from leftover beer or soda cans. It's the perfect summertime hack if you don't have a grill and are cooking for a small group of people—one bratwurst at a time. You can grab the wire grill template here. Vide ...more
The Shadow Brokers, a hacker group known for its dump of NSA hacking tools in 2016, has just leaked their remaining set of data which implies that the NSA compromised SWIFT, the global provider of secure financial services, to spy on banks in the Middle East. The hackers have ...more
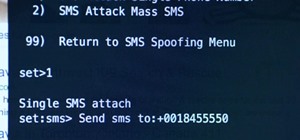
Welcome back, my novice hackers! As most of you know by now, a notorious commercial, legal hacking group named "Hacking Team" was recently hacked. As part of the hack, thousands of emails and other material on their servers was divulged. Among the material released were three ...more
Null Byte users have often requested video content, but the question has always been what format would best serve our community. This week, we partnered with Null Space Labs, a hackerspace in Los Angeles, to test the waters by hosting a series of talks on ethical hacking for s ...more
We've already shown you how to dunk a regular-sized Oreo cookie while keeping your fingers pristine, how to upgrade Oreos into different desserts, and even make them into lazy ice cream sandwiches. Now we're going to introduce you to a few other essential Oreo hacks that will ...more
A human rights activist from the United Arab Emirates recently stumbled upon three gaping security loopholes in iOS that work by enticing you to tap a link sent to your iPhone. Ahmed Mansoor received a text message from an unknown number roughly two weeks ago, but instead of f ...more
Welcome back, my nascent hackers! We have spent a lot of time in previous tutorials focused on hacking the ubiquitous Windows systems, but the vast majority of "heavy iron" around the world are Linux or Unix systems. Linux and Unix dominate the world of Internet web servers w ...more
As the level of data being generated grows exponentially, past the Information Age and into the coming Hyper-Information Age of immersive computing — as resistant as many of us are to the idea — personal data security is becoming a necessary consideration in our everyday lives ...more
What's your Twitter handle worth? If it's considered "desirable" (aka short and simple), it'll get you around 100 bucks, or, if you prefer, the affections of a teenage girl. A user with the handle @blanket found out the hard way that Twitter's security is atrocious when his a ...more
Chrysaor, a zero-day spyware believed to have been created by the Israeli "cyber war" group NSO, is an even greater threat to Android phones than it ever was to iOS. Related to the Pegasus hack that recently affected iPhones, Chrysaor is malware that baits the user into insta ...more
There's something great about sweet, ripe strawberries coated in a bit of hardened chocolate. They're decadent, beautiful, and make for the perfect after-dinner dessert. We love to make them for a group, but are often thrown off by the long and messy process of it all. Then w ...more
Great ideas often strike at random times, but messaging friends and loved ones at an inopportune hour not only risks their wrath, but also increases the chances of your message not being paid proper attention to. Thankfully, there's an app that lets you create and post WhatsAp ...more
Wet shoes are uncomfortable, no one can deny that. Just think about walking around with soaking wet footwear ... and each squishy step you take. Makes you cringe, doesn't it? It can happen in heavy rain, at the beach, or from an unforeseen puddle on the street. And while you c ...more
While we haven't covered Amazon Web Services, or AWS, on Null Byte before, Amazon's cloud computing platform is ripe for attack by hackers, pentesters, and cybersecurity researchers. It's also an excellent cloud hosting service to build or use vulnerable-by-design AWS setups a ...more
Welcome back, my greenhorn hackers! Digital forensics and hacking are complementary disciplines. The better you are at digital forensics, the better hacker you are, and the better hacker you are, the better you are digital forensics. Unfortunately, few people in either profes ...more
WikiLeaks. In recent weeks, it's been the hottest topic on the web. It's been attacked on a multinational level by political influence peddling. First, U.S. Senator Joe Lieberman swayed Amazon's decision to stop hosting WikiLeaks. Then, Tableau Software removed graphs from th ...more
With FarmVille being one of the hottest Facebook games on the market, it's no wonder it's the primary target for scams and virus downloads. Anyone playing FarmVille is at risk, but the primary targets are those looking to improve their gameplay and build their farms and neighb ...more
Bouncing Balls is a Facebook game that allows you to destroy balls left and right! Get Bouncing Balls hacks, cheats, tricks and tips! Watch this video tutorial to learn how to hack Bouncing Balls on Facebook (08/13/09). Description of the app on Facebook: In this game there ...more
This video demonstrates a very simple way to broadcast your voice on the same frequencies that a drive-thru restaurant uses, enabling you to mess with the customers and employees. This hack will work on just about any fast food drive thru. If you like the drive-thru pranks on ...more
Flash games are addicting, especially Bouncing Balls. But can you actually beat all of those high scores you see? Probably not, but you can if you use Cheat Engine. Watch this video tutorial to learn how to hack points in Bouncing Balls (10/11/09). Download Cheat Engine 5.5 i ...more
This is a very lengthy explanation on BTD playing. There's a lot to actually know about the strategy of Bloons Tower Defense. This video tutorial will show you how to place towers in Bloons Tower Defense (10/08/09). Many people will tell you that you should place your towers ...more
+Tom Anderson of MySpace has been very active on Google+ over the first week, and he's not shy with his thoughts on the evolution of the industry he once owned. Here's his take on this morning's Facebook announcement and Mark Zuckerberg's response when asked about Google+. To ...more
Understandably, the tragedy in Japan has substantially risen the level of worldwide radiation-related hysteria. So much so, as an alternative to stampeding health food stores for iodine tablets, crafty individuals and organizations are hacking together personal radiation detec ...more
The world has been overflowing with Microsoft Kinect hacks, each more amazing than the last. The latest innovation, created by a group of engineers at USC, promises an exciting future in gaming (and gets gamers off their asses). The program is called FAAST, and allows for full ...more
Over the past couple of weeks, there have been a series of high-profile hacks and leaks. From the rooting of CombinedSystems, to a secret FBI conference call leak, all the way to the distributed denial-of-service (DDoS) attacks on U.S. government sites—with a lot in-between. A ...more
Anybody who spends most of their day on the internet should know all about lulz. Lulz are most often jokes made at the expense of web users, as popularized on 4Chan. Today, a consortium of hackers called LulzSec is attempting (and in some cases succeeding) in efforts to shut d ...more
Want the highest score on Bouncing Balls out of all of your friends? First step is to get Cheat Engine 5.5. Second step is to check out this video. Watch this video tutorial to learn how to get the highest score in Bouncing Balls (10/23/09). Download Cheat Engine 5.5 then you ...more
Bouncing Balls is one of those Facebook games that can be quite addicting to play. It's even more addicting to hack it. To do that, you need Cheat Engine, the ultimate flash game hacker. Watch this video tutorial to learn how to cheat on Bouncing Balls (09/28/09). There's not ...more
For as much money as they've made from North American video game audiences over the years, Japanese game developers don't seem to have very much faith in them. Dozens of great titles from their 40 years in the industry have appeared in Japan and across Europe, oftentimes even ...more
Warning Don't torrent things that you do not have the rights to torrent. Everything I torrent, I have a physical copy of, and just want a copy on my computer without causing wear-and-tear on my DVD drive's laser. Piracy is naughty. I used to get extremely frustrated with Bit ...more
At first, it seemed like a clever art installation housed on the web, but now we're not so sure... the Newstweek hack may indeed be legit. Earlier this year, Newstweek claimed to have developed a way to hack into webpages on a local Wi-Fi network using a homemade device that ...more
Our hacked Kinect series has demonstrated amply how the Kinect is changing the worlds of business, art, medicine and robotics. But where does it go from here? That will be determined by the thousands of dedicated DIYers out there doing work like you've seen here over the last ...more
As a kid, my favorite thing to do at the Natural History museum was a midday stop, when my family strolled past an antiquated looking vending machine in the museum's musty basement. The Mold-A-Rama machine was oddly shaped, George Jetson-esque, and spewed out made-to-order, br ...more
Last Friday's mission was to accomplish solving HackThisSite, realistic 2. This second mission in a series of realistic simulation missions was designed to be exactly like situations you may encounter in the real world, requesting we help a friend take down a racist hate-group ...more
Shortening URLs has become a necessity in this age of Twitter and limited-character status updates. It not only allows us to cram more words into our oh-so-important Twitter statuses, but it also helps us with a few other things. Some Benefits of URL Shorteners We can create ...more
Are you one of countless Facebook users who find the classic Thumbs Up symbol tiresomely sycophantic? You're not alone. Back in August of 2010, the widespread addition of an "official" Thumbs Down symbol to Facebook pages quickly revealed itself to be a scam, but only after co ...more
Today's post is a small go-to guide for beginner programmers in Null Byte. With many of our community members picking up programming from our Community Bytes, it only makes sense to lay out a one-stop guide for your reference. Hopefully this guide will help you make an educate ...more
We've talked about the deep web before, but we never really covered the details of what's out there. It occurred to me that a nice list of resources would be very helpful to all of you anons out there. Think of this like a helpful brochure to the hidden web. However, I should ...more
Brainwashing is something that happens to us every day, whether you believe it or not. It doesn't take fancy tools or space-age technology. Even if our country didn't intentionally brainwash people (believe me, they do), our country's media is brainwashing people nonstop. Just ...more
Yes, you read the title correctly. GameStop has problems, and if you're lax in morals, you can take advantage of them for free games and cash. I'm bringing you all yet another exclusive Null Byte that falls into the fascinating category of life hacking. If you do not like wha ...more
Welcome to the Google+ Insider's Guide to all things Google+. We're dedicated to keeping you updated with all the latest news, tips and tricks on Google+, and this official index will serve as a one-stop catalog of all our How-To articles, as well as all the news & updates we' ...more
If you follow the Anonymous, Occupy, and IT security scenes, you have no doubt heard about a dox release. What is it? How can it hurt you? And most importantly, how can you protect yourself from it? Some of these steps might seem common sense, while others will be an ah-ha! mo ...more
Use Cheat Engine to hack into the popular Bouncing Balls game. It's as easy as that. It's not too hard to use Cheat Engine if you've never before, then… flash game hacking everywhere! Watch this video tutorial to learn how to cheat Bouncing Balls (10/11/09). Download Cheat En ...more
Put a group or a small number of people in sauna, make sure it's nice and warm. Then open up the door and spray pepper spray(Fox Brand) in the eyes and bodies of the people inside. The heat will increase the pain of the pepper spray, after they snot and hack and gag on it for ...more
New statements from Apple make it clear that they do not believe a hacker, or group of hackers, breached any of their systems. This comes after a recent report from Motherboard that a hacker gang called the "Turkish Crime Family" is threatening to remotely wipe up to 559 milli ...more
Thanks to its encrypted messaging, WhatsApp can be a platform for secure communication with friends and family. One drawback, however, is that the app would let anyone add you to a group chat, regardless of if you approved it or not. This lack of control over your own account ...more
Group chats in WhatsApp are great for communicating with multiple people at once, but that can be a blessing and a curse — any message you send will be seen by everyone, and that's not always ideal. Thankfully, there's a new feature that lets you respond to group messages priv ...more
Mobile phones are not only essential for work and communication, they're quickly becoming an integral asset to our health. Your iPhone can store valuable data about fitness, nutrition, heart health, and so much more. And since iOS 11.3, your iPhone can even import a list of al ...more
Music has always been able to connect us. Spotify is now offering an innovative new way to do just that. The company announced today that they have launched a new feature in collaboration with the Messenger app that allows you to share and make playlists with friends. The fea ...more
Rumor has it that a gang of hackers—or possibly, one lonesome individual—holds the power to remotely wipe millions of iPhones and iCloud accounts, unless Apple coughs up some ransom money by April 7. The gang calls themselves the "Turkish Crime Family," and they're demanding ...more
From time immemorial, human beings seem to be at odds with one another. When these differences become so heated and unresolvable, it eventually erodes into physical violence. This violence has manifested into some of the most horrific exercises in human history, things which e ...more