Welcome back, my budding hackers! In previous tutorials, we've looked at some of the basic commands and concepts for using Linux. Along the way, I realized that I've failed to provide you with some basic background material on the stdin, stdout, and stderror. In human langua ...more
The one thing that separates a script kiddy from a legitimate hacker or security professional is the ability to program. Script kiddies use other people's tools, while hackers and security pros write their own tools. To that end, we're going to see how a stack overflow vulnera ...more
In this video, the instructor shows how to convert Celsius to Fahrenheit using a C++ program. This video shows how to do this by a live example where the instructor writes down the code to do it. First, code the basic structure of a c++ program that contains the include and al ...more
Analysis of photographs and social connections can be a huge component of social engineering. Understanding who a person is, as well as who they know, can establish links within a company. This information could be used by hackers to execute elaborate social engineering attack ...more
After a long hiatus, we shall once again emerge from the shadowy depths of the internet to build an exploit. This time, we'll be looking at how to defeat a non-executable stack by using the ret2libc technique — a lean, mean, and brilliant way of exploiting a stack overflow vul ...more
PowerShell is an essential component of any Windows environment and can be a powerful tool in the hands of a hacker. During post-exploitation, PowerShell scripts can make privilege escalation and pivoting a breeze, but its execution policy can put a damper on even the best-lai ...more
Hi nullbytes! I've been recently reading the whole Linux Basics for the Aspiring Hacker series and felt like it was missing some stuff I know, so I felt like sharing it with anyone who might find it useful too. Apt-Get I wonder why this was omitted in Chapter 5, apt-get is a ...more
Web application vulnerabilities are one of the most crucial points of consideration in any penetration test or security evaluation. While some security areas require a home network or computer for testing, creating a test website to learn web app security requires a slightly d ...more
Being able to write your own hacking tools is what separates the script kiddies from the legendary hackers. While this can take many forms, one of the most coveted skills in hacking is the ability to dig through the binary files of a program and identify vulnerabilities at the ...more
If you've ever had a little trouble trying to program your calculator, you may find a little relief with this four-part video tutorial. Here, a Texas Instruments (TI-84 Plus) calculator will be used to explain the programming process. The four parts include: 1: The Basics 2: ...more
I love making beeps and bloops with the Arduino pitches library, but sometimes archaic 8-bit tunes just don't cut it. Whether you want your robot to terrify your enemies with a demonic synthetic voice, you just need a pocket boom box on the go, or you want to a miniature guita ...more
Bucky from The New Boston serves up this Python video tutorial on how to program raw input in Python. This is the program you use to write all of your Python code down. Fun with input versus raw input! Python is a dynamic, object-oriented, high-level, programming language tha ...more
Want to learn how to broadcast live & record from your game console while viewing game-play in HD - using the BlitzBox B1-HD (for under $100). THis is an easy way to record your PS3, PS2, XBOX 360 or Wii games. The BlitzBox B1-HD features a built-in video capture card. The B1 ...more
Written by JD Coverly of WonderHowTo World, LoadSave:We've spent the last week with Sprint's new phone, the HTC Evo 4G. Specification wise, it's better than Verizon's Incredible and T-Mobile's HD2. Apple has unveiled the new version of their phone this week and thankfully it's ...more
In this video the teacher shows us how to use a TI-84 plus graphing calculator to graph a function, adjust the view window, and determine the values of several types of critical points on the graph such as x-intercept, y-intercept, local maximums, and local minimums. After ent ...more
This easy to follow silent and accurate video will guide you quickly and easily through what you'll need, (like a Power Supply, a sound system that has a Subwoofer Pre-output and a High Input adapter, which may already come with your amp.) First learn what colored wires should ...more
In this video, you will learn how to record using Apple Logic Pro 9. First, open the program and save the session. Make sure your audio interface is set before recording. Go to global settings and navigate to audio. Click on the general tab and change the audio settings. Wave ...more
In this article, I'll show you how to make a simple touch-triggered switch. This is very useful for various electronic projects, from a simple bedside light to a flat panel touch keyboard. The circuit can vary in switching power depending on the transistors you use. For exampl ...more
Smartphones are crazy awesome. You can do your banking, track your children, find directions, and even pretend to have a mustache. The only thing that these personal supercomputers are missing is physical interaction with the environment. I wanted to be able to call my house ...more
It was brought up a while back in a Community Call to Arms that *math* is handy for encryption (and let's face it, everything) so let us go over things you just have to know. "In its simplest meaning in mathematics and logic, an operation is an action or procedure which produc ...more
Last week I had a quick look at V.I.K.T.O.R, the anthropomorphized automated editing app that lives on your iPhone, and today it’s time to put it to work. There’s a powerful idea at the center of V.I.K.T.O.R. Our mobile devices make it absurdly easy to shoot high quality vide ...more
Before you go running off to the Apple store, you may want to educate yourself. DVICE is kind enough to compile the 20 biggest complaints about the iPad from a whole slew of reviewers. 1. Upscaling makes old iPhone/iPod Touch apps ugly. "Here's the problem: It looks terrible ...more
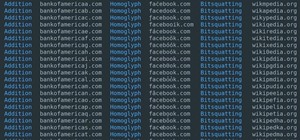
No doubt you've seen some of the hack logs being released. One part that stands out over and over again is the heavy database usage. It used to be early on that virus and hackers would destroy data, usually just for lulz. However, with the explosive commercial growth of the In ...more
SCRABBLE. I miss it. That idiosyncratic smell of cardboard, cheap wood and plastic that rushes out when I remove the box's cover. The instant gratification of unfolding the board into the sweet spot of the table, smoothing it out into the perfect receptacle for a heated battl ...more
The $35 Raspberry Pi is an amazingly useful single-board computer (SBC) with a good balance of price, performance, and connectivity options. But for some projects, it just isn't enough. Whether you need more computing power, a smaller size, or better machine-learning capabilit ...more
Back in July, Google rolled out a new design for the web version of Gmail. The rollout included new features alongside the visual changes, one of which being Confidential Mode. This new privacy-centric feature has now finally arrived on the mobile app version of the service, a ...more
I can't say that my handwriting skills are the best, and my cursive is even worse. I mean, I still don't know how to write a capital L in cursive, but who really cares when I do all my everyday writing with a keyboard now. I've gotten pretty fast at typing on my computer, but ...more
Ever since the announcement of the Razer Phone, a wave of gaming smartphones started to hit the market. With ASUS being such a big name in gaming, it made sense for them to throw their hat in the ring. The result is the ROG Phone. And with this first try, ASUS has topped the r ...more
There's actually more to the dialer screen on your OnePlus than meets the eye. Besides its obvious purpose of calling people, there's a vast array of secret codes that you can input to troubleshoot your device, in addition to revealing important information, making anonymous p ...more
Now that we've officially seen the HoloLens 2 and Microsoft has shown off the improvements and new superpowers of the augmented reality headset, what about the specs? Luckily, Microsoft has laid bare the full specifications for its next-generation headset. Let's dive in and s ...more
When it comes to note-taking, Google Keep is one of the most diverse and functional applications on the Android platform. Sure, there are a plethora of other note-taking apps to choose from, such as ever popular OneNote and Evernote, but Google Keep differentiates itself from ...more
Welcome back! In the last training session we covered how to write and execute scripts. But today we'll be getting back to the code! Today we'll be covering something that is extremely important for building real-life applicable scripts, file input and output. When I say "... ...more
Hi everyone! In the previous part of this series we introduced remote code arbitrary execution via buffer overflows using all of our past experiences. As I said back then, today I'll be explaining the other way you may use to redirect execution flow: using a NOP sled, along ...more
There seems to be no end to all the viral TikTok sound bites and trending TikTok songs, and there's a good reason why they are ingrained in the fabric of our pop culture. TikTok's short audio clips can evoke laughter, tears, and a wide range of other emotions, and many of them ...more
Here at Next Reality, our typical approach to all things augmented reality involves vision combined with remote control, either via a handheld device, gaze control, or hand/finger tracking. But a new dynamic takes the notion of interaction with virtual content into a new real ...more
Using a strong password is critical to the security of your online accounts. However, according to Dashlane, US users hold an average of 130 different accounts. Memorizing strong passwords for that many accounts is impractical. Fortunately, password managers solve the problem. ...more
The absence of a physical keyboard is both a gift and a curse. When it was announced in 2007 that the first iPhone would have a touchscreen only, people literally lost their shit. Now, almost 7 years later, you'd be hard-pressed to find a smartphone that still has a physical k ...more
With group chats, arguments tend to devolve from a dispute between two people to a giant debate amongst all members. But before things get out of control, Telegram has a feature that can help. You can now create polls in group chats. Any member can make one and users can vote ...more
We last saw China-based augmented and virtual reality headset maker Shadow Technologies at last year's Augmented World Expo, where they had the Action One, one of the wildest augmented reality headsets we've seen, on display. This week, the company re-emerged with Shadow Air, ...more
Hacker's are always looking for new ways to exploit systems and exfiltrate passwords, even in hashed form. Sophisticated brute-force attacks powered by high-end GPUs can perform millions of password attempts per second. But Ubuntu and Debian users aren't completely helpless. T ...more
Just because Developer Options is hidden by default doesn't mean you shouldn't unlock it. While for rooters its benefit are obvious, even for the average user it opens the door for tools which enhance your experience. From animation speed to improving gaming graphics, Develope ...more
Whether you're a veteran augmented reality developer looking for a quick access point to add a new platform to your arsenal or just getting started with your first AR head-mounted display, get ready to start developing for the Meta 2. In this short breakdown, we'll use the Un ...more
More proof is emerging that the iPhone 7 won't include a 3.5 mm headphone jack, and damn—it is not pretty. These third-party Lightning-to-3.5 mm dongles were spotted on Chinese site Tama, and they give us a glimpse into a horrifying future in which we have to attach one of the ...more
Similar to the feature that lets you dim the light on your PS4's DualShock controller, your Playstation 4 is filled with useful tricks that you may not know about, especially when all you want to do is pick up and play. One of these useful tricks is the ability to turn your TV ...more
If you haven't read the last article, feel free to stop by and give it a read, but abstaining from reading it will not, for the most part, be detrimental to your understanding. Today we are going to explore some of the inner workings of Bitcoin. As we previously learned in th ...more
There are many ways to take a screenshot in macOS (previously Mac OS X), but all of the well-known options give you a drop shadow in the picture when snapping application windows. If you use the Command Shift 3 shortcut, it takes a screenshot of the entire screen. If you use ...more
Cropping images can be a huge pain if you have a bunch to do at once. Even if you have Photoshop or a similar program, the process of opening each individual photo and cropping them one at a time can take forever. A free web-app called Cropp.me makes that task a lot easier by ...more
The iPhone XR has touched down alongside the XS and XS Max, and it utilizes tried and tested materials found on the iPhone 8, while being molded in the same vein as the iPhone X. The budget-friendlier flagship comes with its own set of design elements to set it apart from its ...more
During Google Developer Days, taking place now at the ICE Congress Center in Krakow, Poland, an introductory session on ARCore provides some insights on how the platform operates. The presentation by Googler Tom Slater includes an overview on the three pillars by which ARCore ...more
Have you ever used an open wifi, which after you connect displays a website to enter your credentials to get internet? That website is called captive portal and widely used in airports, hotels, universities etc. Have you ever wondered what would happen if someone would set up ...more
Mobile gaming has exploded in recent years, with experts predicting 2.4 billion global mobile players by the end of 2019. It already accounts for 47% of the worldwide gaming market, besting console and PC. No wonder we've seen the rise of gaming smartphones, a class of phones ...more
Undo. Redo. These two actions are forever intertwined, but they're missing from the standard keyboard on Android. Accidentally delete a word, and there is no Ctrl + Z to undo this mistake. But there is finally a solution available on Samsung Galaxy phones. Now, if you acciden ...more
Last week, I updated VirtualBox on my computer since I had skipped a few versions, then I could no longer copy text or paste text from my Kali virtual machine to my host OS and vice versa. Installing the Guest Additions didn't seem to do anything, and the bidirectional shared ...more
Unsurprisingly, Google wants to be the caretaker for augmented reality on the web, and its latest move in this endeavor is a 3D model viewer prototype called Article that's designed to work across all web browsers. On traditional desktop PCs and mobile browsers, Article can e ...more
Over the years, the internet has become a dangerous place. As its popularity has increased, it has attracted more hackers looking to make a quick buck. However, as our dependency on the web grows, it becomes increasingly difficult to sever all ties. This means we have to prote ...more
Vuzix Corporation has lifted the preorder status on its M300 Smart Glasses, making the augmented reality device available for purchase by resellers, registered developers, enterprises, and consumers. The M300 is targeted for business use-cases, particularly industrial, constr ...more
With the US Department of Homeland Security (DHS) banning laptops and tablets on flights originating from 10 international airports, and the United Kingdom taking similar precautions, international travelers are faced with hours of non-productive — or far less entertaining — f ...more
If you're an Android fan, you're probably familiar with Qualcomm's Quick Charge technology or, at the very least, what it can do. Quick Charge 3.0, the third generation of Qualcomm's fast-charging technology, is built into most Snapdragon SoCs and it's what lets you charge you ...more
Master Lock combination padlocks have been known to be vulnerable to an attack that reduces their 64,000 possible combinations down to 100. I've devised a new attack for cracking any Master combo lock that simplifies the process and reduces the amount of work down to only 8 co ...more
When you send an emoji from your Android device to someone that uses an iPhone, they don't see the same smiley that you do. And while there is a cross-platform standard for emojis, these don't work the same way as unicode-based smilies or dongers, so not every operating system ...more