Welcome back, my hacker apprentices! A you know, Mr. Robot is my favorite TV show this year, and not just for the realistic hacking. Rami Malek, the actor who plays Elliot, is incomparable in his depiction of a young man with social anxiety who is alienated from a superficial ...more
Tired of all those people tagging you in weird stuff on Instagram? Well, there's an easy way to prevent people from ever tagging you in one of those silly posts again. It's simple, too. It only takes a couple minutes of your time, but will probably save you from years of embar ...more
Smartphones are like high tech buckets that collect our personal information through constant use. This has some obvious benefits, like getting a more personalized experience with our devices. On the other hand, this data is a tempting target for bad actors looking to make a b ...more
Believe it or not, there are some older iPhones still in use out there, and they're not going away anytime soon. Sure, Apple would prefer you to upgrade your device to the latest and greatest models, which are compatible with iOS 5. Those models include all of the following: ...more
A boring work meeting. A conversation with someone you don't like. A date that's going horribly. A run-in with an aggressive and intimidating stranger. These are all situations where you want to flee—and fast. The most common way to make your exit look more legit is with a ph ...more
Some people (including myself) are seeing a "Hold" button instead of the "FaceTime" button when calling people on our new iPhone 4. It turns out this problem comes from a bug where Apple disables FaceTime on the iPhone 4 if you restored from an iPhone 3G. To get your missing ...more
Third-party ROMs like CyanogenMod are the ultimate form of customization for softModders. Hard-working developers offer us alternate Android experiences to replace our often bloatware-riddled stock ROMs. Installing custom ROMs is performed with a special type of software call ...more
While it's easy enough to take a screenshot of an end-to-end encrypted Telegram chat thread using an iPhone, it's an entirely different story on Android phones. Telegram disables screenshots for Secret Chats by default on Android, and not everyone can turn it on. Sometime in ...more
Your smartphone is the perfect place to watch Hulu on the go. Whether you're looking to catch up on your shows in a hotel, or your phone is the only screen available, mobile streaming can be a lifesaver. But what about when you have access to a TV? Wouldn't you rather watch yo ...more
As much as you try to safeguard your personal information, you may have made a small mistake by giving your phone number to the wrong entity, and now you're being bombarded with dozens of spam calls every day. To help parse your call log and reject the proper numbers without a ...more
The lengths people will go to for a grilled cheese sandwich are amazing. They'll use irons, wafflemakers, or whatever appliance that produces enough heat to produce the perfect combination of golden, grilled bread and oozy, melting cheese. I personally favor my cast-iron skill ...more
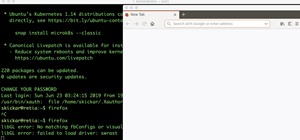
No more carrying around heavy laptops and thousands of Linux Live CDs and USBs to always be ready for pentesting on the fly! I hope you had a good Christmas and happy new year! Update1: Added the section "weaponizing your Android" where I talk about apps and fundamental Kali ...more
Ever since the update that turned Google Keyboard into Gboard rolled out, a lot of people have been noticing that word suggestions and auto-correct features are downright slow. The issue seems to affect users with multiple languages installed more than anyone, though it can al ...more
Changing your wallpaper and downloading icon packs is nothing new to the HTC One, but some people will go overboard with remapped keys, icon layouts on custom grids, and extensive wallpaper cropping—processes that could take hours to get just right. Now you can go overboard t ...more
Minecart rides primarily serve two different functions—transportation or entertainment. We rarely see minecart-based transportation systems in Minecraft these days because most servers support warps or allow users to set multiple homes that they can simply teleport to. That le ...more
With over a billion videos uploaded to YouTube, passing your time browsing through the immense library can be an emotional roller coaster ride. One second you're bawling your eyes out over this devastatingly sad clip of Oden the dog's last minutes with his owner, and the next ...more
There are a surprising number of hidden features in your iPhone's Phone app, from secret dialer codes that provide info or perform actions to special characters that dial extensions automatically. However, there's one little-known trick every iPhone owner should know when usin ...more
Look, I'm no food snob. I once dedicated an entire day to eating only deep-fried things (butter, Twinkies, Oreos, pickles) at the Minnesota State Fair. But even I draw the line at instant mashed potatoes. I mean, why bother? It's not that hard to make perfectly delicious and f ...more
If maintaining privacy is an ongoing battle, the front line is your smartphone. Apple included several new security features in iOS 10, but at the same time, some of the best new functionality comes with potential privacy trade-offs that everyone needs to understand. New feat ...more
I love YouTube for listening to music I don't already have on my phone or in my iTunes library, but there is one very simple thing that you think they would've figured out by now—the ability to have your video continue to play outside of the app! While I understand the point ...more
Most of you probably have a set of blinds at home, the most popular being horizontal or vertical. They're great for keeping the sun out of your eyes and maintaining privacy, but unfortunately, each comes with its own set of problems. Horizontal slats are prone to kinking and ...more
Android has a single text file named build.prop that determines tons of various system-wide settings on your device. You need root access to edit this file, since it's stored on the system partition—but the various lines of codes it contains are actually fairly easy to interpr ...more
Why a PDF Portfolio? If you've been wanting to create a PDF (portable document format) portfolio for your photos, art or design work, or wanted to create a PDF magazine that can be read by anyone on the net, then this article will show you how to go about it. I created my PD ...more
Welcome to the Official Jackass 3D Prank Contest Submission Page Think you've got the wit and imagination to be a Jackass? Well, here's your chance. Johnny Knoxville and Jackass 3D crew are hosting the first ever Jackass 3D Prank Contest to celebrate the upcoming release of t ...more
The new iPhone 6 and 6 Plus are supposed to last a lot longer in your pocket with improved battery life, but that doesn't mean that iOS 8 will be that friendly on your older iPhone model. All of those awesome new features could be killing your battery, but with some simple twe ...more
While Google would like you to believe that Flash is incompatible on Android KitKat, there is a functional workaround that will get it up and running on your Samsung Galaxy Note 3's gorgeous screen in no time. You can't download Flash Player from the Play Store, but Adobe hos ...more
Thanks to a newly discovered iOS exploit, a text message can now ruin your day. It will literally cripple your iPhone, and the worst thing is that anyone with a phone that supports double-byte unicode can do it to you. While it initially sounded like bullshit, we tried it out ...more
To serve as a framework for the "Nexus Imprint" feature in their new Nexus 5X and Nexus 6P smartphones, Google added native fingerprint scanner support to Android 6.0. Sure, Android devices have had fingerprint scanners in the past, but this is a unified, system-wide implement ...more
Of all the places you'd think to check for bed bugs, I doubt that library books would be at the top of your list. As odd as it sounds, though, libraries and library books are some of the most common places for bed bug infestations. Libraries all over the country have reported ...more
RouterSploit is a powerful exploit framework similar to Metasploit, working to quickly identify and exploit common vulnerabilities in routers. And guess what. It can be run on most Android devices. I initially covered RouterSploit on Kali Linux and macOS (OS X), but this tuto ...more
When you can't think of a way to respond in Messenger with words, emojis and stickers will do the trick. Since Facebook is all about the "likes," which use a thumbs-up icon, there's a shortcut to the symbol just to the right of the chat field. It's always there to send a quick ...more
Briefing Playing cards are used to play Killer but Killer is not exactly a card game. You cannot play this game if you do not know how to wink. I do not recommend that you go about winking at men and women to practice for this game. A minimum of 4 players are required to pla ...more
After finding and monitoring nearby wireless access points and devices connected to them, hackers can use this information to bypass some types of security, like the kind used for Wi-Fi hotspots in coffee shops, hotels, and in flights high above the ground. By swapping their M ...more
When you don't have anyone to play with in the flesh, nothing beats a round of competitive online Scrabble. If you're constantly on the move, the Scrabble app developed by Electronic Arts (EA) for Android and iOS mobile devices is probably your favorite way to play. But let's ...more
There's nothing wrong with indulging in guilty pleasures on Spotify every once in a while — we all need a little Coldplay and Creed in our lives. The only problem is, all of your friends and family might be watching. Anyone that is following your Spotify account can potentiall ...more
Coinbase is the primary go-to for many users when it comes to investing in Bitcoin (BTC), Ethereum (ETH), Litecoin (LTC), Ripple (XRP), and more, due to its user-friendly interface. But before you join them, know that the ease of use comes with a price. Coinbase charges fees f ...more
A warning to all of you iPhone users with parents, significant others, and nosy friends: Private Mode in the Safari browser isn't as private as you think. At least, not as private as it used to be back in iOS 7. Video: . Don't Miss: The 5 Best Hidden Safari Features in iOS 8 f ...more
There's no shortage of ice cream recipes out there, but one ice cream shop in London has found a unique recipe to sell to its customers, and of course it's controversial—breast milk ice cream. The Icecreamists make the ice cream from donated breast milk, straight from healthy ...more
Withstanding an attack from a motivated hacker is one of the most important responsibilities a system administrator must undertake. This is especially true for websites that may contain sensitive customer information and a high volume of users. So it's important for a sysadmin ...more
If you've just finally updated to iOS 10, you'll notice that lots of things have changed, and while the vast majority of new features are useful and fun, some can be a bit annoying. One bothersome bit of functionality is how Spotlight Search keeps a running history of everythi ...more
If you keep sensitive data on your phone, you've surely considered a "lockout" app before. There are many such apps that can add an extra layer of security to other apps within Android. For instance, you can require a PIN or password before anyone is able to launch a particula ...more
Pyrit is one of the most powerful WPA/WPA2 cracking tools in a hacker's arsenal, with the ability to benchmark a computer's CPU speeds, analyze capture files for crackable handshakes, and even tap into GPU password-cracking power. To demonstrate how quickly it can hack a WPA/W ...more
The buttons on most Android devices are laid out (from left to right) in a Back, Home, Recent Apps format. Samsung is the lone exception to this rule, which flip-flops them, so this can make for an inconsistent experience if you own multiple Android devices. But thanks to a f ...more
Ramen has always been a go-to meal for frugal foodies, college students, and anyone else who loves a soothing, cheap, and easy meal. And while instant ramen is delicious (and can easily be improved), making a simple homemade ramen is even better, and nearly as easy. Most peop ...more
According to WitsView, 8-inch displays will rule the tablet scene this year at 11.9% market share, compared to yesteryear's 2.6% market share. By year's end, it'll be almost 18%. Apple broke the trend for smaller 7-inch tablets with their iPad mini, which is just under 8-inch ...more
You want learn how to fire breath? This how-to video has 6 easy steps that anyone can do and it's safe. You need corn starch, water and a flame. Watch this video tutorial and learn how to breathe fire. You'll be able to find work as a carnie in these tough economic times.
An awesome new feature appeared in iOS 11 that lets you easily share your Wi-Fi password to anyone else with iOS 11 or higher just by tapping "Share Password" on your iPhone when they try to connect to the same network. However, if your friend is using Android or another mobil ...more
Anyone who has rooted their Android device has likely used a tool called Android Debug Bridge, better known as ADB, at some point during the process. For most, that is their only interaction with the ADB, but to be a true Android power user, you need to really know the tools a ...more
Ever accidentally sent an audio message to someone through the Messages app? It happens to me all the time. My finger slips towards the right side of the keyboard and all of a sudden a one-second audio recording is being made and sent. Personally, I don't even send audio messa ...more
Hackers often find fascinating files in the most ordinary of places, one of those being FTP servers. Sometimes, luck will prevail, and anonymous logins will be enabled, meaning anyone can just log in. But more often than not, a valid username and password will be required. But ...more
For all those times when an app either isn't available or simply won't cut it, your phone's internet browser provides access to your favorite websites and services. But some browsers are flat-out better than others, and chances are, the browser that came pre-installed on your ...more
There are a ton of new features in iOS 11, but some of the best ones, in my opinion, are in the Camera app. They're not huge features, but they're much appreciated to anyone who's ever taken a Live Photo or portrait, or even to those who've needed to scan a QR code quickly. W ...more
Sharing pictures from Google Photos by sending a link saves time because you don't have to download the image from Google, then reupload it somewhere else. But anyone who has your link can access your pictures, and baked into every file is metadata that you may not want prying ...more
A man-in-the-middle attack places you between your target and the internet, pretending to be a Wi-Fi network while secretly inspecting every packet that flows through the connection. The WiFi-Pumpkin is a rogue AP framework to easily create these fake networks, all while forwa ...more
Apple's latest big software update includes an entirely new Apple app, a controversial change in the TV app, better Siri control, an improved Shortcuts app, interesting Safari upgrades, Apple Music Sing, and more. Keep reading to see what iOS 16.2 has to offer your iPhone. Th ...more
Fire. It’s everywhere— always has been. From the Ordovician Period where the first fossil record of fire appears to the present day everyday uses of the Holocene. Today, we abundantly create flames (intentionally or unintentionally) in power plants, extractive metallurgy, i ...more
By now, you probably know that your iPhone secretly tracks and stores the locations you've visited in a backup folder on your computer's hard drive. The files are unencrypted, which means anyone with access to your computer or device can retrieve the information, which is down ...more
MAC addresses (not to be confused with Macs) are unique identifiers assigned to network devices in order to access the internet. Hotels use these Mac addresses in order to check if a registered patron has agreed to their terms and conditions, how much bandwidth is being consum ...more
Welcome back, my greenhorn hackers! Lately, much of the discussion here on Null Byte has revolved around evading detection and not getting caught hacking. Several of you have written me asking for a series on evading detection and forensics, and while I began a series 5 month ...more
When your computer first connects to a nework, it sends out a request on the network to lease an IP from the router. The router then leases your computer an unused IP address, which is used as a unique routing address for sending traffic that is meant for you, to you. As every ...more