How To : Block wireless phone spam
How to block wireless phone spam and stop getting unwanted text messages through Verizon wireless.

How to block wireless phone spam and stop getting unwanted text messages through Verizon wireless.
In this video tutorial, you'll learn how to configure scheduled blocking on your router. It's easy! So easy, in fact, that this home-computing how-to from the folks at Butterscotch can present a complete overview of the process in about three minutes' time. For details, and to ...more
Before you can use Xbox Live 360, you'll have to allow your console to use certain ports that, by default, it may be blocked from using. One way to open up those ports is with port triggering. This helpful home networking how-to will walk you through the process of getting tri ...more
Last year, Hasbro unveiled Scrabble Flash, an electronic version of the popular word game which consists of five SmartLink letter tiles that can communicate with one another using near field communication (NFC) to spell and score words. It's an interesting (and fun) way to bui ...more
Looking for a guide on how to set up your Netgear wireless router to automatically send you email alerts when built-in blocks are triggered? This clip will show you how it's done. It's easy! So easy, that this video tutorial can present a complete, step-by-step overview of the ...more
In this how-to video, you will learn how to configure and change the settings of your wireless router. If you have a bt router, go to api.home. This will bring up your wireless ADSL configuration. Click on advanced to change the advanced settings. You must enter your user name ...more
This video is for XBOX360 users, and includes general suggestions for the types and models of headsets to use for the gaming system. The man on the screen giving advice is Michael Weezner, who says he is an "avid video gamer" and who has much experience about selling, buying a ...more
Minecraft may seem like a game for just hardcore gamers and computer nerds, but it's totally not. It can hook anyone and everyone, from casual gamers to online addicts to total newbies—it can even turn its users into serial killers. And now, Notch and his Mojang crew have made ...more
Cell phones companies are constantly claiming to have the best service in town; but more often than not your service will be patchy. Check out this tutorial for information on how to boost your phone's signal and get the best reception. You Will Need * A fully charged cell pho ...more
Leaving your wireless router at its default settings is a bad idea. The sad thing is, most people still do it. Once they've penetrated your network, hackers will change your router settings so they'll have an easy way back in. This allows them to change your network into a she ...more
Oh, LifeHacker, we love you. You've brought us so many handy HowTo's: Hack Wireless Internet, Bypass Blocked Websites, Convert a Laptop Into a Projector, Watch TV & Movies on the Web For Free, 10 Must-Know Google Privacy Settings, and more. And now, another great one: LifeHac ...more
There are so many hackers around these days, and they are becoming very smart. So smart that they have successfully taken down many government websites. The most recent attack was on the Department of Justice (DOJ). To read about the history of these hackers, check out Wikiped ...more
In the first part of this series, we learned about darknets, as well as how they came about. But these patches of forgotten Internet are not the oasis of free information you might think. Despite being hidden—or just harder to come across—these networks are no more safe then a ...more
Wireless networks. Nowadays, everyone uses 'em, but most don't secure 'em. On average, I can drive up and down any block in my city and find at least one or two open or semi-open networks on any given day. With some changed MAC addresses for good measure, an attacker can use y ...more
Wouldn't it be nice to just sit at your buddy's house, plug into his network, and see exactly what he's doing? What if it was as easy as that? What makes packet sniffers like Wireshark such potent tools is that a majority of local area networks (LANs) are based on the shared E ...more
While our smartphones are many things, one of their primary functions is to make calls. Many of us try to avoid ever having to make calls, but there are situations when it's a must, such as wishing your grandma happy Birthday or calling 911 — and in those times you want stella ...more
In recent years, unwanted calls have become a top priority for the FCC. In 2016, analysts estimated that US customers received over 2.4 billion robocalls per month. As a result, the FCC has provided carriers new tools to combat this problem. The Federal Communications Commiss ...more
Have you ever felt like you wanted to totally annihilate someone in Minecraft with a machine gun? Yeah, me, too. Thankfully, you can! The redstone machine gun, which I'll demonstrate, is essentially just a rapid pulsar attached to a dispenser full of arrows. This design has b ...more
Apple's iOS 13 has been available for beta testing since June, and the stable release pushed out to everyone on Thursday, Sept. 19. To help you make the most out of iOS 13 for iPhone, we've rounded up everything you'll want to know, whether a colossal feature, small settings c ...more
Huawei has been in a losing battle with the US government for around ten years, with the last year being the spike of Huawei's problems. Because of US pushback against some Chinese-based smartphone manufacturers due to security concerns, Huawei is hoping to limit its dependenc ...more
Welcome back, my nascent hackers! In previous tutorials for my Wi-Fi Hacking series, I have shown you how to crack WEP and WPA2 passwords, break a WPS PIN, and create Evil Twin and Rogue access points. In this continuation of the series, let's look at slightly different appro ...more
You'd think the ability to block calls from certain numbers would be built in to most phones by now, but that's certainly not the case with the iPhone. After dropping a few hundred bucks on a device, it'd be nice to be able to choose who you want to talk to, but beyond screen ...more
Not having internet sucks! We do a ton online these days, from working, shopping, studying, and collaborating, to watching fail videos and endlessly clicking through memes. But sometimes your mobile screen is just not big enough! So, wouldn't it be cool if you could use your ...more
Next to spam calls, few things are more annoying than being inundated with spam, scam, and smishing texts. Your iPhone's Messages app should be a place for your friends and family to stay in touch, not a minefield of phishing attacks, malicious links, and viruses. Luckily, the ...more
Android 11 is here. Prior to Google dropping the naming scheme, this would have been a dessert with an R name (maybe Rice Krispies Treat or Red Velvet Cake) — but nope, just plain ol' Android 11. And after months of betas and a global pandemic, it finally debuted a little over ...more
It doesn't really matter what kind of cell phone you have—battery life is one of the most important features for any electronic device. We've written tons of articles on how to get better battery life from your Android, iPhone, Kindle, and more, but we've never really covered ...more
For all the benefits 5G brings to cellular data, it isn't without weaknesses, the biggest being privacy. Yes, the latest standard comes with breakneck downloads speeds up to 4.3 Gbps, but at what cost? Like with all things on the internet, 5G devices open opportunities for bot ...more
Google has recently been pushing to replace the decades-old messaging technology we've been stuck with. SMS was never meant to handle the high-quality multimedia content we consume with our smartphones today, so in comes RCS, which is a universal platform that aims to change o ...more
It wouldn't be iPhone season without a new controversy. Chargegate, Apple's latest PR nightmare, is the name being used for charging issues on some iPhone XS and XS Max devices. If you plug in your iPhone at night — or whenever — then wake up or come back later and see that yo ...more
Hackers and makers are often grouped under the same label. While hackers draw on computer science skills to write programs and find bugs, makers use electrical engineering to create hardware prototypes from microprocessor boards like the Arduino. We'll exercise both sets of sk ...more
Wireless charging is pretty much ubiquitous among modern iPhones and Android smartphones, but the technology has brought a lot of clutter with it. If you desire the convenience of wireless charging, you've guaranteed that a charging pad or dock will be ever-present on your en ...more
There's actually more to the dialer screen on your OnePlus than meets the eye. Besides its obvious purpose of calling people, there's a vast array of secret codes that you can input to troubleshoot your device, in addition to revealing important information, making anonymous p ...more
Former Vice President Dick Cheney was so fearful of attacks, he had his heart defibrillator re-calibrated to block incoming wireless signals so that highly skilled hackers couldn't send him into cardiac arrest. If hackers could potentially kill by turning someone's own defibr ...more
When you don't have a steady cellular signal or immediate Wi-Fi access but need to communicate with others around you, you can set up an off-the-grid voice communications network using a Raspberry Pi and an Android app. There are apps such as Bridgefy that will create a mesh ...more
We are now in the age of 5G. Carriers worldwide are upgrading their networks to the newest standard for mobile, which will dramatically improve your phone experience. How? By giving it download speeds and latency that surpass Wi-Fi. But before you upgrade, there are few things ...more
There's a lot more to your iPhone's dialer screen than just entering phone numbers and hitting the green call button. It's not very obvious, but there are secret codes that you can enter on the dialer to find out information about your device, help troubleshoot issues, and mas ...more
Welcome back, my rookie hackers! As hackers, we are often faced with the hurdle of cryptography and encryption. In some cases, we use it to hide our actions and messages. Many applications and protocols use encryption to maintain confidentiality and integrity of data. To be a ...more
Headphone cords are one of those things we all deal with because it beats the alternative (no music). But they can be so obnoxious—they're always getting caught on things, and they seem to be perpetually tangled. If you have ear buds, you can make a simple a cord container to ...more
Anyone who has been within a block of any wireless brick and mortar store or tech conference in the last couple of years has no doubt seen banners, posters, and videos promoting 5G high-speed wireless services on the way. The last time I can remember a technology being so hyp ...more
On July 3, Apple pushed out iOS 13 developer beta 3 for iPhone, and there's a lot found hidden within. A new FaceTime setting, more Arcade details, full-page scrolling screenshots everywhere, a noise cancellation option in the Control Center, and a new markup tool — and that's ...more
There's a lot of misinformation about VPN services, and it stems from the fact that not all of them are created equal. Some focus on privacy, others on security, and a few VPNs are seemingly even purpose-built for the polar opposite: data collection. We made this guide to help ...more
It's finally out. After months of testing, iOS 13 is available to install on your iPhone, which means over 200+ new features you can use right now. The update, released on Sept. 19, can be installed over the air or from a restore image using iTunes in macOS Mojave and older or ...more
The first sneak peak of Android O is finally here. The developer preview promises more features, stabilization, and better performance, according to the Android Developers Blog. Furthermore, there's speculation that the latest operating system will be code-named "Android Oreo, ...more
Starting in Android 4.3, Google added some code to AOSP that tagged your internet traffic when you were running a mobile hotspot, which made it incredibly easy for carriers to block tethering if you didn't have it included in your plan. But as of Android 6.0, this "tether_dun_ ...more
Practically every kid in the '80s would rush home after school to put in some time on the first-gen Nintendo before their parents got home. Games like Super Mario Bros. and Super Smash Bros. were synonymous with fun times, and to this day, call up a wave of nostalgia amongst G ...more
Ever use an open hotspot on your Note 3, only to find out that it's severely restricted to what sites you can access? While getting online with free Wi-Fi is great for those who have a limited data plan, when that one site you absolutely need to visit is blocked, you're left f ...more
Why do we still need to plug in our phones to charge them? Wireless charging exists, and has for quite some time, but most manufacturers don't include it in their devices. When it comes to the Samsung Galaxy S4, you can buy a QI-compatible wireless charging kit, but between th ...more
UPDATE: The whitehouse petition has received enough signatures to require a response from the government. Your voices have been heard! Now we wait... The Man is always trying to hold you back, and when it comes to the government, it can be this biggest swag blocker of all. As ...more
If you upgrade to an iPhone 12, 12 mini, 12 Pro, or 12 Pro Max, you can take advantage of super-fast 5G speeds, but which 5G network are you actually getting and is it better than the others? Depending on your carrier, you may see 5G, 5G+, 5G UW, or 5G E in the status bar next ...more
Whether it's a short road trip or an 18-hour flight, our phones are now essential travel companions. No longer do we need a GPS unit, maps, cameras, camcorders, or even boarding passes. However, not all phones are created equal in this regard. Some are more suited for travelin ...more
Your social security number, credit card information, and medical history can fall into the wrong hands if you're not careful about how and where you share your data online. If you really care about your data, there are tools and techniques you can utilize to protect yourself ...more
Your iPhone is full of features, many of which you might not even know about yet. Still, Apple keeps adding feature after feature with each new iOS update, and iOS 14.5 is no exception. The latest iOS version adds at least 69 features for your iPhone that you should be happy a ...more
After installing Ubuntu as your primary OS, you should have protected against USB Rubber Ducky payloads, defended against hard drive forensics, and reduced the overall attack surface against physical strikes. When defending against network-based attacks, you'll want to minimiz ...more
2015 is quickly shaping up to be the year of the cord cutter, with various media companies finally warming up to the concept of offering live streaming content. In the wake of Dish Network announcing a streaming cable service called Sling TV and Sony unveiling a similar platfo ...more
Airports are terrible germ-infested purgatories where people sit around for hours without Wi-Fi while they anxiously await to get wherever they really want to go. Unfortunately, there isn't much we can do about waiting, but this little Wi-Fi hack could help make the waiting a ...more
Finally, the much-hyped Xbox One is out, setting the stage for an epic holiday showdown between Microsoft and Sony. While the PS4 was released a full week before the Xbox One, Microsoft's next generation system is fully equipped with the latest games and acts as an all-out med ...more
As 2009 comes to a close, the Telegraph presents a compilation of this past year's wackiest inventions. As always, here at WonderHowTo, we are inspired and impressed by ingenuity. The contraptions below range from utter silliness (engagement ring bra) to downright amazing (see ...more
Mobile gaming has exploded, with roughly $70 billion in revenue in 2019. This gave rise to the so-called gaming phone, headlined by names like Razer and ASUS. While the Galaxy S20, S20+, and S20 Ultra are being marketed as everyman devices, make no mistake — these are unstoppa ...more
Nearly every connection to the internet is dependent on the Domain Name System. DNS, as it's more commonly called, translates domain names like gadgethacks.com into IP addresses, which is what network devices use to route data. The problem with DNS servers is that they don't h ...more
Christmas is just one week before Jan. 1. That means a lot of New Year's resolutions filled with promises to better ourselves with increased productivity, focus, and work ethics — but getting started can be challenging. Give the people in your life a leg up this holiday season ...more
 How To:
15 iPhone Tips for Busy Users to Maximize Your Productivity
How To:
15 iPhone Tips for Busy Users to Maximize Your Productivity
 Home Screen Customization:
How to Hide and Show Specific Home Screen Pages on Your iPhone
Home Screen Customization:
How to Hide and Show Specific Home Screen Pages on Your iPhone
 How To:
Apple's Upcoming Repair Mode for iOS Makes Prepping Your iPhone to Be Fixed Easier and More Secure
How To:
Apple's Upcoming Repair Mode for iOS Makes Prepping Your iPhone to Be Fixed Easier and More Secure
 How To:
Make Your iPhone Do All Your Talking for You on Calls and in Person
How To:
Make Your iPhone Do All Your Talking for You on Calls and in Person
 How To:
Add Website Shortcuts to Your iPhone's Home Screen for Fast Access to Web Apps and Bookmarks
How To:
Add Website Shortcuts to Your iPhone's Home Screen for Fast Access to Web Apps and Bookmarks
 News:
Apple Pencil 3 Is Almost Here — And It Comes with Squeeze Gestures and These Other Features
News:
Apple Pencil 3 Is Almost Here — And It Comes with Squeeze Gestures and These Other Features
 How To:
The Messaging Trick You Never Knew You Needed
How To:
The Messaging Trick You Never Knew You Needed
 How To:
Customize and Use Control Center on Your iPhone for Quick Access to Your Most-Used Apps, Features, and Settings
How To:
Customize and Use Control Center on Your iPhone for Quick Access to Your Most-Used Apps, Features, and Settings
 How To:
11 Features Coming to Apple News on Your iPhone with iOS 17.5 — Including Some Big Ones!
How To:
11 Features Coming to Apple News on Your iPhone with iOS 17.5 — Including Some Big Ones!
 How To:
Apple's Integrating Game Center Leaderboards into News+ Puzzles with iOS 17.5
How To:
Apple's Integrating Game Center Leaderboards into News+ Puzzles with iOS 17.5
 How To:
Apple Has a Killer New Word Game Puzzle Called Quartiles Hiding on iOS 17.5
How To:
Apple Has a Killer New Word Game Puzzle Called Quartiles Hiding on iOS 17.5
 How To:
Identify Any Song Playing on Instagram, TikTok, and Other Apps on Your iPhone Using Shazam
How To:
Identify Any Song Playing on Instagram, TikTok, and Other Apps on Your iPhone Using Shazam
 How To:
Apple News Gives You More Options for Automatic Downloads on iOS 17.5
How To:
Apple News Gives You More Options for Automatic Downloads on iOS 17.5
 How To:
30 New Features and Changes Coming to Your iPhone with iOS 17.5
How To:
30 New Features and Changes Coming to Your iPhone with iOS 17.5
 How To:
Download and Install iOS 17.5 Beta on Your iPhone — And Try New Features Before Everyone Else
How To:
Download and Install iOS 17.5 Beta on Your iPhone — And Try New Features Before Everyone Else
 How To:
Download and Install iPadOS 17.5 Beta on Your iPhone to Explore New Features Before Everyone Else
How To:
Download and Install iPadOS 17.5 Beta on Your iPhone to Explore New Features Before Everyone Else
 How To:
Update Your iPhone's Lock Screen with an Attention-Grabbing Note, Reminder, Warning, or Other Custom Message
How To:
Update Your iPhone's Lock Screen with an Attention-Grabbing Note, Reminder, Warning, or Other Custom Message
 How To:
Your iCloud Email Lets You Create Aliases to Protect Your Primary Email Address and Organize Your Inbox
How To:
Your iCloud Email Lets You Create Aliases to Protect Your Primary Email Address and Organize Your Inbox
 How To:
Use Your iPhone's Built-in Image Analyzer to Reveal the Hidden Meaning Behind Symbols, Signs, and More
How To:
Use Your iPhone's Built-in Image Analyzer to Reveal the Hidden Meaning Behind Symbols, Signs, and More
 Text Replacements:
The Secret Weapon to Typing More with Less on Your iPhone, iPad, or Mac
Text Replacements:
The Secret Weapon to Typing More with Less on Your iPhone, iPad, or Mac
 How To:
Create an Admin User Account Using CMD Prompt (Windows)
How To:
Create an Admin User Account Using CMD Prompt (Windows)
 How To:
See Passwords for Wi-Fi Networks You've Connected Your Android Device To
How To:
See Passwords for Wi-Fi Networks You've Connected Your Android Device To
 How To:
15 iPhone Tips for Busy Users to Maximize Your Productivity
How To:
15 iPhone Tips for Busy Users to Maximize Your Productivity
 How To:
The Messaging Trick You Never Knew You Needed
How To:
The Messaging Trick You Never Knew You Needed
 How To:
Check if Your Wireless Network Adapter Supports Monitor Mode & Packet Injection
How To:
Check if Your Wireless Network Adapter Supports Monitor Mode & Packet Injection
 How To:
Crack Password-Protected Microsoft Office Files, Including Word Docs & Excel Spreadsheets
How To:
Crack Password-Protected Microsoft Office Files, Including Word Docs & Excel Spreadsheets
 How To:
Crack SSH Private Key Passwords with John the Ripper
How To:
Crack SSH Private Key Passwords with John the Ripper
 How To:
Scan for Vulnerabilities on Any Website Using Nikto
How To:
Scan for Vulnerabilities on Any Website Using Nikto
 How To:
Exploit EternalBlue on Windows Server with Metasploit
How To:
Exploit EternalBlue on Windows Server with Metasploit
 How To:
Here Are All the iPad Models iPadOS 17 Supports (And Doesn't Support)
How To:
Here Are All the iPad Models iPadOS 17 Supports (And Doesn't Support)
 How To:
Easily Detect CVEs with Nmap Scripts
How To:
Easily Detect CVEs with Nmap Scripts
 How To:
Use FaceTime's Secret Hand Gestures and Reaction Buttons to Add Animated On-Screen Effects to Your Video Feed
How To:
Use FaceTime's Secret Hand Gestures and Reaction Buttons to Add Animated On-Screen Effects to Your Video Feed
 How To:
The Trick That Lets You Link to Specific Start Times in YouTube Videos Right from Your Phone
How To:
The Trick That Lets You Link to Specific Start Times in YouTube Videos Right from Your Phone
 How To:
CC in a Physical Business Letter
How To:
CC in a Physical Business Letter
 How To:
Gain SSH Access to Servers by Brute-Forcing Credentials
How To:
Gain SSH Access to Servers by Brute-Forcing Credentials
 How to Hack Wi-Fi:
Stealing Wi-Fi Passwords with an Evil Twin Attack
How to Hack Wi-Fi:
Stealing Wi-Fi Passwords with an Evil Twin Attack
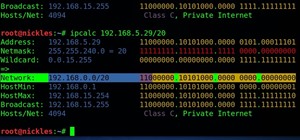 How To:
Understand & Use IPv4 to Navigate a Network
How To:
Understand & Use IPv4 to Navigate a Network
 How To:
Keep Your Night Vision Sharp with the iPhone's Hidden Red Screen
How To:
Keep Your Night Vision Sharp with the iPhone's Hidden Red Screen
 How To:
See What Traffic Will Be Like at a Specific Time with Google Maps
How To:
See What Traffic Will Be Like at a Specific Time with Google Maps
 How To:
Use Burp & FoxyProxy to Easily Switch Between Proxy Settings
How To:
Use Burp & FoxyProxy to Easily Switch Between Proxy Settings
 How To:
Dox Anyone
How To:
Dox Anyone
 How To:
Dial These Secret Codes to See if Someone Is Hijacking Calls & Texts on Your iPhone
How To:
Dial These Secret Codes to See if Someone Is Hijacking Calls & Texts on Your iPhone
 How To:
Make Spoofed Calls Using Any Phone Number You Want Right from Your Smartphone
How To:
Make Spoofed Calls Using Any Phone Number You Want Right from Your Smartphone
 How To:
Clone Any Android App on Your Samsung Galaxy Phone Without Using Any Third-Party Tools
How To:
Clone Any Android App on Your Samsung Galaxy Phone Without Using Any Third-Party Tools
 How To:
Find Vulnerable Webcams Across the Globe Using Shodan
How To:
Find Vulnerable Webcams Across the Globe Using Shodan
 How To:
Use Odin to Flash Samsung Galaxy Stock Firmware
How To:
Use Odin to Flash Samsung Galaxy Stock Firmware
 How To:
Make Your Own Bad USB
How To:
Make Your Own Bad USB
 Hack Like a Pro:
How to Find Directories in Websites Using DirBuster
Hack Like a Pro:
How to Find Directories in Websites Using DirBuster
 How To:
19 Harry Potter Spells Your Android Phone Can Cast Using Google Assistant
How To:
19 Harry Potter Spells Your Android Phone Can Cast Using Google Assistant
 How To:
Bypass File Upload Restrictions on Web Apps to Get a Shell
How To:
Bypass File Upload Restrictions on Web Apps to Get a Shell
 How To:
Perform Advanced Man-in-the-Middle Attacks with Xerosploit
How To:
Perform Advanced Man-in-the-Middle Attacks with Xerosploit
 How To:
Use SpiderFoot for OSINT Gathering
How To:
Use SpiderFoot for OSINT Gathering
 How To:
Turn Any Website into a Full-Screen App on Your iPhone
How To:
Turn Any Website into a Full-Screen App on Your iPhone
 TWRP 101:
How to Make a NANDroid Backup & Restore Your Entire Phone
TWRP 101:
How to Make a NANDroid Backup & Restore Your Entire Phone
 How To:
Find Out Whether Your Phone Has an LCD or AMOLED Display (& Why It Matters)
How To:
Find Out Whether Your Phone Has an LCD or AMOLED Display (& Why It Matters)
 How To:
Stop Your TikTok Account from Being Suggested to Contacts, Facebook Friends & Other Users You May Know
How To:
Stop Your TikTok Account from Being Suggested to Contacts, Facebook Friends & Other Users You May Know
 Google Photos 101:
How to Use Google Lens to Identify Landmarks in Your Images
Google Photos 101:
How to Use Google Lens to Identify Landmarks in Your Images
 VLC 101:
How to Stream Movies from Your Computer to Your Android Phone
VLC 101:
How to Stream Movies from Your Computer to Your Android Phone
 How To:
Set Your Wi-Fi Card's TX Power Higher Than 30 dBm
How To:
Set Your Wi-Fi Card's TX Power Higher Than 30 dBm
 How To:
Embed a Metasploit Payload in an Original .Apk File | Part 2 – Do It Manually
How To:
Embed a Metasploit Payload in an Original .Apk File | Part 2 – Do It Manually