Learn how to convince someone to go skinny-dipping. The trick to getting someone to skinny-dip with you is to make them think it's their idea. You Will Need * A smooth delivery * Persuasion skills * A smooth delivery * Persuasion skills Step 1. Praise their body Grease the ...more
With this video you'll be able to pull a prank on your friends, convincing them they're psychic! It's a great illusion that anyone can do. You'll need to watch the video and check out the accompanying link here. Tada!
Shaikh Yusuf Estes teaches parents the way to keep they're teenagers praying. While many parents think that bringing a child up a Muslim right when they can talk, the prophet has already said that the age of 7 is the age to teach a child how to pray. The more a child is genuin ...more
Are you a follower or a leader? No matter how you respond, we all know that leader is a more desirable position to hold. Great leaders typically share a few qualities—confidence, intelligence, and strength, to name a few—but one of the most intriguing is their appearance. With ...more
Ultimately a doctor’s note is the only necessary proof needed to show your boss that you really did go to the doctor’s but if you feel like making an airtight case you can always take a few extra steps to make sure there’s not a shadow of a doubt. Work for a scrooge who quest ...more
The best way to show your parents that you are ready to date is by being responsible. Document just how responsible you are and present them with possible, mind-easing dating options and you’ll be dating in no time. If you’re more than ready to start dating, but your parents ...more
Tired of walking everywhere? Does your only ride have two wheels and a bell? Check out this video and learn tips and tricks for convincing your parental units to buy you a car. Pretty soon you will be cruising through town and the envy of all your friends. You Will Need * Gas, ...more
For some reason these days, it seems like all the young people want to date old people and vice versa. If you find yourself on the young side of that equation, watch this video for some novel tips on convincing your parents to let you date an older man or woman.
Does your mom constantly harass your and try to nose her way into your business? You don't have to let her, and you also don't have to ruin your relationship. Watch this video for some tips on setting boundaries and living your own life while still loving your mother.
While there's an art to surviving the all-nighter, there's also an art to staying awake throughout the day when you're operating on little to no sleep. In 1964, the record for sleep deprivation was set by 17-year-old Randy Gardner, who stayed awake for an incredible 264 hours ...more
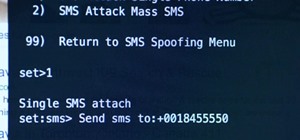
Spoofed phone calls originate from one source that's disguising its phone number as a different one, and you probably get these calls all the time. Maybe they're numbers from your local area code or for prominent businesses, but the callers are just hijacking those digits to f ...more
There are a lot of manipulative people out there, but you don't have to let all of them push you around. It's time for the tables to turn. You already know how to manipulate people, how to lie to them, and how to convince them that you're trustworthy, but what about when some ...more
You wouldn't send your GPS coordinates to a completely random stranger just because he or she asked you for it, right? So why are you constantly sharing your location (and other data) to apps on a daily basis? While there are many apps that need your location in order to func ...more
Open-source data scraping is an essential reconnaissance tool for government agencies and hackers alike, with big data turning our digital fingerprints into giant neon signs. The problem is no longer whether the right data exists, it's filtering it down to the exact answer you ...more
A powered-off Windows 10 laptop can be compromised in less than three minutes. With just a few keystrokes, it's possible for a hacker to remove all antivirus software, create a backdoor, and capture webcam images and passwords, among other highly sensitive personal data. The ...more
This is evil and it destroys people. Let's just get that out of the way. Nonetheless, suppose you need to make someone distrust their own memory and perception of reality. Suppose you want someone to believe in you more than they believe in themselves. Regardless of your mali ...more
Hello my fellow hackers, it's been a while since my last post, I can't get the time now-a-days for the posts but can manage to tend to comments. Welcome to my 9th post, this tutorial will explain how to extract and decrypt WhatsApp database from the Victim's android system. ...more
The art of persuasion (or subtle emotional manipulation, depending on how you're looking at it) does not necessarily have to be an evil thing. When you want to make an important sales pitch to a tough customer, propose a risky business plan at work, or gently convince your si ...more
When performing something such as a mass mailer attack on a company, sending executables usually isn't the best option. That's why, in this tutorial, I'll be teaching you how to code a VBA script macro into a Word document in order to compromise a system. Combined with a littl ...more
There are a ton of great new features in iOS 8, and one of the most interesting (and perplexing) ones is called "Family Sharing." By utilizing this feature, you are creating a continuity among all of the iOS devices in your family, granting members the ability to share apps, ...more
Lying is awesome. From a very young age, children learn that flat out denying the truth gets you out of trouble and helps keep you calm in the face of horror. But what happens when you just have to know if someone, say, used your toothbrush? You could ask them to take an expen ...more
Airgeddon is a multi-Bash network auditor capable of Wi-Fi jamming. This capability lets you target and disconnect devices from a wireless network, all without joining it. It runs on Kali, and we'll cover installing, configuring, and using its jamming functionalities on a smal ...more
I absolutely loathe it, and I'm certain I'm in the majority, yet we still do this nonsense every year. Take one day and make it to where every headline you read and every link you click are completely useless. Slap a bunch of corporate logos on last year's memes and pollute fe ...more
Well hello dear readers of Null byte, let me start off stating english is not my first language and they will be some grammar mistakes. This also is my first tutorial so don't hesitate to give me feedback :) You may have made a malicious apk (android package) before on kali, ...more
I've had a handlebar mustache for about five years now, and I've learned a lot over those years about how to grow and care for it. I will now share all of that information with you! Hopefully this will encourage you to grow one for Movember! The first thing I want to address r ...more
What if I told you that you could read minds? You'd most likely think I was crazy, and you'd be right. But what I really meant is that you could make people think that you could read minds, something that's not the least bit crazy. Performing mind reading — and it is a perfor ...more
It's no secret that devices leak data, but sometimes they do so in ways you may not expect. Your phone, laptop, printer, and IOT devices leak Wi-Fi information that can (and is) used to track you. Today, we'll make a Wi-Fi probe logger with Probemon.py to track nearby devices ...more
Last week, we discussed whether Google should require you to use your real name for Google+ profiles. Google is working on eliminating fake profiles, and in the process, they've booted some real people, including actor +William Shatner. If you find out that your Google+ accoun ...more
Instagram is all about sharing and interacting with others, but sometimes we hide in the shadows and lurk. Whether their ex-lovers, current crushes, former high school classmates, or future coworkers, we silently view their content without them knowing. You can deny it all you ...more
Once a hacker has created a PowerShell payload to evade antivirus software and set up msfconsole on their attack system, they can then move onto disguising their executable to make it appear as a regular text file. This is how they will get a Windows 10 users to actually open ...more
Last week, we explored nine signs to watch out for if you suspect that somebody is lying to you. In this week's slightly more evil edition, we present the flip side: eight sneaky tips for lying effectively. In a nutshell: don't act like a guilty liar. Maintain normal eye cont ...more
If you've ever needed to prove you have remote access to a device, or simply want a way to convince someone their computer is haunted, SSH can be used to make a device begin to show signs of being possessed. Spooky Action at a Distance If you need to prove you've got remote ...more
With an ordinary birthday card, we can introduce a physical device which contains malicious files into someone's home and deceive them into inserting the device into a computer. In my last series, we used a Post-it note to trick a neighbor into visiting a website that we cont ...more
While living alone, I grew to enjoy cooking. Not only was it necessary to my existence, but it was cheaper than eating out. One thing I really came to love was garlic, especially its smell. If a recipe didn't ask for it, I added it anyways. The only thing I hate about garlic ...more
Welcome to Minecraft World! Check out our tutorials, post to the community corkboard, and come play on our free server! Our previous workshop on building an automatic boat dock went really well. A lot of Minecrafters showed up and everyone got right to work on their own versi ...more
Defcon is the largest hacker conference with something for everyone, whether it be the talks, parties, villages, or any of the hundreds of events. In this guide, we'll take a holistic view at everything that goes into attending the con for the first time, from securing your el ...more
Mochi seems to be everywhere these days: as a topping at your local frozen yogurt shop, in ice cream balls (the green tea ones are heaven), and as colorful treats all over Instagram. It seems like mocha mania is in full force! Traditionally, it takes quite a bit of effort to ...more
Your brain holds a lot of precious information and is capable of great feats. However, there's one quality that doesn't lie among its strengths—memory security. Yes, that's right, your brain can be hacked, and it doesn't take a psychologist to do it. Anyone with the right know ...more
Biting into a perfectly ripened piece of fruit is enough to convince you to give up baked goods and plant your own garden. The combination of flavor, juice, and sweetness in a ripe mango, apple, plum, or berry is the stuff of life itself. Alas, most people don't know how to c ...more
Don't let the TV ads convince you to buy some bulky contraption that will gather dust in your closet, crunches are safe and effective! This how-to video shows how to do crunches with varying degrees of difficulty based on your ability. Remember that ab exercises alone will not ...more
Nice people finish first—or is it last? Though you may have been told throughout your life that being kind pays off, there are some obvious advantages to getting mean. So whether you're driving towards a goal at work, or need to attack a task in your personal life, acting like ...more
Halloween is a night to dress up as any character you'd like—but for women, that typically means wearing something skimpy or downright absurd. From "sexy" policewomen to nearly undressed fairy tale princesses, we're surrounded by costumes that leave little to the imagination. ...more
Accents are not only fun but attractive too, when done properly, at least. Work on your Irish accent, practicing the inflection and sound of consonants and vowels. Impress your friends with your new accent. You may have the luck of the Irish, but you’d better work on getting ...more
It's not easy staying fit and healthy these days with addicting phones, oversized portions, and long workdays, to name just a few things. To succeed, it takes work, commitment, and an understanding of your mind and body — and your iPhone can help you with some of that. While A ...more
At last, what you all finally waited for! Hi! Fire Crackers, Welcome to my 7th post (Part-3), this tutorial will explain about some situations and how to make the Victim's Life like Hell! And fill his system with Malware. #1 Situation: After Exploiting... Go ahead and explo ...more
Telemarketers can be as terrifying as a villain from a horror film. Your phone rings with an unknown 800 number, and you immediately fill with a sense of dread. There's no way to get them to stop calling; you imagine the number appearing on your phone at all hours of the day a ...more
First of all, I would like you all to meet my good friend Iggy. There he is, in all his scaly reptilian glory. As you can see, he spends a lot more time on top of his cage than inside of it. You see, Iggy here doesn't deal well AT ALL with confinement. I don't know if it's pos ...more
While hackers have taken advantage of numerous vulnerabilities in Adobe's products to deliver payloads to Windows users via PDF files, a malicious PDF file can also wreak havoc on a Mac that's using the default Preview app. So think twice before double-clicking a PDF open on y ...more
I love cryptography. It is like a great gigantic puzzle for me to solve. However, it is more important than that. It is also how we keep secrets safe. Not just sorta safe either, but really safe. Until recently, if you wanted to use strong encryption you had to either learn d ...more
Hacking can't be that hard, can it? At least, that's what it seems like thanks to movies like Hackers, The Net and that last Die Hard flick. Even the Jurassic Park girl's got some game. They all look like they're typing 20wpm, yet can generate a screen full of code in the blin ...more
Zombies are in, as always, and if you want to ride the wave of zombie madness this Halloween, check out this two-part video guide. It will teach you how to create really scary professional-looking zombie makeup for your face that will convince just about anyone you're out to e ...more
Smartphone manufacturers do their best to keep you tied down to their ecosystem, but the reality is that there's not much keeping you from switching. Transfer some files, install a few apps here and there, and all of a sudden, you're knee-deep in a new operating system. Don't ...more
No nets, no coins, no cards, no nothing! This magic trick is a fun one to do and only requires your hands, arms and an audience. Check it out and see how to convince your friends that your arms are made of rubber. Video: .
If you want to convince your friends that money is not an issue, then you can just burn it for real like Walter White. But if you don't really want to destroy your hard-earned cash, this burn trick is perfect for you. It just takes some basic chemistry and a few materials, suc ...more
Today I am going to teach the various ways that you can use social engineering to hack a system. For those of you that have followed my past tutorials, you know that social engineering can unlock a world of possibilities. This is because no matter how many firewalls, no matter ...more
The art of persuasion is a very crucial characteristic that anyone can learn, and it has countless benefits. Whether it's at work, home, or in social situations, the ability to be veritably persuasive can have an unheralded impact on your daily life. Convincing others to do y ...more
This year's biggest film certainly didn't come as a surprise: with another incredible comic book creation, Marvel's Guardians of the Galaxy wowed audiences more than any other movie. With its unique team of heroes, Guardians provided a set of ready-made Halloween costumes. Al ...more
There is a huge myth that most Americans believe, and it might be the marketing triumph of the 20th century. We pay an absurd markup (Zero Hedge says as much as 280,000% for "designer" water) on something we can get for free because most of us believe that bottled water is hea ...more
Instead of suffering through long, dull meetings with your supervisors and coworkers, you can turn those office table sessions into your very own psychological experiment. Using the tricks below, you'll be able to hack your verbal responses and physical movements to convince ...more
In these times of social distancing, video calling is becoming the technological substitute for face-to-face connections. For those who carry an iPhone, the art of video calling defaults to FaceTime, the native app on iOS that is exclusive to Apple devices. But what do you do ...more