Back in 2007, YouTube user HouseholdHacker posted a parody video on how to make a high-def speaker for under a buck. MythBusters took on the challenge and busted it. Although that particular method doesn't seem to work, that doesn't mean you can't make your own speaker for le ...more
It may not be as large as the Samsung Galaxy Note 2, but the Galaxy S3's screen size is still big enough to make iPhone owners cry themselves to sleep. The 4.8-inch AMOLED display with 720 x 1280 pixels makes the GS3 a great mobile companion—and an even better portable gaming ...more
One of the biggest advancements in the new iPhone XS, XS Max, and XR is the dual SIM functionality that will let you use two cellular networks at once. Like Sinatra, however, Apple is known to do things its own way, so their dual SIM setup is a bit different than you might thi ...more
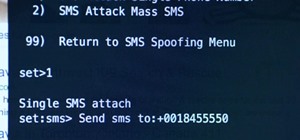
Hi, my name is Alan, and I am not a script kiddy brat from Xbox Live asking you how to boot someone offline for being mean to me. I am an amateur white hat hacker hoping to learn and teach and this is my first tutorial. THC Hydra is very prominent online brute-force tool and ...more
In this series, I'll be exploring electromagnetic weapons, how to build them, their function and application to the future, and the amazing possibilities electromagnetism has to offer. First, the electromagnetic pulse generator, or EMP. You've probably heard of these before, a ...more
Besside-ng is the hidden gem of the Aircrack-ng suite of Wi-Fi hacking tools. When run with a wireless network adapter capable of packet injection, Besside-ng can harvest WPA handshakes from any network with an active user — and crack WEP passwords outright. Unlike many tools, ...more
The passcode, or the four-digit code you enter in order to access an iPhone or iPod touch, was created to ensure security and prevent hacking. But what if you haven't touched your iPhone in a month and you simply don't remember what your passcode is anymore? Don't fret; just ...more
Electronic warfare tactics work by jamming, disrupting, or disabling the technology a target uses to perform a critical function, and IoT devices are especially vulnerable to attacks. Wireless security cameras like the Nest Cam are frequently used to secure critical locations, ...more
When you don't have anyone to play with in the flesh, nothing beats a round of competitive online Scrabble. If you're constantly on the move, the Scrabble app developed by Electronic Arts (EA) for Android and iOS mobile devices is probably your favorite way to play. But let's ...more
If you've grown bored of day-to-day hacking and need a new toy to experiment with, we've compiled a list of gadgets to help you take password cracking and wireless hacking to the next level. If you're not a white hat or pentester yourself but have one to shop for, whether for ...more
When shopping for a new smartphone, you'll encounter comparisons and spec sheets that are filled to the brim with values like mAh, GB, and GHz. To the average consumer, however, these values are meaningless, so we end up looking at which device has the specs with the highest a ...more
Not to be outdone by Apple and it's new line of flagship phones, Google has followed suit and finally announced the followup to their highly regarded Pixel line of handsets — the aptly named Pixel 2. Thankfully, the tech giant has also joined in on the trend towards more durab ...more
In case you didn't catch the big event in Cupertino, Apple just unveiled two of the most cutting-edge phones ever made — the iPhone 8 and the iPhone X. Out of the many glorious specs that were rattled off on stage, one stands out for being just a little confusing: Both models ...more
In recent years, Hollywood has taken a shine to hackers, with hackers appearing in almost every heist or mystery movie now. This can be both good and bad for our profession. As we know, whichever way Hollywood decides to depict our profession is how most people will perceive i ...more
You may have heard of a signal jammer before, which usually refers to a device that blasts out a strong enough radio signal to drown out the reception of nearby devices like cell phones. Purpose-built jammer hardware is outright illegal in many countries. Still, Wi-Fi is vulne ...more
The DrinkShield is not quite as dirty as the picture above may convey. Circuitry nerd Craig Smith (who also happens to love drinking) has developed a breathalyzer that can be turned into a potentially naughty party game. Aptly tagged with the phrase "Blow Me", the DrinkShield ...more
There are nearly 100,000 unique onion service addresses online with over two million people using Tor every single day. Join me as I explore a small fraction of what the Tor network has to offer. It's puzzling to imagine about 100,000 .onion websites in existence. Readers who ...more
Airgeddon is a multi-Bash network auditor capable of Wi-Fi jamming. This capability lets you target and disconnect devices from a wireless network, all without joining it. It runs on Kali, and we'll cover installing, configuring, and using its jamming functionalities on a smal ...more
Kip "Kipkay" Kedersha is known for his intriguing and clever how-to and prank videos, even when he teams up with MAKE Magazine. He will show you how to tweak, hack, mod, and bend any technology to your hacking needs. No electronic device, gadget, or household item can stand th ...more
If you have a modern iPhone, you have an excellent video recorder at your disposal. Every iPhone since the 6S has the ability to shoot in 4K resolution, and each new iteration has brought new capabilities to the table. But even the best mobile shooter can use a little extra he ...more
In five short years, three generations of ultra-low-cost Raspberry Pi devices have challenged the boundaries of what a person can do with a $35 computer — especially with Kali Linux. With each Pi more powerful and cheaper than the last, the addition of the Pi Zero in 2015 too ...more
While photography usually gets all the love, our phones have gotten really good at capturing video. Think about it — when was the last time you needed a camcorder for a vacation? With mobile cameras getting better each year, we're now at a point where smartphones can be used f ...more
The reason Amazon's Kindle has become so popular over the past several years is due to the amount of digital books one can fit inside—over 1,000 for the smallest Kindle. Gone are the days of lugging around heavy books to school and the airport. Instead we can fit our e-readers ...more
When it comes to resistance to the elements, Samsung seems to believe in the old saying "if it ain't broke, don't fix it." They've carried over the IP68 rating under IEC 60529 that was first found on the S8 all the way to their tenth-anniversary flagship, the Galaxy S10. While ...more
Duct tape is the king of all household items. You can use duct tape for practically anything, like this sweet wallet. But duct tape isn't the only crafty tape out there; masking tape holds its own, too. You may already know that you can make homemade speakers using an inflate ...more
Many have tried to prove (or disprove) that tennis ball lock picking really works, but it still seems up for debate. Mythbusters have supposedly debunked this technique (watch the video). Someone over at the Auto Blog also has tested this car lock method with failed results (w ...more
While modern browsers are robust and provide a lot of functionality, they can be unlocked to do some pretty spectacular things with browser extensions. For hackers and OSINT researchers, these tools can be used to defeat online tracking, log in to SSH devices, and search the i ...more
Hello, all. In this article, I will be showing you how to make one of the most useful products known to man. I am talking, of course, about charcoal. You might be surprised at just how many uses this stuff has. You can use it to purify your drinking water, replace your aquari ...more
Loaded with a gorgeous display and a powerful processor, the Kindle Fire HDX is an impressive all-around tablet, especially when it's used for what Amazon Kindles were built for—reading electronic versions of novels, textbooks, and other printed works. While the Kindle Store ...more
This is the third part of my electromagnetic pulse series (see Part One and Part Two). By now, I've covered the hardware and general concept of electromagnetic pulse generators, but how exactly do they disable electronics? How can an invisible field of energy have such a catas ...more
There's an iOS feature that benefits many users, but it's absolutely vital if you wear AirPods or other headphones models connected to your iPhone. A large number of iPhone users don't even know about it, especially since it's disabled by default and hidden deep in the system ...more
The game has undergone many transitions over the years, since its days as LEXIKO (1931) to its briefness as CRISS CROSS WORDS to its current and amalgamated, renowned brand of SCRABBLE. There has been many editions of the word board game along that historic metamorphosis, and ...more
Solar panels are an amazing invention. Catching energy from the Sun before it even enters Earth's food chain, photovoltaics are like an all-natural nuclear power plant. Unfortunately, the constituted parts of a solar panel are rare, valuable, and subject to the coercive forces ...more
So the new iPhones have arrived. Like last year, Apple released three iPhones in three different sizes that vary in price and specs. There's the base model iPhone 11, and then there are the real deal, premium models, the iPhone 11 Pro and Pro Max. The iPhone 11 Pro and 11 Pro ...more
You may already know that you can build a functional circuit on a sheet of paper with the graphite from a pencil, but you'd probably never think of using it to fix an electronic device. This same principle can be used to bring back a bricked phone, but can also repair a damage ...more
A stethoscope, often considered the symbol of a doctor's profession, but also used by safe-crackers and auto mechanics to hear sounds that otherwise couldn't be heard. Well, it's time to make a high-tech electronic spy stethoscope with Kip Kay in this gadget video tutorial, fo ...more
Google's new Pixel and Pixel XL smartphones are available for pre-order right now, but the general public won't start to get their hands on these devices for another week or two. Tech reporters got some hands-on time at Google's launch event on October 4th, but camera testing ...more
Mice, cute as they may be, are an unwelcome visitor in many a home. This video tutorial provides step by step instructions on how to hack a wireless electronic laser mouse trap from an automatic garage door opener and a computer mouse. Find out where those little pests are goi ...more
If you've ever taken apart an electronic device that uses physical buttons, you already know why these types of input methods are destined to fail. The rubberized contacts used in physical press-and-release buttons like those of a gamepad or keyboard are incredibly frail and c ...more
Give an 18-month-old a shoe, check back 10 minutes later, and it's a very big maybe he will have it on his foot. But give him your smartphone, and in a mere five minutes, he can take 100 pictures of the carpet, send weird messages, and delete essential apps. Imagine what your ...more
Android 11 is here. Prior to Google dropping the naming scheme, this would have been a dessert with an R name (maybe Rice Krispies Treat or Red Velvet Cake) — but nope, just plain ol' Android 11. And after months of betas and a global pandemic, it finally debuted a little over ...more
The holiday season is here, and if you didn't already pick up a SCRABBLE set during Black Friday or Cyber Monday, then you still have time to buy the perfect gift for your lexical-minded friend. There's sure to be deals out there over the next couple of weeks, you just need to ...more
Take a tour through the world of the light-emitting diode. Learn - who invented it, how to use it, and how to make your own. A light-emitting-diode (LED) (pronounced /??li?'di?/),[1] is a semiconductor diode that emits light when an electric current is applied in the forward ...more
Step 1: What Exploit Development Is and Why Should I Be Interested on About This Topic An exploit is a piece of software, a chunk of data, or a sequence of commands that takes advantage of a bug or vulnerability in order to cause unintended or unanticipated behavior to occur ...more
Check out this Make Magazine segment on building mini robots. Then you can move onto huge ones like Big Dog! John Park builds some lively and inexpensive miniature robots. Starting with a simple vibrabot made from a scrub brush, John assembles a solar junkbot and a slightly m ...more
Keyloggers are a must-have tool in your arsenal. Hardware keyloggers have the advantage of being undetectable through anti-virus or other protection programs. They also capture keystrokes before the OS even boots up, so they are pretty handy tools. The only issue with these t ...more
After months of waiting, the iPhone 11 is here. At an event in Cupertino, Apple unveiled the iPhone 11, 11 Pro and 11 Pro max. You probably have a lot of questions after reviewing the specs sheet, including wanting to know more about the IP68 rating that all three phones have. ...more
Defcon is the largest hacker conference with something for everyone, whether it be the talks, parties, villages, or any of the hundreds of events. In this guide, we'll take a holistic view at everything that goes into attending the con for the first time, from securing your el ...more
Augmented reality is beginning to leak out into the mainstream world. This is thanks, in part, to ARKit and ARCore. These releases turned the current smartphones owned by millions of Apple and Android users into AR-capable machines. And while there are definitely some awesome ...more
Reuben Margolin builds large scale kinetic sculptures based off of mechanical waves. Some of his sculptures contain hundreds of pulleys all working in harmony with each other to create sinusoidal waves and their resulting interference patterns. He designs them all on paper and ...more
Three years ago, Scrabble was one of the very first 500 mobile applications to appear on the new iTunes App Store, allowing iPhone users the chance to kill their Scrabble cravings on the go. It was a smart move for Hasbro and Electronic Arts (EA), but it's been two years and e ...more
If the whale tail cookies and edible undies weren't naughty enough, you've still got about 24 hours left before Valentine's Day to whip up one of F.A.T. artist Randy Sarafan's step-by-step clap-off bras. Inspired by the electronic singing panties and remote-controlled bras of ...more
Whether you're in an airport, restaurant or waiting room, the insidious grip of televisions on human life is omnipresent. Sometimes it's nice to talk to other human beings while looking at them directly—actually hearing what they have to say. Thankfully, there's a DIY device ...more
Technology in computers these days are very favorable to the semi-knowledgeable hacker. We have TOR for anonymity online, we have SSDs to protect and securely delete our data—we can even boot an OS from a thumb drive or SD card. With a little tunneling and MAC spoofing, a dece ...more
Everyone floats in the Dead Sea because the amount of salt in water effects the density. Do a hands-on experiment and practice checking density. Here’s a good science experiment to do in class or at home, if you have access to an electronic balance. The density of salt water ...more
Kip "Kipkay" Kedersha is known for his intriguing and clever how-to and prank videos, even when he teams up with MAKE Magazine. He will show you how to tweak, hack, mod, and bend any technology to your hacking needs. No electronic device, gadget, or household item can stand th ...more
Household Hacker brings you fun hack how to projects in a variety of areas: electronic hacks, computer hacks, pranks, etc. Search Household Hacker on WonderHowTo for more videos by this creator. In this video, learn how to mod a USB flash drive. Household Hacker has put toget ...more
This video tutorial demonstrates a mouse-hacking simple prank sure to annoy any friend or colleague. To replicate this hack, you'll need a mouse and a musical key chain. The steps are roughly as follows: First, open up the mouse. Looking inside, find and remove the scroll whee ...more
When Apple announced its new iPhone 7 and iPhone 7 Plus models in San Francisco, one of the biggest new features was an "IP67" water-resistance rating. Couple that with a few official renderings that show the new iPhone covered in water, and you'd probably arrive at one logica ...more
They're finally here. Apple announced three new iPhone models at their "Gather Round" event in Cupertino, and they're all absolutely gorgeous phones. With bezel-less screens and polished titanium edges, the iPhone XS, XS Max, and XR are truly marvels of engineering — but perha ...more