In this video tutorial, learn how to unlock (or jailbreak) your Blackberry, with these step-by-step instructions. This video also shows you how to get a IMEI Unlock Code from "Unlock To Talk", however, this code costs money. You can access a code here.
If you're an owner of a BlackBerry smartphone, chances are you're going to want to use BBM, which for all of you newbie BlackBerry owners, stands for BlackBerry Messenger. BBM is an instant messaging application developed solely for BlackBerry device owners. Video: Add contact ...more
It's called a Quick Response code, but most know it simply as QR code, a matrix barcode dedicated to the world of smartphones. The information contained within the square black modules could be text, a URL, vCard, or some other kind of data. And even though mobile tagging has ...more
Want to switch your Blackberry Curve's service? Here might be your chance. In this tutorial, learn how to unlock (or jailbreak) your Blackberry Curve in just a few steps, listed below (from Killer Number X): 1) Go to menu 2) Go to options 3) Go to advanced options 4) Sim card ...more
BlackBerry has formally announced the arrival of its flagship, the KeyOne, during Mobile World Congress 2017 in Barcelona. The all-Android KeyOne looks distinctly BlackBerry, with its 4.5" screen and physical QWERTY keyboard. Here's the lowdown on this elegant handset that hea ...more
Images of BlackBerry's two upcoming Android phones have surfaced. Reportedly named "Hamburg" and "Rome," keeping with the company's tradition of using cities as code names for its devices, the images come from BlackBerry Central founder Dylan Habkirk (via Times News UK/GSMAren ...more
When going out to eat with friends, it's inevitable that one person takes charge at the end of the meal to split the bill. They whip out a pen and begin asking everyone what they ordered, carefully dividing, adding, and subtracting on the back of the receipt for everyone to us ...more
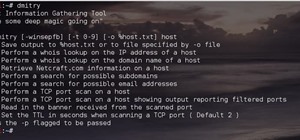
As long as you're on the internet, you can be hacked. With an estimated 2.65 billion social media users, these apps are prime targets for hackers. While companies like Facebook, Snap, and Twitter do a formidable job against the waves of attacks they receive daily, they are no ...more
We have some bad news for BlackBerry fans: It looks like the upcoming KeyOne flagship won't be shipped in April after all. At the company's fiscal Q4 2017 earnings call, CEO John Chen confirmed that the new device wouldn't be shipped in April as planned, but instead, will be ...more
It's that time of year again. The world's largest electronics companies are sending representatives to the annual Mobile World Congress event in Barcelona, and for gadget lovers like us, that means we'll get our first look at some of this year's biggest upcoming flagship smart ...more
These codes contain a lot of important information, such as BlackBerry version used, PIN, IMEI, the duration since the last BlackBerry activation, signal strength, battery power, storage capacity, and the total memory capacity of the phone. Video: .
Syncing your bluetooth earpiece to your BlackBerry device can be tricky. But pairing your bluetooth enables BlackBerry with your earpiece is actually quite easy. Best Buy has answers. The Best Buy Mobile team explains how to connect a Bluetooth earpiece to your mobile device. ...more
Have you ever noticed that whenever you setup your voicemail account after getting a new cell phone number, it asks you to create a security pin to access your voicemail from other phone lines? When you call your home or cell number from another phone, after a few rings your ...more
Coinhive, a JavaScript cryptocurrency miner, was reportedly discovered on the BlackBerry Mobile website. It was placed there by hackers who exploited a vulnerability in the site's e-commerce software that allowed them to anonymously mine cryptocurrency every time the website w ...more
In a long-awaited move, the popular messaging platform WhatsApp has finally made its official web debut. Desktop and laptop owners will be happy to know that they can now message their favorite contacts directly from their computers, without the need to install additional apps ...more
While there is definitely no shortage of video game emulators in the Android Market, it lacks in modern gaming consoles. Nintendo 64, Game Boys, and Sega Genesis are all accounted for, but what about emulators for some of the gaming consoles that have come out in the, let's sa ...more
It took many months of cries from all around the internet—and a particularly large groan from an ex-Lifehacker editor-in-chief—but Apple has not only acknowledged the existence of its iMessage problem, it's promising a fix. Update: Apple has finally fixed the issue by creatin ...more
Outside of early military applications, augmented reality is a relatively new technology. It stands to reason that the next company to make a splash in AR would be a startup, and Techstars wants to help. Nonetheless, there are also more established companies working in AR, an ...more
When Google introduced the Pixel 3 on October 9th, one of new additions they briefly mentioned was the Titan M security chip. While they did talk about how it will improve overall security, they didn't expand on the number of changes it brings to the Pixel 3's security. Well, ...more
A team of academics from three different universities and two private companies have just discovered a new vulnerability that affects almost every Android device since 2012. The vulnerability is known as RAMpage, and it could be used to gain complete control over the device. ...more
There's nothing like buying an awesome new gadget, but it leaves you with one problem (besides an empty wallet)—what do you do with the ones you already have? There are plenty of ways to put your old gadgets to use, but if you'd rather get rid of them, you may as well get some ...more
Now that smartphones have ensured that we're connected to the internet 24/7, online privacy has become more important than ever. With data-mining apps hoping to sell your information for targeted ads, and government agencies only one subpoena away from knowing every detail of ...more
When it comes to cybersecurity, one layer isn't enough. A complex password (or one created with a password manager) does a good job of protecting your data, but it can still be cracked. Two-factor authentication strengthens this by adding a second layer of security, giving you ...more
Biting into a perfectly ripened piece of fruit is enough to convince you to give up baked goods and plant your own garden. The combination of flavor, juice, and sweetness in a ripe mango, apple, plum, or berry is the stuff of life itself. Alas, most people don't know how to c ...more
Mobile World Congress is a four-day event that is both a showcase and conference starring prominent figures in the mobile industry. Oftentimes, OEMs will use this event to announce new products for the upcoming year — and this year shouldn't be any different. Here are all the ...more
Rooting. As an Android user, I'm sure you've heard the word once or twice. According to Kaspersky, 7.6% of all Android users root — but for the 92.4% who don't, we wanted to talk to you. Rooting allows you to remove barriers and open Android to a level of unprecedented contro ...more
Android comprises an entire ecosystem of apps, games, functions, and features, so it would only make sense that it has its own lexicon. Words, phrases, and acronyms that didn't exist ten years ago are now used in an off-the-cuff style by developers and support technicians acro ...more