Welcome back, my tenderfoot hackers! We have looked at a number of ways that we sniff traffic on the network with such tools as Wireshark, tcpdump, dnsiff, and others, but each of these tools is only capable of pulling packets off the wire. Those packets can be examined for ...more
Many FarmVille farmers want money fast, or experience fast, or want to level up, or want to speed things up— make and earn things faster. No matter how long they play, they're not getting what they want, and that is to outshine everybody else. But you can't reach the top by si ...more
I'm constantly searching for a homemade pizza dough that tastes good but isn't too challenging to execute. In other words, a recipe that doesn't require any arcane "dough whispering" skills. However, my hunt may be coming to an end thanks to one celebrity chef's concept. Maki ...more
How many of you have or know people who have a smartphone? There's a lot of you, right? Well, depending on how most of you use those smartphones, there could be all kind of sensitive information stored on it, and that doesn't just mean sensitive personal information, but it co ...more
In this clip, learn how to make a fast, cheap and super easy mount for your your bicycle to display safety lights. Wearing bike lights at night will help you stay safe in the dark and if you want to avoid the cost of getting lights custom fitted, this hack is perfect for you. ...more
Lava lamps are cool and retro, but they can be expensive and there is a risk of fire if you leave them unattended and they tip over accidentally. By using this tutorial by Shooting Eggs, you can make your own light up bubble tube using materials you might already have around t ...more
Systm is the Do It Yourself show designed for the common geek who wants to quickly and easily learn how to dive into the latest and hottest tech projects. We will help you avoid pitfalls and get your project up and running fast. Search Systm on WonderHowTo for more DIY episod ...more
In this episode of Full Disclosure we are explaining the website attack known as Cross-Site Scripting (XSS). Cross-Site Scripting is a type of security vulnerability that affects web applications that do not sanitize user input properly. This kind of vulnerability allows an "a ...more
In this tutorial, learn how to hack a can of Monster - or any large soda can - to stash a bottle. This is great if you are drinking a beer in public when you aren't allowed or if you'd just rather no one knew what kind of embarrassing beverage you are actually consuming. Follo ...more
Don't be too disappointed if you don't have the spiffy new Kindle Touch, there is an up side. The benefit to owning the older (duller) models is that the firmware remains the same throughought generations, so the hacks retain their usefulness. This has given the modding commun ...more
Bloons Tower Defense 4 cheats are here. And you guessed it… this one uses Cheat Engine. If you want to hack the game, you have to know how to do it, and Cheat Engine can be kind of a complicated process if you've never used before. This video tutorial teaches how to hack mone ...more
For as much money as they've made from North American video game audiences over the years, Japanese game developers don't seem to have very much faith in them. Dozens of great titles from their 40 years in the industry have appeared in Japan and across Europe, oftentimes even ...more
When the iPad 2 was released earlier this month, as to be expected there was a whole lotta buzz. And for good reason—while the the newest version shares the same price tag as the old, it boasts some significant new features. In case you missed it, here's a quick overview: Bet ...more
Netcat is a featured networking utility which reads and writes data across network connections, using the TCP/IP protocol. It is designed to be a reliable "back-end" tool that can be used directly or easily driven by other programs and scripts. At the same time, it is a featur ...more
The Xbox 360's official firmware is constantly being updated, and the unofficial kind is no different. This video will show you how to update your flashed XBox 360 LiteOn disc drive's LT firmware to the newest version, allowing you to continue to use all of the cool hack and m ...more
This is a cheap little hack from a $5 discount store headlamp. Check it out. Quick and easy. You need a bolt to secure to your camera. This is great if you are shooting long shots and need different brightnesses. Otherwise kind of ghetto.
Movies like to show hackers breaking passwords with fancy software and ludicrous gadgets. The reality of busting passwords open is much more mundane. Simple as it may sound, most passwords are broken purely by guesswork. Check out this infographic from ZoneAlarm, as well as th ...more
One day, you may find yourself in an emergency situation where you need to undo the chain lock of your home's front door, or somebody else's front door. Maybe someone forgot the unlock it when exiting the back door. Maybe you're grandfather is having a heart attack. Maybe your ...more
Today's post is a small go-to guide for beginner programmers in Null Byte. With many of our community members picking up programming from our Community Bytes, it only makes sense to lay out a one-stop guide for your reference. Hopefully this guide will help you make an educate ...more
Don't trash your unfashionable old skirt, but turn it into something new, something unique, something fashionable. See how to create a designer tote from a skirt in this video from GiannyL. This DIY closet hack is simple and easy, and the tote bag is great for any occasion, w ...more
This is kind of scary! This video demonstrates just how easy it is to hack into an iPhone to access the data on it - including recovering deleted photos. You only think you've deleted those naughty photos you sent to your girlfriend.... Fortunately, there is a way... However, ...more
Unless you avoid the news entirely, you've almost certainly heard about the hacking sprees that have been taking place over the past several weeks. Tens of thousands of usernames, passwords and email addresses have been released online for anyone to download. Thankfully, it se ...more
Hacking into computer systems to steal passwords could be a bit complicated for the average everyday joe, but for all of your tech illiterate folks out there, there's any easy way to get that password, and all it takes is a camera. Check out this con video tutorial to learn h ...more
The biggest struggle with flashing DVD drives on Xbox 360s has been the price tag of the probe to extract keys on some drives. The probe and kit is required to extract the DVD key, which is needed to perform a drive repair, flash, or backup of any kind. Who wants to pay big bu ...more
As per Alex's request, I am posting about generating word-lists in Python. However, this is my FIRST attempt with Python, so please provide me with critiques and any and all comments. I really want to know what you think as there was a little bump here and there seeing as I a ...more
It's been a great year for video games, kind of. Sure, the AAA release lineup has been a trainwreck and hacking has been a bigger problem than ever. But two things have happened involving the federal government that have made video games more legitimate in the United States th ...more
Oh, LifeHacker, we love you. You've brought us so many handy HowTo's: Hack Wireless Internet, Bypass Blocked Websites, Convert a Laptop Into a Projector, Watch TV & Movies on the Web For Free, 10 Must-Know Google Privacy Settings, and more. And now, another great one: LifeHac ...more
With the purchase of my latest computer, installing Linux turned into a nightmare from Hell. The graphics drivers are probably the biggest issue that anyone with a newer computer will run into when installing Linux. AMD and NVIDIA are the dominant ones on the market, both of w ...more
Del The Funky Homosapien ft. Khaos Unique "Proto Culture" Chorus:] Let me tell you about the Proto Culture If you don't know the culture, here's the whole structure We've had enough of the lackluster-trust us We get the kind of games you can't rent at Blockbuster [KU:] Ga ...more
WonderHowTo is made up of niche communities called Worlds. If you've yet to join one (or create your own), get a taste below of what's going on in the community. Check in every Wednesday for a roundup of new activities and projects. Thanks to all of our active moderators and ...more
This Null Byte is the first part in a mini-series on the art of Social Engineering. I will be teaching you how to effectively defend yourself against it. What is Social Engineering? Social Engineering is the art of hacking humans. It's when a person is manipulated into doing ...more
The community here on Null Byte has always been great and helpful in sharing their know-how, even before I took up admin duties in this World. I jumped at the chance of leading Null Byte because I enjoy teaching and informing people on all of the important need-to-know things ...more
Wireless networks. Nowadays, everyone uses 'em, but most don't secure 'em. On average, I can drive up and down any block in my city and find at least one or two open or semi-open networks on any given day. With some changed MAC addresses for good measure, an attacker can use y ...more
If you're a frequenter of Null Byte, I bet you have at least some interest in information security. Furthermore, you have a hobby that if applied in certain ways, will get you arrested. I've received quite a few messages from the community here about federal cybercrime law and ...more
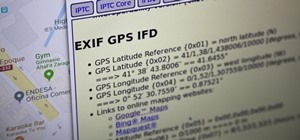
Anonymity is something that doesn't exist today. Everything you do in the world is tracked, from the purchases you make to surfing the internet—even taking pictures on your iPhone. Everything you have ever said and done on the internet is still there—somewhere. This is called ...more
The latest film addition in the American-produced Millennium series, The Girl in the Spider's Web, was just released on Blu-ray a few days ago. As you could expect, the movie has many hacking scenes throughout, just like the previous English and Swedish language movies centere ...more
Pokémon GO, the global augmented reality game that's brought fans out of their homes to catch Pokémon across the planet, has brought about plenty of real-world positives. Unfortunately, when players get power hungry and start taking game hacks too far, we all get a little scre ...more
Welcome back, my neophyte hackers! Have you ever had a neighbor that you're certain is up to no good? Maybe you've seen him moving packages in and out at all hours of the night? Maybe you've seen people go into his home and never come out? He seems like a creep and sometimes ...more
Garlic is a key ingredient in many delicious meals, and if you've been a fan of our site for even a short while, it's no secret that we love to share tricks and tips to make cooking with garlic even easier than you first assumed. Here are just 10 of the many ways to both prep ...more
In the previous article, we learned how to set up our VPS, configure our PHP server, and developed an in-depth understanding of how the payload works. With all that taken care of, we can get into disguising our payload to appear as an image and crafting the note in the greetin ...more
With an ordinary birthday card, we can introduce a physical device which contains malicious files into someone's home and deceive them into inserting the device into a computer. In my last series, we used a Post-it note to trick a neighbor into visiting a website that we cont ...more
Conducting phishing campaigns and hosting Metasploit sessions from a trusted VPS is important to any professional security researcher, pentester, or white hat hacker. However, the options are quite limited since most providers have zero-tolerance policies for any kind of hacki ...more
Using just a small sticky note, we can trigger a chain of events that ultimately results in complete access to someone's entire digital and personal life. Imagine arriving home one night after work and there's a Post-it note on your apartment door with the website "your-name- ...more
Compromised uTorrent clients can be abused to download a malicious torrent file. The malicious file is designed to embed a persistent backdoor and execute when Windows 10 reboots, granting the attacker remote access to the operating system at will. Torrent clients like uTorre ...more
There are many ways to attack a Wi-Fi network. The type of encryption, manufacturer settings, and the number of clients connected all dictate how easy a target is to attack and what method would work best. Wifite2 is a powerful tool that automates Wi-Fi hacking, allowing you t ...more
Your social security number, credit card information, and medical history can fall into the wrong hands if you're not careful about how and where you share your data online. If you really care about your data, there are tools and techniques you can utilize to protect yourself ...more
Samsung isn't set to reveal its latest and greatest — the Galaxy S10 line — until February 20, but that hasn't stopped leaks from giving us an early taste. While we already know what the rumored devices will probably look like, we now have access to their wallpapers as well. A ...more
A developer from a firm named Tendigi came up with a way to run Android Marshmallow 6.0.1 on an iPhone 6 Plus, and it's pretty awesome. The hack is the brainchild of Nick Lee, who had previously installed Windows 95 on an Apple Watch, and you can see it in action below. Video: ...more
One of the more annoying parts about cooking or baking at home is dealing with sticky ingredients. You scrape the peanut butter out of the jar and into a measuring cup to make sure you have the right amount for your recipe, then scrape the correct amount into the bowl you're c ...more
Hello partners, first of all I would like to thank all those who have sent me positive feedback about my posts, to say that I'm always willing to learn and teach. I'm also open to answer the appropriate questions. Second i want to say sorry for the series i left in stand by m ...more
If your facebook account was hacked by someone and you really want it back this tutorial would help you get it back. Step 1: First goto this link. https://www.facebook.com/hacked Click the button "Your account has been Compromised". Then type in your email address, Login nam ...more
Malware attacks on mobile phones are reaching an all-time high and it looks like companies like Samsung are doing all that they can to prevent any unwanted hackers from accessing its sensitive user data. When it comes to Samsung, well, they get enough flack already being all ...more
In Italian, the word affogato means "drowned." Kind of a morbid name for such a delicious goodie, right? But there's a reason it's called that. For those of you not in the know, affogato is a coffee-based treat usually consisting of a scoop of vanilla gelato or ice cream "dro ...more
When alcohol tastes bad, there's little you can do to save it—or so you think. While it might seem easier to toss your entire bottle of old, opened wine, or to give up and drink crappy vodka anyway, there are creative ways to turn a spoiled or just plain bad boozy beverage int ...more
If you've grown bored of day-to-day hacking and need a new toy to experiment with, we've compiled a list of gadgets to help you take password cracking and wireless hacking to the next level. If you're not a white hat or pentester yourself but have one to shop for, whether for ...more
Design flaws in many routers can allow hackers to steal Wi-Fi credentials, even if WPA or WPA2 encryption is used with a strong password. While this tactic used to take up to 8 hours, the newer WPS Pixie-Dust attack can crack networks in seconds. To do this, a modern wireless ...more
While many people may use Bluetooth every day, the majority don't know how it works or that it can be hacked. Bluetooth hacking gives a clear window into the world of the target. Nearly every device has Bluetooth capabilities, and people store a great deal of personal info on ...more
With all the hype surrounding the recent Galaxy S8 release, it can be easy to forget Samsung makes other smartphones. But let's be real here; $726 isn't cheap. If you're someone who doesn't want to drop that kind of cash on a smartphone — or who doesn't feel your device needs ...more
It took nearly six months, but Google has finally made its wildly popular iOS keyboard available to Android users. Technically, it's just an update to the existing Google Keyboard app for Android, but it renames the app to "Gboard" and includes all of the features from iOS, so ...more
If you took your favorite search engine, gave it a witty personality, and bundled it together with a messenger-style interface, you'd have the new Google Assistant. It's great for getting fast answers—even on your follow-up questions—but its flair for fun might just be the sta ...more