It's gigantic! It can handle over 100 simultaneous touch points! It has a curvature of 135 degrees! And best of all, it is not the newest, insanely expensive gadget to hit the market. Instead, this touchscreen was hacked together with a bunch of PCs, video cameras, projectors ...more
Bejeweled 2 is a famous web-based free game. Bejewel 2 Deluxe is not free and is available for PC, Xbox 360, Apple's iPod and iPhone, PlayStation 2, smartphones, and Macs. Learn how to hack Bejeweled with tricks, cheats, hacks. This video tutorial will show you how to unlock a ...more
Bejeweled 2 is a famous web-based free game. Bejewel 2 Deluxe is not free and is available for PC, Xbox 360, Apple's iPod and iPhone, PlayStation 2, smartphones, and Macs. Learn how to hack Bejeweled with tricks, cheats, hacks. This video tutorial will show you how to change p ...more
Via WonderHowTo World, Cinematography: Aerial photography company perspectiveAerials has captured incredible 360° footage of the Gulf of Mexico oil spill. The team launched their custom built Canon 5D Mark II aerial drone (see video two in the gallery below for a demonstratio ...more
This is a video about "How to Hack: Demolition City 2" by Travis. This is a flash game. To begin hacking, go to the game and enter the first level. At this point, you do not have any cash. Specify that you are using Mozilla in the cheat engine. After you have completed the fir ...more
In this video tutorial, viewers learn how to hack the game Frantic 2, using Cheat Engine. The point of Frantic 2 is to dodge hundreds of bullets coming at you from all kinds of directions whilst destroying enemy ships. Cheat Engine is an open source memory scanner/hex editor/d ...more
In this video tutorial, learn how to open & take the back off the iPhone 2G. This shows how to crack open the iPhone 2G case, specifically to hardware flash the radio by shorting the test point. This was considered the first hack freeing the iPhone 2G from its simlock. Warnin ...more
Hak5 isn't your ordinary tech show. It's hacking in the old-school sense, covering everything from network security, open source and forensics, to DIY modding and the homebrew scene. Damn the warranties, it's time to Trust your Technolust. In this episode, see how to turn a Fo ...more
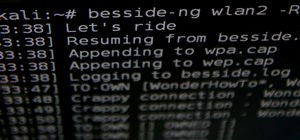
Hak5 isn't your ordinary tech show. It's hacking in the old-school sense, covering everything from network security, open source and forensics, to DIY modding and the homebrew scene. Damn the warranties, it's time to Trust your Technolust. In this episode, see how to build a w ...more
This is a video walkthrough of the ultra violent and gory game MadWorld, exclusively for the Nintendo Wii. Mahalo has produced this full walkthrough for MadWorld, complete with high-quality videos. The guide explains everything from the point system and basic combat techniques ...more
This is a video walkthrough of the ultra violent and gory game MadWorld, exclusively for the Nintendo Wii. Mahalo has produced this full walkthrough for MadWorld, complete with high-quality videos. The guide explains everything from the point system and basic combat techniques ...more
These are video walkthroughs of the ultra violent and gory game MadWorld, exclusively for the Nintendo Wii. Mahalo has produced this full walkthrough for MadWorld, complete with high-quality videos. The guide explains everything from the point system and basic combat technique ...more
Need to use your XBox 360 as a wireless router to tether your other digital devices? While tethering itself is pretty much to the point, what about being able to tether from further distances than ever before? You can actually increase the WiFi range of your XBox 360 by making ...more
WonderHowTo is made up niche communities called Worlds. If you've yet to join one (or create your own), get a taste below of what's going on in the community. Check in every Wednesday for a roundup of new activities and projects. Hacking, crafting, mining & more… just another ...more
Lifehacker posts an article on the art of cracking weak passwords, courtesy of Internet standards expert, CEO of web company iFusion Labs, and blogger John Pozadzides. Pozadzides certainly knows a thing or two about password logic. (Note: this information is not intended to ha ...more
If you're like me, you were always jealous of the kids with rich parents who got to ride around in their own Power Wheels cars. Now that I am tall enough to sell my body and time, I find myself attaining childhood dreams like buying my own Power Wheels car. I would not have ch ...more
In this article, I'll show you how to easily "hack" Facebook, Twitter, YouTube, and any number of similar account types with an Android app called FaceNiff. FaceNiff allows you to sniff and intercept web session profiles over the Wi-Fi that your mobile device is connected to. ...more
Last Friday's mission was to accomplish solving HackThisSite, realistic 4. The fourth in a series of realistic simulation missions was designed to be exactly like a situation you may encounter in the real world. This time, we are told "Fischer's Animal Products is a company th ...more
Have you ever been away from home or on holiday and noticed an open network connection? FREE INTERNET! But then you find out that every search or page redirects you to an "enter password" or "signup here" page. Well, there are ways around this. In this article, I'll show you ...more
Last Friday's mission was to accomplish solving HackThisSite, realistic 3. The third mission in a series of realistic simulation missions was designed to be exactly like situations you may encounter in the real world, requesting we help a friend restore a defaced website about ...more
Nearly everyone has the capacity to be a cheater. Sometime or another, all Xbox users have yearned to get their gamerscore to unimaginable thresholds—for bragging and egotistical purposes. I can relate to this desire. However, I also don't want to mod my gamerscore, because it ...more
With a lot of Null Byters playing around with Linux because of its excessive use in the hacking world, some of you are bound to run into some trouble with the installation at some point or another. If you make a mistake, or you're intimidated by the wonky-looking installation ...more
As a kid, my favorite thing to do at the Natural History museum was a midday stop, when my family strolled past an antiquated looking vending machine in the museum's musty basement. The Mold-A-Rama machine was oddly shaped, George Jetson-esque, and spewed out made-to-order, br ...more
Tricycle + simple plow blade = true yankee ingenuity. (Who needs a pricey snow plow vehicle?) Craig Smith recently submitted his custom contraption to MAKE: "The custom 3-wheel bike with sidecar was made years ago, a replica of a bike my childhood friend had. Last winter I a ...more
Apartment Therapy posts a simple household hack on removing a stripped screw without an extractor. For all our WonderHowTo Home & Garden DIYers, you never know when you might accidentally strip a screw clean. Here's how to remedy the problem. You Will Need: a hammer a multi- ...more
Attention all iPhone users. Engadget posts a helpful tip on possibly avoiding that painfully long iPhone 4 upgrade wait: "Apple and AT&T have worked to give folks a little leniency, with existing AT&T users able to upgrade to the iPhone 4 'up to six months early.' In other w ...more
One of the greatest innovations in the DSLR revolution is not only being able to execute shots you never dreamed possible, but you'll find it's affordable, too. I can't think of a better example than this remote controlled DSLR helicopter rig, designed specifically for the Can ...more
Iowa firefighter Pete Lilja has modded the software of a Canon powershot to record images of Earth, from as high as 85,000 feet! Lilja's hack requires the following: 1 basic point-and-shoot consumer camera attach camera to a GPS transmitter (+ a phone number just in case the ...more
Mikey shows you how to use the cyclic controls on a 6-channel helicopter radio controller. Cyclic controls move a helicopter forwards and back, as well as side-to-side. If you're comfortable with using the rudder controls, you're ready to move on to the cyclic control, usually ...more
David Wang of the iPhone Dev Team has achieved what is considered quite a jaw-dropping hacking feat. Yesterday Wang posted a video of Google's Android operating system up and running on an iPhone. Via CNET: "The Android-on-iPhone hack is a notable technical accomplishment, bu ...more
Watch this video to learn how to draw a rose in just seconds. • To draw a rose, you need a paper and three sketch pens of light green, dark green and red colors. • First draw a “U” shape with the red color. • Mark the bottom peak point of the U shape with a thick dot. • Now f ...more
Make your own custom characters for Icy Tower! It's as easy as drawing stick figures, believe it or not. Only stickman don't look as cool, unless of course it's a stickman that you want to use as your Icy Tower character. This wintery video tutorial teaches you how to make cu ...more
Want to know how to get free green points in WeeWorld? Sure you do. They're free! And there's 500 of them. No hacking involved, just a little trick, but you can't do it over and over again. WeeWorld is a virtual hangout full of self expression, friends, and fun. It's a thrivi ...more
Learn how to stop a cough with acupressure. The next time you're hacking up a lung, try stopping it with the ancient Chinese healing art acupressure. You Will Need * Two hands * Friend WARNING: If you feel pain when using acupressure, stop immediately. Pregnant women should ...more
Christian Cantrell, Adobe's Air Product Manager and Evangelist, has released a video to demo websites that take advantage of the motion sensors in a mobile phone, tablet, or laptop via JavaScript. Now, let's take a look through the code and break down the core pieces that you' ...more
Last Friday's mission was to accomplish solving HackThisSite, realistic 2. This second mission in a series of realistic simulation missions was designed to be exactly like situations you may encounter in the real world, requesting we help a friend take down a racist hate-group ...more
Cell phone jammers, a DIY endeavor for the darker crowd. I'm pretty sure we've all considered having one at some point: whether the obnoxiously loud woman next to you is announcing private bedroom stories to a crowd on the subway, or your kids are grounded from using the phone ...more
Last Friday's mission was to accomplish solving HackThisSite, realistic 1. This is the first in a series of realistic simulation missions designed to be exactly like situations you may encounter in the real world. This first mission, we are asked to help a friend manipulate th ...more
As per Alex's request, I am posting about generating word-lists in Python. However, this is my FIRST attempt with Python, so please provide me with critiques and any and all comments. I really want to know what you think as there was a little bump here and there seeing as I a ...more
Most people have had the unfortunate experience of not having a washer and dryer at some point. Apartments in my area tend to charge at least one hundred dollars extra for the units with washer and dryer hookups, and even more if you want a unit with an actual washer and dryer ...more
Cheers to another completed Community Byte project! Things went well regarding timeliness and being friendly to the other coders and students. If you've got ideas for our next mission, or an idea for a tutorial, submit them to me. Friday, our mission was to take out HackThisSi ...more
Here at Null Byte, we've spoken a lot about securing and anonymizing traffic. This is a big deal. With all of today's business taking place electronically via computers, we need to be secure when on-the-go. A lot of businesses don't even train their employees to secure their c ...more
Remember the good ol' days when you actually had to swipe your credit or debit card to make a payment at the store? Now all it takes is a flick of the wrist to purchase goods with your card, thanks to RFID (radio-frequency identification) technology from Chase (blink), Visa (p ...more
There's a lot of talk going around about Google's new social network and how it's heavily influenced by Facebook, but truth be told, how could they build Google+ without taking a note or two from the world's most popular social network? One thing that's different (and better) ...more
Impress dinner companions with your flawless manners—it’s as simple as observing a few key rules. You Will Need * A crash course in dining etiquette Step 1. Know the basics As soon as you take your seat at the table, place your napkin in your lap and obey the basic rules: ...more
WonderHowTo is a how-to website made up of niche communities called Worlds, with topics ranging from Minecraft to science experiments to Scrabble and everything in-between. Check in every Wednesday evening for a roundup of user-run activities and how-to projects from the most ...more
If you've ever been inside of a real laboratory, you probably noticed how expensive the equipment is. You'd never be able to afford even just one of those ultra high-tech machines required to splice genes or split atoms. Even the lesser machines can be prohibitively costly, in ...more
Law enforcement can make a lot of folks cringe. Too often do we hear on the news, and even experience in our own lives, the unjust way that an unacceptable portion of law enforcement treat the very citizens they are supposed to protect. People's rights are violate each and eve ...more
Eventually, we plan on doing some root the box competitions here at Null Byte, but we're still looking for a server to play on. Anyone want to donate one? You won't regret it. Root the box is like 'king of the hill', except you have to hack a server and maintain access. Each s ...more
We'd like this to be one of the last HTS mission announcements, at least for now. As soon as Null Byte finds a server to play with (anyone want to donate one?), we are going to start doing root the box competitions, which is like king of the hill, except you have to hack a ser ...more
We're officially seeking Null Byters on a weekly basis who are willing to take the time to educate the community. Contributors will write tutorials, which will be featured on the Null Byte blog, as well as the front page of WonderHowTo (IF up to par, of course). There is no ne ...more
We're aiming for this to be one of the last HTS mission announcements, at least for now. As soon as Null Byte finds a server to play with, we are going to start doing root the box competitions, which is like king of the hill, except you have to hack a server and maintain acces ...more
The community tore up the first realistic mission last week. You've applied the techniques learned in the basic missions to a real scenario, so I'm pretty content. The realistic missions are where the learning gets intense and where we can apply real knowledge to extremely rea ...more
What is Google Dorking? Well, simply put, "Google Dorking" is just an efficient way to utilise keywords in order to perform very specific searches on a given subject. In this case, one would look for websites/servers that are vulnerable to attacks or are configured improperly ...more
Welcome to the 10th Community Byte session for coding in Python and completing the challenges presented to us by HackThisSite. These sessions are created to bring our community together, to learn from each other, and grow together. Everyone is welcome, from novice programmers ...more
If you've ever heard software piracy terminology being discussed, I'm sure the term KeyGens came up. KeyGens is short for key generator, which is a program that exploits algorithmic faults in software by generating software license keys that appear to be genuine. Normally used ...more
If you've ever wondered how software pirates can take software and crack it time and time again, even with security in place, this small series is for you. Even with today's most advanced methods of defeating piracy in place, it is still relatively easy to crack almost any pro ...more
We're officially seeking Null Byters interested in teaching others! Contributors will write tutorials, which will be featured on the Null Byte blog, as well as the front page of WonderHowTo (if up to par, of course). This is a job meant for anyone with the will to share knowle ...more
With the purchase of my latest computer, installing Linux turned into a nightmare from Hell. The graphics drivers are probably the biggest issue that anyone with a newer computer will run into when installing Linux. AMD and NVIDIA are the dominant ones on the market, both of w ...more
Null Byte is looking for forum moderators! Welcome to the ninth Community Byte for coding in Python and completing the challenges presented to us by HackThisSite. These sessions are created to bring our community together, to learn from each other, and grow together. Everyone ...more