It is well documented that what you say and do online is tracked. Yes, private organizations do their best to protect your data from hackers, but those protections don't extend to themselves, advertisers, and law enforcement. Whether you are a journalist, a protestor, or a hi ...more
Hackers and makers are often grouped under the same label. While hackers draw on computer science skills to write programs and find bugs, makers use electrical engineering to create hardware prototypes from microprocessor boards like the Arduino. We'll exercise both sets of sk ...more
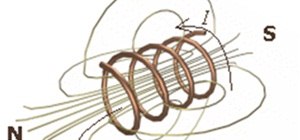
Smartphones and laptops are constantly sending Wi-Fi radio signals, and many of these signals can be used to track us. In this guide, we'll program a cheap IoT device in Arduino to create hundreds of fake networks with common names; This will cause nearby devices to reveal the ...more
Apple has a few exciting surprises for you in its latest iOS 16 and iPadOS 16 software updates. Released on Thursday, May 18, version 16.5 includes new features, bug fixes, and security patches, and there are even hints of some big things coming in future software updates for ...more
What if you could have a secret hard drive connected to your computer that only you could activate? You can! Samimy shows you how to hack a remote controlled toy car and make a super secret hard disk drive in your computer, accessed via a secret activation key. This hidden eme ...more
Interested in tethering a WiFi device to your Google Nexus One phone? This guide will show you how it's done. Whether you're the owner of a Google Nexus One Android smartphone or just covet one, you're sure to enjoy this Nexus One owner's guide from Nexus One Hacks, which pres ...more
Now that you're officially allowed to do it, jailbreaking your iPhone, iPod Touch, or iPad is a better idea than ever before! This video will show you everything you need to jailbreak a wide variety of Apple devices, including the iPhone 3G and 3GS, the iPod Touch 2G and 3G, a ...more
This video will show you how-to hack Bluetooth on your iPhone with an app called BlueSn0W. You'll need a jailbroken Apple device to begin with, so make sure that step is done first. After that you'll be able to hop on someone else's signal.
This tutorial illustrates how a wireless pinhole spy video camera can jam wireless internet or WiFi signals.
Video: . Recycle your hard drive into a hidden flash memory device that only you know how to turn on and use in secret. This DIY hack project allows you to recycle your broken hard drives back to life and turn them into something useful. So far, this project has several funct ...more
In this gamer's guide, you'll learn how to use a signal booster when playing Shaun White Skateboarding for the PS3. For all of the details, and to get started using signal boosters yourself, watch this video walkthrough. Be sure to search WonderHowTo for more Shaun White Skat ...more
9GAG's infographic teaches us all sorts of conveniences and short cuts to daily life, urawaza style. Some aren't complete revelations (the first hanger trick below), but others are pretty cool (if they work!). A few I wouldn't mind trying: free wifi at the airport ice cold dr ...more
Learn how to build an environmentally friendly directional WiFi antenna with this simple video guide. To follow along at home, you'll need the following things: a copper wedge, an N-type connector, some screws, a clamp-on N plug, a pigtail, and a wireless card. You'll also nee ...more
Welcome to the second Goonight Byte! Our second coding session was kindly hosted by th3m, so props to him for letting this happen. Our task this time was to hack the bot that we made the week prior, which was only capable of connecting to the channel and then printing message ...more
Understandably, the tragedy in Japan has substantially risen the level of worldwide radiation-related hysteria. So much so, as an alternative to stampeding health food stores for iodine tablets, crafty individuals and organizations are hacking together personal radiation detec ...more
The iPhone and iPod touch are nearly identical devices, especially now that Apple has added a front-facing camera to the iPod touch. All that's missing is the phone part. With the help of Lifehacker and apps like Skype and Line2, you can save some money by turning your iPod To ...more
Unlock your Galaxy's hidden potential by rooting it! Rooting your phone will enable you to do fun, against-the-rules things like running custom ROMs. Want to turn your Galaxy into a wireless hotspot with free WiFi tethering? You can do that too. Don't know how to root an Andr ...more
Unlock your HTC Tattoo's hidden potential by rooting it! Rooting your phone will enable you to do a great number of fun, against-the-rules things: Interested in running a custom ROM? It's easy. Want to turn your Milestone into a wireless hotspot with free WiFi tethering? Go ah ...more
Unlock your Motorola Milestone Google Android's hidden potential by rooting it! Rooting your phone will enable you to do fun, against-the-rules things. Interested in running a custom ROM? It's easy. Want to turn your Milestone into a wireless hotspot with free WiFi tethering? ...more
Need internet but don't want to pay? Well, try lusting of those around you by picking up their Wi-Fi signal. Live out in the boondocks? No problem… if you have an old satellite dish laying around. Watch this video tutorial to hack you way into free internet. See how to make a ...more
Grab your thinking caps and get your hack on. Null Byte is officially seeking contributors on a weekly basis who are willing to take the time to educate the Null Byte community on anything, from hardware hacks to life hacks. Contributors that write tutorials will be featured o ...more
Hak5 isn't your ordinary tech show. It's hacking in the old-school sense, covering everything from network security, open source and forensics, to DIY modding and the homebrew scene. Damn the warranties, it's time to Trust your Technolust. In this episode, see how to get free ...more
As advanced gaming systems continue to evolve, older classics like the Nintendo Entertainment System (NES) are one step closer to extinction. They're rotting in the basements of gamers. They're gathering dust at the local pawn shop. Or worse... being thrown out in the trash li ...more
Dreams are like an internal human holodeck. Inside your mind, anything is possible, from your grandest wishes to your worst nightmares. This is all well and good, but what if you could control your dreams and become the omniscient god of a handpicked reality whenever you go to ...more
WonderHowTo is a how-to website made up of niche communities called Worlds, with topics ranging from Minecraft to science experiments to Scrabble and everything in-between. Check in every Wednesday evening for a roundup of user-run activities and how-to projects from the most ...more
Hello, fellow Null Byters. Today, with mixed feelings, I want to let you know that this is my last official post as the admin of Null Byte. I've come to the decision that I need to spend more time focusing on my studies. Over the past 5 months, I have enjoyed building this co ...more
In this article, I'll be showing you how to make a cool visual representation of sound using an old cathode ray tube (CRT) television, a stereo, and a sound source. You'll also need a pair of wire cutters, and a few screwdrivers. To properly understand this project, it's a goo ...more
Impress dinner companions with your flawless manners—it’s as simple as observing a few key rules. You Will Need * A crash course in dining etiquette Step 1. Know the basics As soon as you take your seat at the table, place your napkin in your lap and obey the basic rules: ...more
Computer viruses are terrifying. They are undetectable, dangerous, and operate constantly right under your nose. For the average computer user, there are only a few repair options. You could buy expensive antivirus software that causes more problems than it fixes, you can wipe ...more
Body hacks. So simple, so ingenious. They're the shortcuts in life. We love them, the internet loves them. Back in 2008, somebody named Alicia Goh wrote a friendster blog post that has been passed along far and wide. Her tricks of the body include quick solutions for an itchy ...more
Haven't you ever wanted to live in a futuristic home? I think that homes are headed towards an era where they will be controlled by our computers and smartphones. No longer will you have to find your keys to unlock your door, or wait until you get home to monitor your security ...more
The days of trundling hoops, hopscotch and painted wooden rocking horses are long since past. The latest trend in toys? Biofeedback. Electroencephalography. A decade into the 21st century, the toy market is awash in products that incorporate functional neural sensors. One suc ...more
Want more range out of your wireless mouse? How about your keyboard? Maybe you like working from your couch and the signal's a little bit finicky. Well, this is the solution for you, but it requires a little work. See how to increase the rang of a wireless keyboard and mouse ...more
Leaving your Wi-Fi radio "on" allows your smartphone to auto-connect to trusted wireless networks in lieu of using cellular data, but it also consumes battery power while it's constantly network hunting. If you forget to turn Wi-Fi off when you're on the go, expect a quick ba ...more
Greetings aspiring hackers. I have observed an increasing number of questions, both here on Null-Byte and on other forums, regarding the decision of which USB wireless network adapter to pick from when performing Wi-Fi hacks. So in today's guide I will be tackling this dilemm ...more
On all other iPhone models, you go to "Battery" in the Settings app and toggle on "Battery Percentage" in order to see the exact amount of power left in the status bar. On the iPhone X, XS, XS Max, and XR, however, that option no longer exists since there's not enough room up ...more
Switching phones has never been easier. Google backs up most of your app data on the cloud, which can then be restored onto your new phone. Sadly, Signal doesn't use this feature since it could compromise your security. Instead, Signal stores encrypted backups locally, requiri ...more
Traditionally, if you were looking for end-to-end encrypted messaging, you'd stick with something like iMessage, WhatsApp, or Signal. However, if you already use Facebook Messenger, you have all you need for truly private chats with its built-in E2E encryption. It's available ...more
Your social security number, credit card information, and medical history can fall into the wrong hands if you're not careful about how and where you share your data online. If you really care about your data, there are tools and techniques you can utilize to protect yourself ...more
Apple first added the "Do Not Track" option to Safari in iOS 7, which sent a request to site owners and advertisers to not track your browsing activity. By tracking your activity, those third-parties could tailor content to you that you're more likely to interact with. While t ...more
Signal, the encrypted messaging app, has seen 1.4 million downloads in just the first quarter of 2017—roughly twice the downloads it received in the same period last year. Rani Molla at Recode attributes this to Donald Trump's inauguration, as the private messaging service saw ...more
10 Life Hacks: 1.Wifi Booster 2.Spray Bottle 3.Mosquito repellent 4.Untie Plastic Bag Knot 5.Tootpaste Hole cover 6.Remote Control fix 7.Vibrating Toothbrush 8.Shoe Reminder 9.Zip Bag Protector 10.Colored Keys Video: .
As the third-largest smartphone manufacturer in the world, Apple devices are a constant target for hackers everywhere. While iOS has seen fewer common vulnerabilities and exploits (CVEs) in recent years, iPhones still aren't hack-proof. Fortunately, you can strengthen your sec ...more
These days, if you're having friends over, they'll probably ask to log into your Wi-Fi network before asking for a drink. But if you've forgotten your password, it can be quite hard to find, since most devices obscure the characters with asterisks. But it honestly doesn't tak ...more
While the security behind WEP networks was broken in 2005, modern tools have made cracking them incredibly simple. In densely populated areas, WEP networks can be found in surprising and important places to this day, and they can be cracked in a matter of minutes. We'll show y ...more
Considering that nearly half a million brand new apps were published to the Google Play Store in 2015, you can definitely call it a banner year for Android development. In fact, it's getting to the point where we're a bit spoiled as end users, since we've grown to expect somet ...more
Welcome back, my neophyte hackers! Have you ever had a neighbor that you're certain is up to no good? Maybe you've seen him moving packages in and out at all hours of the night? Maybe you've seen people go into his home and never come out? He seems like a creep and sometimes ...more
To hack a Wi-Fi network using Kali Linux, you need your wireless card to support monitor mode and packet injection. Not all wireless cards can do this, so I've rounded up this list of 2019's best wireless network adapters for hacking on Kali Linux to get you started hacking bo ...more
Thanks to backups, Signal conversations can span over multiple years and multiple phones. These archives can get rather large as you share photos, videos, and other files with friends. But between the other apps and large files on your phone, you might not be able to afford to ...more
Have you ever gone to a friend's house and not asked for the Wi-Fi password? Probably not, and the same can likely be said of any friends that come over to your place. But the actual act of sharing Wi-Fi passwords is still incredibly clunky, and it's particularly hard if you h ...more
When you think of high quality music, your phone isn't the first thing to pop into your mind, even though 68% of US smartphone owners stream music on a daily basis. Most of us tolerate the audio quality from our devices simply because music is something we can't live without — ...more
Blue light (like that from our smartphone) tricks the human brain into thinking it's still daytime, even if it's coming from something as small as a screen. So while you're playing around with your new Pixel or Pixel XL after dark, subconscious signals to be awake are preventi ...more
In the digital age, maintaining your privacy is a never-ending battle. All sorts of companies and agencies have access to your data, and quite a few can eavesdrop on almost every method of modern communication. In an effort to push back, Open Whisper Systems has been at the f ...more
The price of hacking Wi-Fi has fallen dramatically, and low-cost microcontrollers are increasingly being turned into cheap yet powerful hacking tools. One of the most popular is the ESP8266, an Arduino-programmable chip on which the Wi-Fi Deauther project is based. On this ine ...more
iOS 12 has a feature that lets you instantly share saved Wi-Fi passwords with other iPhone users, but it can be finicky when you're sharing with multiple people. Then there's an even more pressing question: How do you share your password with Android users? Thankfully, there's ...more
The rumors were confirmed today at WWDC, Amazon Prime is coming to the TV app on the iPhone. This app will allow users to stream their favorite Amazon Prime shows including Bosch, Mozart in the Jungle, Catastrophe, Transparent, and more. The release of this app signals that m ...more
If you're watching videos over Wi-Fi on your iPad, iPhone, or iPod touch, iOS 10 lets you adjust the quality for when you want to save data or need help watching a movie or TV show on a poor connection. To do so, open up the Settings app and scroll down to Videos, then select ...more
Heads up! We've done a new, more thorough review of the best Android file-sharing apps. You can check that out here. Our old file-sharing app roundup can still be viewed below for posterity. Update: The 4 Best File-Sharing Apps for Android (2018) We've come to a point where ...more
In this day and age, maintaining your privacy is a perpetual battle, and doing so with an internet-connected device like your smartphone is even more of a struggle. Every website you visit, every app you install, every message you send, and every call you make is a potential v ...more
You can view battery information in the Today View, you already know what carrier services you, and you can quickly figure out with normal use whether your display orientation is locked, so what do you need the status bar at the top of your iPhone? If you don't find much use f ...more