Electronic warfare tactics work by jamming, disrupting, or disabling the technology a target uses to perform a critical function, and IoT devices are especially vulnerable to attacks. Wireless security cameras like the Nest Cam are frequently used to secure critical locations, ...more
You don't have to be a frequent flyer to know how indispensable navigation apps have become. Many of us rely on these apps for traveling from state to state and getting around in foreign cities, but even more of us count on these apps to beat rush hour traffic and find the qui ...more
Welcome back, my greenhorn hackers! Sometimes, we don't have a specific target in mind, but rather we are simply looking for vulnerable and easy-to-hack targets anywhere on the planet. Wouldn't be great if we had a search engine like Google that could help us find these targe ...more
Got a knack for speeding? Like running red lights? Believe or not, the police have better things to be doing than pulling you over, like catching real criminals. That's why more and more cameras are popping up at known speeding zones and on street corners—so the cops can clean ...more
Need to be undercover? Well, make yourself impossible to photograph. Get some infrared LEDs. They're undetectable to the human eye, but that's not the case with cameras. Wire them to the brim of your hat and you've got instant invisibility to any camera -- paparazzi, Big Brot ...more
The Watch Dogs video game series came out in 2014, enamoring audiences with the idea of a seemingly magical smartphone that could change traffic signals, hack web cameras, and even remotely control forklifts. This may sound like science fiction, but The Sonic uses a customized ...more
It's common for IoT devices like Wi-Fi security cameras to host a website for controlling or configuring the camera that uses HTTP instead of the more secure HTTPS. This means anyone with the network password can see traffic to and from the camera, allowing a hacker to interce ...more
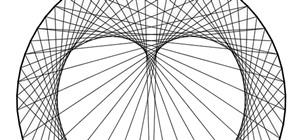
What if you could easily visualize which access point every Wi-Fi device nearby is connected to in a matter of seconds? While programs like Airodump-ng can intercept this wireless information, making it easy for hackers to use and understand is another challenge. Fortunately, ...more
The Deauther Watch by Travis Lin is the physical manifestation of the Wi-Fi Deauther project by Spacehuhn, and it's designed to let you operate the Deauther project right from your wrist without needing a computer. That's pretty cool if you want to do all the interesting thing ...more
Android's settings menu is actually pretty daunting. There are options for nearly everything, so in the sea of various menus and submenus, it's easy to overlook important privacy and security settings. On Google's Pixel phones in particular, there are 20 such settings that you ...more
Data for mapping and other applications is the lifeblood of machine-driven cars, and so far, Tesla has taken a definitive lead in information it has gathered ahead of other driverless players, including Waymo. But Tesla's position could be short-lived, if the world's largest ...more
The new iOS 14 for iPhone arrived Wednesday, Sept. 15, 2020, alongside iPadOS 14, and there are a lot of features to uncover. Improved widgets. Better home screen customization. Exciting Messages improvements. New abilities in Camera and Photos. There's so much here that it'll ...more
Learn how to hack Google with this amazing video. This video will teach you how to hack Google by using advanced search operators and esoteric search terms to find “hidden” files and mp3s quickly and easily; you'll also learn how to use Google to hack unprotected Internet-cont ...more
With more and more vehicle owners simply deciding refuse to pay red light camera and speed camera tickets, private, for-profit companies and municipalities are growing increasingly desperate. America’s second-largest city shut down its photo ticketing program last year largely ...more
As you may have seen in your city or town, red light cameras are on the rise in the United States. In many instances in my area, these cameras have sprung up seemingly out of no-where, and mostly without any reason. Over use of these systems can make privacy (even on the road) ...more
Scenario: it's late at night, the roads are completely empty and you are stuck at the longest light ever. Solution: don't run a red- change it to green yourself. Avoid a ticket, save yourself some time (and perhaps a little gas). Many of you may have already seen Kipkay's ins ...more
Hak5 isn't your ordinary tech show. It's hacking in the old-school sense, covering everything from network security, open source and forensics, to DIY modding and the homebrew scene. Damn the warranties, it's time to Trust your Technolust. In this episode, see how to set up SS ...more
Here at Null Byte, we've spoken a lot about securing and anonymizing traffic. This is a big deal. With all of today's business taking place electronically via computers, we need to be secure when on-the-go. A lot of businesses don't even train their employees to secure their c ...more
This instructional video shows how change traffic lights from red to green, using science, and without actually having to know anything about magnetic fields or properties! Save gas, time, and frustration in your car and during your commute! Works great! See the test results! ...more
A router is the core of anyone's internet experience, but most people don't spend much time setting up this critical piece of hardware. Old firmware, default passwords, and other configuration issues continue to haunt many organizations. Exploiting the poor, neglected computer ...more
It only takes a few commands to manipulate a MacBook's secure HTTPS traffic and pluck login passwords out of the encrypted data. Let's take Facebook and Gmail hacking to the next level by intercepting Safari and Google Chrome web traffic in real time. Both Facebook and Gmail ...more
Welcome back, my tenderfoot hackers! Well, the first season of Mr. Robot just ended and Elliot and fsociety successfully took down Evil Corp! They have effectively destroyed over 70% of the world's consumer and student debt! Free at last! Free at last! Of course, global finan ...more
Tesla has confirmed the EV carmaker has begun to upload videos from models equipped with its latest flavor of Autopilot, as Tesla seeks to "fleet source" data to help improve its cars' machine learning capabilities. Tesla has informed owners of Model S and Model X models prod ...more
While the security behind WEP networks was broken in 2005, modern tools have made cracking them incredibly simple. In densely populated areas, WEP networks can be found in surprising and important places to this day, and they can be cracked in a matter of minutes. We'll show y ...more
Despite the security concerns that have plagued Facebook for years, most people are sticking around and new members keep on joining. This has led Facebook to break records numbers with over 1.94 billion monthly active users, as of March 2017 — and around 1.28 billion daily act ...more
Tesla says the new version of Autopilot is now as good as the previous one, after having completed over-the-air updates of the driverless software during the past few days. Model S and Model X Tesla models the electric car firm began to make October 16 last year lacked certai ...more
From Instagram bot farms in China all the way to vending machines in Moscow that promise to sell you fake followers — the Facebook-owned empire is attracting the attention of the world around. When it comes to Russia especially, the country seems to be developing a little crus ...more
In the driverless race, technological advances can sometimes just add more tension to an already heated competition, if Waymo suing Uber over their allegedly stolen LiDAR technology is any indication. Now, Sony is offering a new camera sensor, one that should help self-driving ...more
Welcome back, my hacker novitiates! Now, and more so in the future, wars will be fought hacker v. hacker. The number of soldiers, guns, tanks, and ships will be less important in your success in warfare than the number of well-trained hackers you have. Every nation and every ...more
Considering how often many of us fly on commercial airlines, the idea that a hacker could somehow interfere with the plane is a very scary thought. It doesn't help to learn that at Defcon, a researcher found that the Automatic Dependent Surveillance Broadcast (ADS-B), transmis ...more
Arcade games have always been more about chance than skill (at least when I play them). Whether you're at a children's party at a Chuck E. Cheese's or drinking it up with your pals at a barcade like Dave & Buster's, you'll find similar games that hold the golden ticket to fun ...more
In a previous guide, I demonstrated how to extract images from a security camera over Wi-Fi using Wireshark, provided you know the password. If you don't know the password, you can always get physical with the Hak5 Plunder Bug. Using this small LAN tap, we can intercept traffi ...more
Welcome back, my rookie hackers! When Wi-Fi was first developed and popularized in the late '90s, security was not a major concern. Unlike wired connections, anyone could simply connect to a Wi-Fi access point (AP) and steal bandwidth, or worse—sniff the traffic. The first a ...more
Welcome back, my novice hackers! Previously in my "Spy on Anyone" series, we used our hacking skills to turn a target's computer system into a bug to record conversations and found and downloaded confidential documents on someone's computer. In this tutorial, I will show you ...more
Welcome back, my greenhorn hackers! Over the years, I have written many articles here on Null Byte chronicling the many the hacks of the NSA, including the recent hack of the Juniper Networks VPN. (By the way, my speculation in that article has proven to be correct. The NSA d ...more
In 2019, the Raspberry Pi 4 was released with specs including either 1 GB, 2 GB, or 4 GB of memory, a Broadcom BCM2711B0 quad-core A72 SoC, a USB Type-C power supply, and dual Micro-HDMI outputs. Performance and hardware changes aside, the Pi 4 Model B runs Kali Linux just as ...more
Hacking from a host machine without any form of proxying is reckless for a hacker, and in a penetration test, could lead to an important IP address becoming quickly blacklisted by the target. By routing all traffic over Tor and reducing the threat of malicious entrance and exi ...more
Hackers can be notoriously difficult to buy gifts for, so we've curated a list of the top 20 most popular items Null Byte readers are buying during their ethical-hacking studies. Whether you're buying a gift for a friend or have been dying to share this list with someone shopp ...more
After seeing the title of this post from me, you might be thinking, "Why did The Joker made another post on a topic on which we already have a nice sticky post?" The fact is that though ghost_ has made a great post, it is more aimed at the general community than the newbies. ...more
Most users don't realize how much valuable data is in their network traffic. With a few simple tools, an attacker can quickly pick out cookies, passwords, and DNS queries from a macOS device as it covertly streams the victim's network traffic to the attacker's system. Here, we ...more
In a world increasingly regulated by computers, bugs are like real-life cheat codes. They give you the power to break the rules and do good or bad without ever leaving your seat. And government agencies around the world are discovering and stockpiling unreported bugs as cyberw ...more
In recent years, Hollywood has taken a shine to hackers, with hackers appearing in almost every heist or mystery movie now. This can be both good and bad for our profession. As we know, whichever way Hollywood decides to depict our profession is how most people will perceive i ...more
Every summer for the last 26 years, hoards of hackers have descended on the Las Vegas Strip for DEFCON, the biggest hacker conference in the US. There's a wealth of talks every season (DEFCON 27 has at least 95 scheduled), and there have been some essential topics to learn fro ...more
Did you know that you can unlock many hidden features and tweak several hidden options by installing a CHDK or Canon Hack Development Kit onto your Canon camera? This walkthrough will give you some insight into the different benefits of the CHDK and how to unlock your camera b ...more
In the digital age, camera's have gotten better, more advanced and more expensive. Even those throw-away cameras have taken the leap to digital-ness, which means more money. But you don't have to be confined by the one-time use of these single-use digital cameras anymore. Kipk ...more
Got a Canon Powershot whose resolution or functions are not cutting it for you? Then amp up its abilities - without flat out buying a new camera - by checking out this digital camera hack video. By modifying the camera's firmware you'll be able to add games as well as a manual ...more
Normally, when standing outside your local regional airport, you'd need a special radio or scanner to pick up the transmissions coming from that Air Traffic Control tower. Well, not anymore. Kip Kay from Make Magazine will show you how to take an old vintage AM/FM transistor ...more
There's nothing more tedious, yet exciting, than watching surveillance cameras at work. They prey on the innocent and the unknowing. They protect businesses, workplaces, and homes. They catch criminals in the act, find hilarious anomalies, and are just darn cool when you're no ...more
If you are a photographer and are handy with a screwdriver and electrical tape, this is a really cool project to do. Basically, you "Frankenstein" a camera, taking a camera apart and rebuilding it with different lenses and the like, which makes for really cool photo effects.
If you've got an extra DVD drive laying around not being used, watch this video and learn how to give the lens new life—as a powerful macro lens for your camera phone! You'll be able to take incredible pictures on your camera phone using this clever mod. Video: .
Iowa firefighter Pete Lilja has modded the software of a Canon powershot to record images of Earth, from as high as 85,000 feet! Lilja's hack requires the following: 1 basic point-and-shoot consumer camera attach camera to a GPS transmitter (+ a phone number just in case the ...more
This tutorial will let you hack into a wide selection of web cams and online security cameras. The hack is actually quite easy, and is best done with a browser like Mozilla Firefox. Navigate to Google in your browser, and then type in "inurl:viewerframe?mode+refresh". This pie ...more
"Skimboarding in a Storm" displays some ultra cool camerawork, employing the relatively cheap and user friendly GoPro camera (also used in the clever Kitchen Timer Panning Time Lapse Hack). Says Gizmodo, "The idea is pretty simple: attach the rugged, waterproof Go Pro camera ...more
Build your own cheap taser with an old camera and some plastic. These guys even show you the final product's effects on each other.
Notice: This is probably not new to many people. This *IS* new for some people however, and meant for them! Post interesting cameras you find. Website at http://householdhacker.com Today we'll show you how to look through various security cameras using search engines. For t ...more
See how to hack a wireless CCTV (closed circuit television) camera to show your Windows or Linux PC desktop on your 42-inch plasma television. This is a homemade hack that's easy with good quality picture. Doing this mod can save you money, unless you don't have a CCTV camera ...more
Ikea Hacker features a nice Ikea mod: Romain turns the Ivar side unit into a camera dolly. "A few days ago, I found out that the Ivar 'wooden ladder' was perfect to use it as rails for my cinema dolly! I can now make some nice sequence shots with this 18€ accessory from Ikea. ...more
We almost forgot about the disposable camera. With every cell phone outfitted with a camera, who needs the emergency 7-Eleven point-n-shoot? Well, until it transformed from photographic instrument to weapon. Be careful. Seriously. Consider the how-to lineage. The disposable ...more
Welcome back, my rookie hackers! "How can I travel and communicate over the Internet without being tracked or spied on by anyone?" It's a question many Null Byteans have asked me, so I have decided to write a comprehensive article addressing this issue. There are a multitude ...more
You've probably already figured out that your Nexus 7 doesn't have a rear camera, but that doesn't mean you can't do some awesome things with your tablet's front camera! Sure, the front-facing camera is only 1.2MP, but that doesn't mean it sucks. In fact, there's a cool mod f ...more