Night People: A Bad Vibes Label Profile Shawn Reed is one of our favorite people, not content with making music with Wet Hair, he also runs 'Night People' - an almost complete DIY record and tape label operation in Iowa - a label which has consistently put out and introduced ...more
Today's digital cameras record not only the images themselves, but also the metadata behind the scenes, like camera settings, location, date, time, etc. But there's a lot more to say about a photograph. What's the subject? Is it night or day? Outside or inside? Person, place o ...more
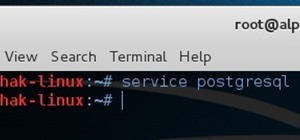
As we all know, security is a big thing here in Null Byte. We've talked quite a bit about ways to encrypt traffic and become anonymous on the internet, some of which entail using proxies, VPNs, and SSH tunnels. We've also talked about preference using SSL pages in practice for ...more
Social networks like Facebook and Google+ are great for staying connected with family, friends and coworkers—even fans. But sharing and communicating with practically anyone in the digital realm has alienated us from most of the flesh-and-blood beings we see everyday—our neigh ...more
Sharing a laptop's wireless Internet connection with other computers connected to its Ethernet port is a great skill to know. It can be good for a number of reasons; Your computer may not have proper hardware to have a standard setup, or you may have an awkward network topolog ...more
This Week's Workshop: Music To My Ears The heart of WonderHowTo's Minecraft World is, naturally, “How-To” and so in the spirit of all things tutorial and DIY we will be hosting a weekly workshop showcasing the best and newest tutorials, builds, and inspiring ideas. We hope to ...more
Behavioral ad targeting companies are diving deeper into the realms of your subconscious with a new approach to serving adverts to you online—and they're using your television. Many web surfers peruse the internet at home while they're watching television. You might even be d ...more
The whole world is connected to the Internet, which means bank for advertising companies who track your every move online. Most of the content you see on the web is free, and that's because of advertisements. If there were no ads, none of us would be addicted to the Internet b ...more
There's an epidemic on the Internet, and the disease—Facebook. It's an addiction comparable to a hot cup of coffee in the morning or a soothing cigarette throughout the day—in worse case scenarios, a hit from the crack pipe. If you're on Facebook, you know what I'm talking abo ...more
Microsoft recently released the first sneak peak of their new operating system, Windows 8, and it's a pretty big departure from the last few major updates. The new Windows 8 was built from the ground up, and is designed primarily as a touchscreen interface, which is perfect fo ...more
Earlier this month, game developer David Braben and his Rasberry Pi nonprofit foundation revealed a $25 USB PC. The computer can connect to an HDMI monitor on one end, and a USB peripheral on the other (such as a keyboard or a USB hub). You can use the USB hub to connect multi ...more
At Google I/O this morning, Google finally announced the launch of its much awaited Google Music service. It's currently in invite-only beta mode, but they claim it will open up to the masses soon enough. To start syncing your music library with Google's Cloud now, you need ma ...more
Your best friend's on Yahoo!, your daughter's on AIM, and now your co-worker wants to connect with you over Windows Live. Before you know it, your desktop is overflowing with buddy lists and message windows. Mismatched alert sounds are dinging and buzzing incessantly. Your com ...more
The Fake Adult Website Prank is an incredible trick if you happen to have the necessary access and work in the internet industry. Luckily, I had both. The objective of this prank is to fool your boss or co-workers into thinking you've accidentally sold out the site to a adult ...more
You may have already heard of Zazzle, an online service that allows you to print on a variety of goods (tees, mugs, posters, etc.). You can design-it-yourself, or choose from Zazzle's library of available designs. Of late, Zazzle has partnered with Keds to offer something a b ...more
If your not sure how to steam your media files to your Playstation3 this video will explain three different ways to achieve just this. Your options will include using a thumb drive, a personal web server or get the appropriate software. In this video, I answer a question from ...more
This video includes instructions on how to get your PlayStation Portable (PSP) onto the BGSU wireless network. Set-up Your Connection 1. Go to Network Settings under the PSP settings menu. 2. Select the "Infrastructure Mode" and press X. 3. Under "Select a connection to edit ...more
Any talk about privacy is a complicated (usually) and touchy subject. In today's world, privacy is an ever eroding pleasure to be had. Numerous cases, like the monumental Kat'z vs United States, have been fought to hold on to this right. So talking about privacy in the domain ...more
If you've read my darknet series, you've probably got a pretty good idea of what I2P actually is and is capable of. One of the features of I2P is that it's designed with P2P file sharing in mind. Using a built-in service called I2PSnark, you can host and seed torrents quickly ...more
This article is all about creating content and using it to build links to your website. Content, meaning articles, videos, and even podcasts is now really the new advertising. That’s because people go to the internet to look for information, not look at advertising. So you nee ...more
I recently posted a link to what seemed to be a very useful guide on Lifehacker for creating a TOR button in Chrome. However, when I tried it myself, it did not work. Also, it lacked a warning on the limits of Tor, which I think are important. Therefore, I decided to create an ...more
Google+ is the most exciting new social network to come around this decade, and the only product with a chance of challenging the monopolies we know as Facebook and Twitter. As an Internet addict, I've joined every major social network there is - from Friendster (who?) to MySp ...more
Thanks Anonymous User For This Article, Not Bad Ok SoftzZz...!.!.!.: Step 1 Antivirus The best freeware antivirus is AVG Anti-Virus Free Edition 2011, and you can get him from this site. Step 2 Optimizing tool For me CCleaner is the easiest way to do some things, like: 1. ...more
"Life is difficult." That's how Scott Peck's best-selling book, "The Road Less Travelled", begins. That life is difficult is not news. Over two-thousand years ago the Buddha said it too: Life is suffering. The sanskrit word the Buddha used for suffering is dukkha. Dukkha doesn ...more
This video shows you how to control your computer from your iPod touch. 1. Go to UVNC. Click on Installation. This will take you to download options. Download the latest stable version. 2. Install Hamachi, which helps you find your computer's IP address. Click on Download Here ...more
Ever wonder how all of those tiny chips and components can fit inside your laptop or smartphone? If you tried to squeeze them in there yourself, your laptop would quickly become too heavy for your lap, and your mobile phone would need wheels to stay mobile. The secret to mini ...more
For a moment, picture a situation where you want to host some files or images, but you do not want it traced back to you. Perhaps you're working on a project with others and need secure data storage. Anonymity is the new shield of the 21st century—and you best protect yourself ...more
There's nothing better than playing a game of Scrabble, feeling the smooth wooden tiles in your hand and savoring the heavy fumes of cardboard, cheap wood and plastic as you rearrange the letters on your rack into the perfect word. You try to keep a straight face while you wat ...more
I've struggled for a long time trying to set up a virtual network between my KVM virtual machines. I tried several forums and tutorials on the web, but still on my system it just wouldn't work. I eventually got it owrking, so I've decided to make some notes of my own. Hopefull ...more
THE FOLLOWING IS ONLY FOR YOUR ALIENWARE WARTIME THE BELOW SETTINGS ARE FOR YOUR ALIENWARE WARTIME EDITION DESKTOP PC, THAT HAS THE CORE I7/X58 MOBO AND DDR3 TRIPLE CHANNEL MEMORY INSTALLED; *AND NOT FOR ANY OTHER CONFIGURATION!* OTHER DESKTOP PC'S WILL VARY IN THESE SETTIN ...more
The trend of online video sharing came to the mainstream with popularization of YouTube, which let users view, submit and share video clips. YouTube started off in the year 2005, and quickly became one of the most visited websites on the internet. Sensing the emerging trend, l ...more
In general, hacking and information security is not just one discipline, but a number of them, and today we will look into some of the networking concepts. In the last Hacker Fundamentals, we talked about the OSI model as well as a little on TCP/IP and the protocols that make ...more
Industrial espionage, social engineering and no-tech hacking are all very real and there are simple precautions that you can take to protect yourself, which this article will discuss. Whether you are a high-profile businessman or a housewife (or husband), keeping information y ...more
Since the internet is becoming more and more important all the time in regards to overall marketing plans for many companies, it’s imperative that the company website be up to the task of attracting visitors and converting them into customers. There are many methods and techni ...more
Before you start snapping away and submitting your photos, please take some time to read the official rules below! No purchase necessary to enter or win; a purchase does not improve your chance of winning; void where prohibited by law. ELIGIBILITY: Only legal residents of t ...more
+Nik Cubrilovic discovered last week that Facebook could track your web activities even after you logged out of your Facebook account. After some blatant denials from Facebook spokespeople, Facebook decided to fix the logout issue, but not before +Michael Arrington, on his new ...more
I have had a lot of people ask me, "How does my neighbor keep getting into my wireless?!". Chances are, these people are all using WEP, a deprecated wireless encryption protocol. Either that, or you are using one weak WPA passphrase. If someone can access your wireless networ ...more
Culinary collective Studiofeast is known for thinking outside the box, especially when it comes to food. They've hosted inventive and spectacular events like the L Train Lunch, where a high-end meal was served to guests on a moving train, and the Datalicious Last Supper, where ...more
Three years ago, Scrabble was one of the very first 500 mobile applications to appear on the new iTunes App Store, allowing iPhone users the chance to kill their Scrabble cravings on the go. It was a smart move for Hasbro and Electronic Arts (EA), but it's been two years and e ...more
Giveaway Tuesdays has officially ended! But don't sweat it, WonderHowTo has another World that's taken its place. Every Tuesday, Phone Snap! invites you to show off your cell phone photography skills. Submit your best shot to our weekly competition for a chance to win an awes ...more
Who could resist a retro SCRABBLE board game for two bucks? Suereal definitely couldn't, especially with the challenge of totally revamping a board game into something genuine and creative. Craftster's Craft Challenge #51 last June was meant to bring life back to an old board ...more
Written by JD Coverly of WonderHowTo World, LoadSave:We've spent the last week with Sprint's new phone, the HTC Evo 4G. Specification wise, it's better than Verizon's Incredible and T-Mobile's HD2. Apple has unveiled the new version of their phone this week and thankfully it's ...more
No doubt you've seen some of the hack logs being released. One part that stands out over and over again is the heavy database usage. It used to be early on that virus and hackers would destroy data, usually just for lulz. However, with the explosive commercial growth of the In ...more
I want to write this article because in my childhood, I had experienced internet stalking which ultimately ended in physical stalking which then lead to several attempted abductions. I have now learned how to use the internet safely, who to communicate with and I've learned ho ...more
Facebook unveiled a lot of changes last week, and, as usual, it's causing a lot of consternation and controversy. People within my Facebook, and on Google+, keep asking how to remove the ticker, and are trying, and mostly failing to make sense of the changes. I've decided to ...more
INTRODUCTION The everyday PC user doesn't think much about its PC and problems that can cause critical damage to their data or other stuffs stored on Hard drive and other electronic parts until the problem actually occurs. Once a failure happens, the repairs can be costly and ...more
Wouldn't it be nice to just sit at your buddy's house, plug into his network, and see exactly what he's doing? What if it was as easy as that? What makes packet sniffers like Wireshark such potent tools is that a majority of local area networks (LANs) are based on the shared E ...more
INTRODUCTION In this world of Internet era, almost everyone wants to create theirs own web presence by either hosting their own blog, articles, photos, videos, reviews, etc etc . But some people choose their own way and decide to have something bigger! What is it? Its a websi ...more
My JO was watching The Simpsons on FOX the other day, like she wholeheartedly does every evening, and I joined her, much like I always do— though I must admit, I'm not as obsessed with the cartoon family as much as she is. Just like she isn't as obsessed with SCRABBLE as I am. ...more
Want to stay up to date with the emails in your inbox? Most mobile phones, like the Samsung Instinct, have an email feature and internet capability to keep you connected. Watch this video cell phone tutorial and learn how to send and receive email on a Samsung Instinct. Check ...more
Bored of sitting on your PC? Need internet on your Nintendo DSI? First check out whether you have WAP/WPA2. You can find out whether you have WAP by going to internet and typing your IP address and going to your wireless settings. If you do have WAP/WPA2 then go to system sett ...more
Learn a little bit about technology with help from EMBARQ. Watch this how-to video tutorial on installing your 2Wire Gateway for EMBARQ High-Speed Internet. This will cover exactly how to install your EMBARQ 2Wire Gateway modem for Internet. This is the complete process step-b ...more
Learn a little bit about technology with help from EMBARQ. Watch this how-to video tutorial on installing your EMBARQ 660 Modem. This will cover exactly how to install your EMBARQ Modem for EMBARQ High Speed Internet service. This is the complete process step-by-step from box ...more
The Dropbox utility can automatically sync your computer files with other devices each time you save them. In this tutorial, learn all of the steps you need to sync files with Dropbox. You Will Need • Internet access • Compatible mobile device • Dropbox software Step 1: In ...more
With a little bit of planning, you can avoid a lot of blood-pressure-raising traffic messes. You Will Need * Time to plan * Traffic reports * GPS service Step 1: Avoid rush hour If at all possible, don’t drive from six to ten in the morning and between four and seven at nigh ...more
Check out this video tutorial to see how to bluesnarf a Nokia 6310i handset (cell phone). What is Bluesnarfing exactly? Answer: Serious flaws in Bluetooth security lead to disclosure of personal data. Three vulnerabilities have been found: First, confidential data can be obt ...more
This is my list of programs that I must have on my PC, but I think you can also use them, so here is the list: Antivirus The best freeware antivirus is AVG Anti-Virus Free Edition 2011, and you can get it from this site. Optimizing tool For me, CCleaner is the easiest way ...more
Note: The article assumes that the reader has a fundamental understanding of at least one other programming language, and that this is intended serve as a quick reference for Perl's basic syntax & behavior in regards to Variables, Control Structures, & Functions. Learning to ...more
If you're reading this, you're connected to some network or directly to the Internet. Have you ever wondered how to set the network icon on the Windows XP Task Bar? This video will teach you exactly how to do this simple task. Make sure to hit "play tutorial" in the top left c ...more
The internet is constantly under siege by bots searching for vulnerabilities to attack and exploit. While conventional wisdom is to prevent these attacks, there are ways to deliberately lure hackers into a trap in order to spy on them, study their behavior, and capture samples ...more