Before you go out to protest, understand what you are facing. Sometimes these demonstrations become infected with looters and rioters, which could mean interaction with law enforcement and potentially arrest. And if your phone is on you, it can be used as a tool against you. ...more
Apple makes it simple to share your location with your family and friends using tools built into the "info" page for each conversation thread in Messages. With those tools, you can send your current location or share trackable real-time coordinates. But iOS always has a few hi ...more
The Home button on an iPhone does a lot. That's not necessarily news for anyone who's ever owned an iPhone with a Home button, but what you might not know is that it's capable of so much beyond the standard everyday functions. So if you have an iPhone 7, 8, or the new SE model ...more
As long as you have the meeting ID, you can join and interrupt virtually any video call on Zoom. And that's how we get terms such as "Zoom-bombing," where someone jumps into a chat to say or visually show vulgar and inappropriate things to the other participants. However, host ...more
Pinning a tweet is a great way to get the point across because it's the first post people see when they visit your Twitter profile. When you pin a tweet, reply, or retweet, it sticks to the top of your profile, whether you create new tweets or not. It's the perfect spot to pla ...more
Between school, work, and your personal life, there's a good chance you have multiple Google accounts. Most Google apps let you log into all of them simultaneously to receive applicable alerts when they arrive. Well, there's a dead-simple way to switch between these accounts, ...more
If you have devices that run different operating systems, you know how frustrating it is that Apple's Calendar app isn't available on other platforms. If you use Siri to quickly create an event on your iPhone or Mac, you're not going to see that event on your PC or Android tab ...more
If you have friends who aren't privacy-conscious, you've surely heard the old "What do I have to hide?" excuse. Despite the fact that billions of people are using the internet each day, many of them don't know the dangers that can find them. And many don't know the tools to co ...more
Life can get busy. Between work, school, and all the extracurricular activities, weekly chores like making a grocery list can get pushed to the back burner. But with a little help from the Google Keep app for Android or iPhone, you can at least make one thing easier. Say your ...more
Sports technology company Form is testing the waters for augmented reality wearables with a product aimed at a very specific user group. On Tuesday, the company unveiled Form Swim Goggles, a $200 pair of goggles outfitted with a see-through display designed to feed activity d ...more
Contrary to popular belief, it takes more than just one artist to create the sound, lyrics, and vocals of a song. With most music being enjoyed digitally nowadays, it's harder to know all of a track's collaborators, as this info used to be in the CD booklet. Well with Tidal, y ...more
For years, there has been a disconnect between the Chrome app on your smartphone and the Chrome browser on your computer. The latter was a powerfully fast browser which could be enhanced with extensions to add new features and functionality, while the former was just a fast br ...more
While Google isn't ready to commit to a wide release of the AR walking navigation mode for Google Maps, the company has begun testing the feature with members of its Local Guides crowdsourcing community. As a result, I've had the opportunity to test an alpha build of the feat ...more
Browsing the web can be dangerous. With all of the various threats out there, it isn't enough to just avoid bad links and visit only HTTPS websites. You need to take advantage of the tools available to you so you don't end up the victim of some scam. Fortunately, Opera is maki ...more
Kali Linux is probably the most well-known hacking distribution among penetration testers. However, there are alternative distros which offer versatility and advanced package management systems that are absolutely worth considering. One such distribution is Pentoo, a Gentoo-b ...more
While iOS 12 is arguably the best iteration of Apple's mobile operating system yet, one major fault so far is security. On Sept. 26, Videosdebarraquito discovered a passcode bypass that gave access to contacts and photos from the lock screen. Apple has since patched that secur ...more
The first few minutes after gaining access to a MacBook are critical — but where do we begin? Using tools built into macOS, we can develop an in-depth understanding of running background processes, detect antivirus software, locate sensitive files, and fingerprint other device ...more
Think back to when you last wanted to transfer some music or videos to your friend's smartphone and how difficult and slow it was. As powerful as our phones are, the default file sharing options are limited. There are, fortunately, some better options which make moving files e ...more
With the re-emergence of Samsung's Good Lock app, you're once again able to tweak parts of your Galaxy's interface with no root or major modifications required. One add-on in particular even lets you fully customize the Quick Settings panel on your S8, S9, or Note 8 in a full ...more
Apple released the iOS 11.3.1 update for iPhones on Tuesday, April 24, 26 days after the official release of iOS 11.3 and eight days after the iOS 11.4 beta 2 update. It is the first minor update to iOS 11.3, and the biggest thing in it is a fix that lets displays fixed by thi ...more
The microphone in a Windows computer is accessible to most applications running on the device at all times and completely without security limitations. Information gathered from recorded audio conversations taking place in the surrounding area of a compromised computer can be ...more
While TouchWiz as an Android skin isn't a favorite among many, Samsung Internet is a fantastic web browser that S9 owners should be happy to have preinstalled out of the box. But you don't need to buy Samsung's latest flagship to try their browser — Samsung Internet is availab ...more
While it may not be an obvious feature, Apple actually built a way into iOS that lets you hide specific pictures and videos in the Photos app that you want to keep on the down-low, for your eyes only. If you show off your photos a lot or stream slideshows to your TV, this is a ...more
This week, saw two companies leaning on AR to prop up their financial futures. On one hand, Apple made quite a bit of AR-related news ahead of its quarterly earnings report next week. On the other hand, Vuzix launched a pre-order program for its Blade smartglasses and closed ...more
With email, one size does not typically fit all. You have multiple email accounts, each for different purposes and with varying levels of importance, so it only makes sense to customize the way your phone alerts you to each account's incoming emails. Luckily, Outlook allows yo ...more
Around this time in 2016, the predictions for the next year had reached something of a consensus: 2017 would be the year of augmented reality. But a funny thing happened on the way to the future — nothing much, really. At least not for the first half of the year. It seemed cl ...more
The Force was awakened in many a household on Christmas morning this year, as evidenced by numerous recipients of newly unwrapped Star Wars: Jedi Challenges systems sharing their first lightsaber battles in augmented reality on social media. In case you've been exiled on Dago ...more
TeslaCoil's Nova Launcher is one of the best home screen apps on the Play Store. It's about as fast as it gets, and it's always among the first to add the latest Android features. However, it looks like Nova Launcher isn't showing users all of the customization options availab ...more
Features like themes and a tab queue make Firefox an extremely versatile mobile browser. Mozilla is constantly adding bonus functionality like this to Firefox, but a long-time staple is perhaps the most powerful feature: Extensions. This system gives you the ability to add fea ...more
With Google's release of Poly API on Thursday, the search giant has found a way to simplify the workflow for AR creators by enabling the ability to integrate its 3D object search engine Poly directly into an application. While services like Turbosquid and Sketchfab, websites ...more
Whether inappropriate or unimportant, some emails don't need to be viewed at a certain times of the day. For example, you might not want to see any personal emails during work hours. By default, Gmail will notify you of all emails that hit your inbox, but fortunately, there's ...more
The iPhone X is sure to be a hot seller this holiday season. You probably know someone with the $1,000 iPhone on their wishlist, and with a price tag that high, Black Friday is probably the best chance of them getting one. But there's only one store we've found so far that's e ...more
Have you ever been listening to the radio and a song comes on that you can't identify? But you're driving, so you can't open your phone and use your favorite app to find the song's name. Well, with a feature called "Now Playing" on Pixel phones, Google has solved this problem. ...more
The number of households in the US that go hungry because they lack money for food hit a high of almost 15% in 2011. While that number continues to decline, nearly 13% of American households still go hungry. Malnutrition — either from not eating enough or not getting enough n ...more
A week into my internship, I experienced pretty serious back pain and slight difficulty breathing. I scheduled a doctor's appointment to make sure nothing was wrong, and I got a surprising diagnosis: bad posture. Yep, slouching at my desk had caused all of my maladies. In an ...more
James Ashley, Atlanta-based Microsoft MVP and author of Beginning Kinect Programming with Microsoft Kinect, has been running monthly challenges since around the release of the HoloLens Developers Kits. Each month, those of us who follow what happens in the community can look f ...more
It's never fun when you install an app and then proceed to be bombarded with constant notifications. The SoundCloud app, while great in other regards, tends to have a bit of an issue on this front. So it's only fair that I share with you how to turn off every single one of th ...more
Pinning a tweet to your profile is a fantastic way to get people to view and engage with your most important content on Twitter. In fact, it could very well be the best way to improve your overall Twitter strategy. Think about it: Every time someone visits your profile page, ...more
Winter is here, which means we have a lot of questions about the coming season of Game of Thrones. It's hard finding someone who cares enough to listen to you rant about why Jon Snow is the rightful ruler of Westeros. It's also hard to figure out who exactly everyone is and is ...more
Supercell's highly anticipated Brawl Stars has soft launched in Canada, with gamers worldwide salivating at the prospect of a full debut around the corner. Unbeknownst to many, this game can be played on your iPhone right now, regardless of where you live. As a testament to t ...more
Every now and then, it's refreshing to play a game that doesn't involve much thinking. Sega is set to bring us just that, as a new game called WWE Tap Mania has soft launched for iOS and Android in the Philippines. As its name implies, lots of mindless tapping will be involve ...more
Fans of Titanfall now have a great alternative to play on their iPhones whenever they're out and about. Titanfall: Assault has arrived as a soft launch for iOS devices. A hybrid between card-based and real-time strategy genres, the game will pit you against other players with ...more
Every party has a pooper, and that's why you're reading this article. We don't mean to be a downer on such a fun day as 4/20, but it's important to make sure you know about the source of your pot, especially if you're one of the 2,299,016 people who use medical marijuana in th ...more
Netmarble's ChronoBlade, a mobile role-playing game, has made its way to iOS and Android by way of a soft launch that will make it exclusive to users in Canada and Singapore for a couple of months. Its console-quality graphics and extra features will surely make it a hit when ...more
Augmented reality could come in very handy for those of us prone to losing things—namely, our wallets. Pixie Technology, a company from Los Altos, California, has developed a way to locate your lost wallet and keys using AR technology and tracking chips, a platform they call t ...more
The Autobots and Decepticons are back as Transformers: Forged to Fight has soft-launched for both iOS and Android. Help Optimus Prime fight corrupted Transformers one on one to save them from their ruthless overlords, and have them join your cause, regardless of which side the ...more
Earlier last week, there were a number of fake five-star WhatsApp reviews to be found on the Google Play Store. Now, Gmail, Chrome, Messenger, and Firefox are all the latest victims to be saturated in five-star spam that wrongly refers to the word "game" in reference to non-ga ...more
Dynasty Warriors has finally been unleashed on the world of mobile gaming. The latest installment in the popular series is called Dynasty Warriors: Unleashed, and it sends you rampaging through armies using a variety of devastating attacks, all while collecting and upgrading o ...more
Before the release of the Galaxy S8, Samsung quietly uploaded one of their core TouchWiz apps to the Google Play Store as a beta. Samsung Internet, as it's called, has been a staple on all Galaxy devices for years now, but you can now try the browser on any Android phone. Aft ...more
Antibiotic-resistant infections that usually occur only in hospital settings are spreading in communities, increasing hospital stays—and danger—for young children. In a study published in the Journal of the Pediatric infectious Diseases Society, researchers from the School of ...more
ProtonMail has long been the favorite of journalists and security-conscious professionals, with Edward Snowden the most famous example. But these days, everyone cares about anonymity, so it's no surprise that ProtonMail currently has over 2 million users. And now the service i ...more
The only way to know which Pokémon are in your area in Pokémon GO is the cryptic "nearby" list, which sometimes doesn't work—and also doesn't tell you which direction to head off to hunt that Pokémon you're looking for. Luckily, there's a new app that makes it a lot easier to ...more
Most augmented/mixed reality hardware still exists in the development stage, whether that's one of the more robust headsets or a high-powered smartphone. Most everything else isn't widely used or monetized. Snapchat, however, snuck in under the radar and created the foundation ...more
Since Ive started to learn about nmap and metasploit and other tools I was learning well but I had one problem, I had nothing to practice it on. As a result I asked someone about my problem and they told me about Vulnhub. It's a great way to practice. Its good beginners and pe ...more
Researchers at MIT's Computer Science and Artificial Intelligence Laboratory have created Wi-Fi technology that identifies where you are, which may eliminate the need for passwords. Video: . The system, called Chronos, can determine where a user is with an accuracy of "tens of ...more
Welcome back, my budding hackers! One of the most basic skills the forensic investigator must master is the acquisition of data in a forensically sound manner. If data is not captured in a forensically sound manner, it may not be admissible in court. In my Kali Forensics seri ...more
This article is to all the newbies on here wanting to become a hacker. Since I have seen many newbie questions on here, I need to address this. Thank You: First thank you for wanting to become a hacker, it is not an easy path. Becoming a hacker, at least in the way that I s ...more
Whether you're anxious to tune into this Sunday's Super Bowl 50 to see Cam Newton and the Carolina Panthers take on Peyton Manning and the Denver Broncos, or to see if you win some money on your silly prop bet, or just want to tune in for the commercials, there are a handful o ...more
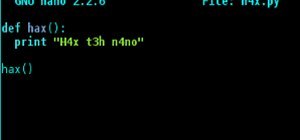
What's up readers? We have ever so slightly touched upon this concept of scope with variables but still don't really know what it means. In this tutorial we will learn the behaviors of variables existing in our programs and within functions. What Is a Variable Scope? A scope ...more
If you've been visiting websites of ill repute, or if you've been Christmas shopping and don't want to spoil the surprise, it would be a disastrous situation if anyone were to come across your browsing history. Visited sites, cookies, and cache can paint a very clear picture o ...more