Thanks to their partnership with Tidal, over 30 million Sprint customers can access Hi-Fi audio on the go. And the Jay-Z-owned music service isn't limited to just Sprint customers — for $19.99/month, anyone can listen to lossless audio from their favorite artists. But streamin ...more
What do Hulu Plus, Pandora, and YouTube all have in common? Ads—and lots of them. Sometimes, an advertisement or two isn't a big deal, but when you're bombarded with them daily on your iPhone, they can get old really quick, and might even lead you to delete the apps entirely. ...more
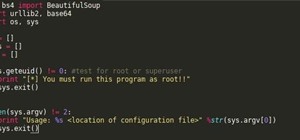
When performing something such as a mass mailer attack on a company, sending executables usually isn't the best option. That's why, in this tutorial, I'll be teaching you how to code a VBA script macro into a Word document in order to compromise a system. Combined with a littl ...more
Hey Everyone! Welcome to my post. We have seen a numerous GUI Tool in kali linux. Armitage, wireshark, Burpsuite etc,. Lets see an another GUI tool. GHOST PHISHER: Open terminal and type ghost-phisher and you will see various tabs ghost phisher has cool features : 1.HTTP S ...more
BeEF is an XSS-exploiting framework that lets you "hook" or gain control of victim web browsers. In this part of XSS exploitation, we will be working on finding an XSS-vulnerable website. We can simply do this by Google Dorking. How It Works XSS is caused when a website "ref ...more
Normally, "restricted access" is something you despise. No one likes to be told they can't do something, especially when it comes to the Internet. Unfortunately, having web access at all times can not only eat away at your wallet, but make your day less productive overall, so ...more
As you might know, Tidal differentiates itself from the competition with its audio quality. Unlike Spotify and Apple Music, it aims to give its subscribers studio quality audio from any device. However, before you sign up for Tidal, be aware there are few steps you need to tak ...more
If you have some photos, videos, and documents that you want to keep completely hidden and encrypted on your Android device, Andrognito is the app you need. We showcased this app in the past, but since then, CODEX has rebuilt it from the ground up with new and improved feature ...more
Google is known for merging older products into a new one's ecosystem for ease of use. The transition can take time, and that's the case with the old Google Wifi system now that Nest Wifi is out. Google is working on phasing out the dedicated Google Wifi app in favor of using ...more
A man-in-the-middle attack places you between your target and the internet, pretending to be a Wi-Fi network while secretly inspecting every packet that flows through the connection. The WiFi-Pumpkin is a rogue AP framework to easily create these fake networks, all while forwa ...more
Need some help figuring out how to put a password on your wireless router? This home-computing how-to from the folks at CNET TV will teach you everything you'll need to know to do just that. For detailed information, and to get started protecting your own wireless network help ...more
The Pixel and Pixel XL come with an awesome data-saving feature called Wi-Fi Assistant that automatically connects to open internet hotspots, then creates a secure VPN on your device to keep your data safe. When you're connected to a Wi-Fi network, internet speeds are general ...more
Smartphones are now indispensable when traveling. Domestic and overseas travel alike require food, navigation, translation, and so much more to make work or vacation successful. Gone are the days of lugging multiple tourist books around with you everywhere you go — you need to ...more
Ever use an open hotspot on your Note 3, only to find out that it's severely restricted to what sites you can access? While getting online with free Wi-Fi is great for those who have a limited data plan, when that one site you absolutely need to visit is blocked, you're left f ...more
Hello NullByte, it's mkilic! This time I'm here with the C.H.I.P from NTC. Although it is not too popular, the C.H.I.P is a brand new micro computer. It is very similar to the Raspberry Pi or Beaglebone Black. The key difference with this particular board is its cost and size. ...more
There are hidden Wi-Fi networks all around you — networks that will never show up in the list of available unlocked and password-protected hotspots that your phone or computer can see — but are they more secure than regular networks that broadcast their name to any nearby devi ...more
This video presents how to connect to your iPod Touch or iPhone using SSH (Secure Shell) without using Wi-Fi connection. 1 Step. Presuming you have Internet connection in your iPhone, click Cydia. Wait for it to load. Type "OpenSSH" without quotes into the search engine. When ...more
Welcome back Hackers\Newbies! Hey guys first of all I would like to explain my absence here in NullByte. I got a little "occupied" with "other things". When I got back, I saw all these HowTo's, articles, Help Questions, I decided, I need to share more of what I have, to you g ...more
My girlfriend was going away for a few weeks, but where she was going, there was no easily accessible Internet. She works mostly on the web, so it was imperative that she have a decent Internet connection during her travels. So, tethering her phone was the only real possibilit ...more
There are many tools out there for Wi-Fi hacking, but few are as integrated and well-rounded as Bettercap. Thanks to an impressively simple interface that works even over SSH, it's easy to access many of the most powerful Wi-Fi attacks available from anywhere. To capture hands ...more
Rooting. As an Android user, I'm sure you've heard the word once or twice. According to Kaspersky, 7.6% of all Android users root — but for the 92.4% who don't, we wanted to talk to you. Rooting allows you to remove barriers and open Android to a level of unprecedented contro ...more
In a era where cyber security is becoming increasingly important, Comcast has decided to use its customers' routers to provide hotspot access to the public. A new program, outlined by Dwight Silverman over on the Houston Chronicle website, seeks to provide Xfinity customers wi ...more
In the 21st century, we're all looking for ways to stay private, especially on our electronic devices. We have big tech corporations, enemy countries, malicious hackers, and other prying eyes watching our every move, so it's only natural to want to limit what they can see. Mak ...more
No more carrying around heavy laptops and thousands of Linux Live CDs and USBs to always be ready for pentesting on the fly! I hope you had a good Christmas and happy new year! Update1: Added the section "weaponizing your Android" where I talk about apps and fundamental Kali ...more
Welcome back, my rookie hackers! When Wi-Fi was first developed and popularized in the late '90s, security was not a major concern. Unlike wired connections, anyone could simply connect to a Wi-Fi access point (AP) and steal bandwidth, or worse—sniff the traffic. The first a ...more
Hak5's products get a lot of attention. Popping up in popular shows like Mr. Robot, their hacking tools are bold proof of concepts with space built into the design for the community to add their own tweaks and modifications. On Friday, Oct. 27, Null Byte attended the Hak5 rele ...more
Unless you have unlimited cellular data, you probably connect your iPhone to every Wi-Fi network you come across. It could be a local coffee shop, public library, or just a friend's place. Wherever it is, you'll need to ask for the access point's password if it's a secured net ...more
Despite the security concerns that have plagued Facebook for years, most people are sticking around and new members keep on joining. This has led Facebook to break records numbers with over 1.94 billion monthly active users, as of March 2017 — and around 1.28 billion daily act ...more
Apple released the latest version of its iPhone OS, iOS 14.6, today, Monday, May 24. This latest update (build number 18F72) introduces new features like unlocking your iPhone with Voice Control after a restart, Apple Card Family support for up to five people, and subscription ...more
The battle between Pepsi and Coke has been a grueling one, with both sides securing their secret formulas for great tasting, addicting sodas behind lock and key. But even big time companies screw up every now and then, and one of the most guarded trade secrets in the beverage ...more
As a web developer, I often read articles about hackers (from the lowly to the knowledgeable) infiltrating websites via the dreaded 'SQL Injection' method and completely taking control, changing, gaining access, or destroying the owner's data. As a fellow web developer, I'm su ...more
It’s called Urophagia—the art of consuming urine. There could be any number of reasons for having the desire to drink your own urine (or somebody else’s). There’s the so-called term “urine therapy,” which uses human urine as an alternative medicine. In urine therapy, or uropat ...more
In a recent arbitrage tip, we showed you the secret to making money fast by buying and selling the same thing over and over again on eBay. But there's one thing you need to know about the buying part—get the lowest price possible! This article aims to show you some of the best ...more
First of all the tutor advises that this is a good idea to do it regularly. It is advisable to drain it out otherwise it shall stop the boiler from working. Before starting your work you have to switch off your boiler. Now allow the water to cool down because it is very hot. F ...more
This how-to video shows you how to open your above ground pool after it has sat there all winter. Make sure to remove water on top of the cover, any debris, and tubing securing the cover. Open your above ground pool and get it ready for summer. Check the skimmer, filter, and p ...more
This how-to video shows you how to open your in-ground pool after it has sat there all winter. Make sure to remove water on top of the cover, any debris, and tubing securing the cover. Open your in ground pool and get it ready for summer. Check the skimmer, filter, and pump be ...more
The padlocks that secure most of America's high-school lockers are one of the easiest types of locks to open in the world for thieves and other miscreants. The easiest, cheapest way to do so is using a shim. These can be bought online, but why both when you can make one yourse ...more
In this how to video, you will learn how to open a 6th generation Ipod Classic. First, make sure to turn it off and make sure the hold button is on. Take a prying tool to undo the clips inside the device by sliding it in between the cover and back. Once the clips are undone, p ...more
Have you locked yourself out of your car? Well, as long as you have a shoelace, you may be able to get back in. Don't Miss: 15 Ways to Open a Locked House/Car Door Without a Key Don't Miss: 6 Easy DIY Ways to Open Your Car Door Without a Key Video: . Pull your shoelace out of ...more
Pokemon's Darkrai is one of the most coveted levels of the game. With this tutorial, learn how to find Darkrai in a few easy steps, as well as secure a Membership Pass and a Mystery Gift in Pokemon Platinum. So grab your Nintendo DS and follow along! The Darkrai event for pok ...more
Wrestling with the whys are wherefores of WiFi? Can't figure out how to secure your network? Take heart: This remarkably thorough, seven-part home networking tutorial will get you up and running faster than you can say `Wireless G.' This video shows how to set up a Linksys wi ...more
Watch this video from This Old House to learn how to replace a pane of glass in a door. Steps: 1 Measure the broken door pane for a new piece of glass. 2 Use a stiff-blade putty knife to pry the wooden stops from around the broken pane. 3 Carefully remove the broken pane from ...more
Don't know the combination to your lock securing all of your important gym socks? Maybe you just want to impress all of your friends by hacking a combo lock? Whatever the reason, this instructional hacking video will show you how to open a lock with a soda can shim the easy wa ...more
Health, safety and security are three main issues which determine if your cruise is a successful vacation. Health Health is a big issue because if one person gets sick, the entire ship can become infected. Gastrointestinal illness is the most common illness aboard cruise sh ...more
This video shows you how to use Skype on your iPhone 3G or 3GS. As you know, Skype (from app store) can only be used on wifi. This video shows you how to use 3G Unrestrictor (from Cydia) so that you can make calls using Skype on 3G. Combine this with Backgrounder (Cydia app) a ...more
Steve with Eikenhout Educational Video Series and Paul Griggs with PGriggs Construction demonstrate how to install new windows during a new construction application. You will need a level, a utility knife, a caulk gun and a hammer to install the windows. First, cut the house w ...more
Systm is the Do-It-Yourself show designed for the common geek who wants to quickly and easily learn how to dive into the latest and hottest tech projects. They will help you avoid pitfalls and get your project up and running fast. In this DIY episode, see how to build a firewa ...more
Watch this video from This Old House to learn how to prevent frozen pipes. Steps: 1. Seal air-leaking holes and cracks around home with expanding foam sealant or silicone caulk. 2. Use foam-rubber pipe insulation to protect exposed pipes from cold. 3. Slip foam-rubber insulat ...more
TrueCrypt is a free open-source program for encrypting data and it's excellent for securing hard drives, but it also has the ability to hide a secret operating system inside another operating system. CNET shows you how this "insider secret" operating system is created. This op ...more
In today's time of rampant IT crimes, including identity theft, security is more important to the average computer user than ever. This tutorial, which was recorded and encoded for the Internet usingly only open source tools, demonstrates how you can use GnuPG to secure and ve ...more
This video tutorial will explain you how to secure a USB thumbdrive (or flashdrive) using the free, open-source encryption software TrueCrypt.
In this video from Lowe's we learn how to use a gas smoker. This tip comes from Lowe's. You can cook with a smoker anytime of year. He is using a gas smoker. Keep this away from siding. The fire source heats the moist wood chips, which release the smoke that flavors the food. ...more
This is a tutorial showing you how to mod a ps2 slim. This will allow you to play backups as well as Guitar Hero 2 customs. If you want to learn how to make your own copy I might put up a video for that. This tutorial also shows the swap trick in action. -I am not responsible ...more
In this tutorial, we learn how to make a photo cube. This project can be done in a couple of hours and only costs a couple of dollars! To start, you will first get an exact measurement of the width of your wood. After marking these, you will cut the wood using a band saw. Afte ...more
FaceTime is a very cool Apple App that makes video chat possible on the iPhone, but only if you're on a wifi network. Officially, at least! One of the many cool things that you can do after your jailbreak you iPhone 4 is use FaceTime on the 3G network! This quick video will sh ...more
In this clip, learn how to tether your rooted Droid to a WiFi network and use it as a modem for your other Wireless devices. This process is pretty easy and only requires a network and that your phone be rooted. Step 1: Just download the Wireless Tethering APK to your compute ...more
Mark Bittman shows us how to make Matambre, an Argentine dish, also known as Stuffed Flank Steak. Take a piece of flank steak and make a shallow cut about halfway down the thickness of the meat, and two perpendicular cuts on either end, then open it up into a large thin piece ...more
This video illustrate us how to make a hovercraft with common household items. To build one, first of all, collect all of the items required for making it. You need a CD, bottle cap, balloon and super glue. Then start by applying glue to the lower end of the cap and sticking i ...more
The trucker's hitch is a good, strong knot with many uses. It's ideal for securing a load in a vehicle, and was used that way dating back to the days of wagons hauled by horses. In this video the folks at ITS Tactical teach you how to tie a trucker's hitch, quick and easy. IT ...more
Hak5 is at it again, with a plethora of somewhat accessible solutions to your technological problems. If you've ever needed to get through your school's firewall, or secure traffic tunneling, or try out applications in a fast, efficient manner? This video has it all and more. ...more