In my previous article, we learned how to generate a vulnerable virtual machine using SecGen to safely and legally practice hacking. In this tutorial, we will put it all together, and learn how to actually hack our practice VM. This will provide some insight into the methodolo ...more
How to make eggshell planters. Great fun to do with the Kids this Easter Step 1: Watch This Video Guide Full instructions for how to make these eggshell plant pots given in this short and simple video guide. Video: . What you need: An Eggs Egg Cup A knife Kitchen Paper Cress ...more
If you grew up dying eggs for Easter, you've no doubt used or at least seen those boxed kits that turn your eggs neon colors. Admittedly, they're easy—just plop a dye tablet into some water, dunk the eggs, and wait for them to dry. But the one thing a lot of people don't thin ...more
This is an awesome little science trick that has to be seen to be believed. Simply by emptying a bottle of "supercooled" water into a glass, you can watch it turn into ice right as your pour! It's no magic trick or chemical craziness—it's normal water and you can try it yourse ...more
Nowadays, it feels like you can't talk about eating healthy without bringing up quinoa. Quinoa (KEEN-wah) has been the "superstar" of the health movement for a while; 2013 was declared the International Year of Quinoa by the United Nations, and has only continued to grow in po ...more
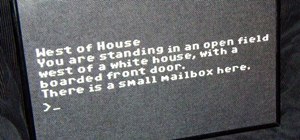
Welcome back, my fledgling hackers! Sometimes, for a variety of reasons, we can only get a command shell on our target system. For instance, with Metasploit, it's not always possible to get the all powerful Meterpreter on our target system. In other cases, we may be able to c ...more
I've always had an affinity for pretty wine bottles. When I was younger, my parents and my siblings would give me their empty wine bottles so I could collect them, and I loved every single one. Of course, once I reached a certain age, I realized that I loved what resided in t ...more
Popping a shell is often the main goal of a hacker, and it can be exciting when executed properly, but sometimes they do have their limitations. Metasploit's Meterpreter probably needs no introduction, but this powerful, dynamic payload can offer a leg up over normal shells. T ...more
Welcome back, my novice hackers! Before we try to attack a website, it's worthwhile understanding the structure, directories, and files that the website uses. In this way, we can begin to map an attack strategy that will be most effective. In addition, by knowing what files ...more
Cross-site scripting is one of the most common vulnerabilities found on the web today, with repercussions of this type of flaw ranging from harmless defacement to sensitive data exposure. Probing for XSS can be tedious and time-consuming for an attacker, but luckily there are ...more
Mockingjay - Part 2, the final film in the Hunger Games series, hits theaters next month, and what better way to celebrate one of the series' most fabulous characters than with an over-the-top costume this Halloween? Effie Trinket, played by Elizabeth Banks, is just as memora ...more
The options for customization are virtually endless when you're rooted and have an unlocked bootloader and custom recovery. However, there is always risk involved when flashing new mods or installing new ROMs. I always make backups in case something happens, but when I'm testi ...more
A fire snake, also referred to as a black snake or sugar snake, is a classic science experiment you can do right in your own kitchen using a baking soda and sugar mixture and a fuel to ignite the reaction. When the baking soda gets hot, it makes carbon dioxide gas. The pressu ...more
Welcome back, my greenhorn hackers! Continuing with my series on how to crack passwords, I now want to introduce you to one of the newest and best designed password crackers out there—hashcat. The beauty of hashcat is in its design, which focuses on speed and versatility. It ...more
Welcome back, my apprentice hackers! In this series on password cracking, I have been attempting to develop your skills in the age-old art of password cracking. Although it might seem like a simple and straightforward exercise, those of you who have attempted password crackin ...more
Welcome back, my fledgling hackers! A short while ago, I did a tutorial on conducting passive OS fingerprinting with p0f. As you remember, p0f is different from other operating system fingerprinting tools as it does not send any packets to the target, instead it simply takes ...more
Amazon's Appstore has come a long way since it launched in 2011, with over 250,000 apps to its name. That being said, their app numbers pale in comparison to Google's Play Store, which currently boosts over 1.3 million apps. But the Kindle runs Android as a base, so there's n ...more
Speed Eater Joey Chestnut beat six-time reigning world record holder Takeru Kobayashi, eating 66 hotdogs in only 12 minutes in July 2007. How can we not admire his repulsive skills? In this Time Magazine video, he dishes secrets on HowTo speed-eat. Basically, it takes rhyth ...more
The Google Chrome browser for Android allows you to cast quite a few different videos from the web to your TV, but some sites actively disable this functionality, and others have outdated video players that won't allow for it. For example, Instagram's mobile website won't let ...more
If you took your favorite search engine, gave it a witty personality, and bundled it together with a messenger-style interface, you'd have the new Google Assistant. It's great for getting fast answers—even on your follow-up questions—but its flair for fun might just be the sta ...more
Warm water is an essential part of life that we sometimes tend to take for granted. Over one billion people, or roughly one-seventh of the world's population, have no access to hot water. Warm water is not only comforting when showering and bathing, but also helps the body ge ...more
When I left off on our last hack, we had hacked into the ubiquitous Windows Server 2003 server by adding ourselves as a user to that system so that we can return undetected at any time. The problem with this approach is that a sysadmin who is on their toes will note that a new ...more
We all fall sleep in different ways. Some may require absolute silence, others need white noise, and some enjoy listening to a song or two to help bring on the sleep. If you're in the latter group, like I am, there's a problem. Fall asleep before the music stops, and a loud so ...more
Welcome back, my budding hackers! When we are looking for ways to hack a system, we need a specific exploit to take advantage of a certain vulnerability in the operating system, service, or application. Although I have shown you multiple ways to exploit systems here in Null B ...more
Two slices of whole-wheat toast with lots of butter. Two eggs, poached to a firm yet custardy texture. The yolks should absolutely not be hard-cooked and the whites should be tender, not rubbery. That's my idea of the perfect breakfast. A golden, runny-but-not-liquid yolk, cre ...more
In this video, I will show you how to make copper glow red hot with the catalytic oxidation of acetone. For this science experiment, we'll just need some acetone, copper wire, and a flame source to initially heat the copper coil we'll make. Video: . Materials Needed Pure acet ...more
Baking powder and baking soda are two staples almost everyone has around that seem to last forever. But a lot of people don't know that they eventually start to lose their potency after enough time on the shelf. If you can't remember when you bought it, it's probably time for ...more
There are many password-cracking tools out there, but one of the mainstays has always been John the Ripper. It's a powerful piece of software that can be configured and used in many different ways. Metasploit actually contains a little-known module version of JTR that can be u ...more
Welcome back, hacker novitiates! In the next few hacks, we will be breaking into Windows servers. In this installment, we will learn to add ourselves as a user to a Windows 2003 server. Of course, when we have added ourselves as a user, we can come back any time and simply log ...more
While seltzer water is commonly consumed as a beverage (and a healthier alternative to carbonated soda), it is less known as a fantastic addition to many familiar recipes. The bubbles in seltzer water expand when heated, and when added to certain foods, it instantly allows the ...more
How many of us actually drink enough water? It's one of the easiest ways to improve your health, but most people don't get nearly as much as they should. We've grown so accustomed to soda, coffee, and sugary juices that water just seems bland by comparison. That's why drinks l ...more
Video: . Step 1: Ingredients Cod filets (1 Pound) Olive oil (1/4 Cup 4 tbs) Onions (3 Large) Parsley leaves (1) Step 2: Directions In order to desalt your cod, you would normally leave your fillets in cold water for a period of 12 hours, but there is a way around that. -Cu ...more
Confession: I love bagels. I love to make them, but above all, I love to eat them. In college I ran a mini-bagel business from my kitchen, and on bagel-making day, it wasn't uncommon for me to eat the circular goodies for breakfast, lunch, and dinner. Yet even with my obsessio ...more
The outer skin is nearing completion with only one more lava panel to go (in addition to 2 more water panels on the inner-sphere, but they're a cinch compared to the 1-2 month slog each lava and double-glass panels take to make). I'll post a longer (video) teaser showing the ...more
Only three things in life are certain: death, taxes, and getting a dent in your car or truck. Even if you're as careful as possible, you can't always account for runaway shopping carts, wrongly thrown footballs, out-of-nowhere light posts, and other real-life annoyances. Howe ...more
Welcome back, my tenderfoot hackers! Those of you who have been reading my posts here for awhile know how much I emphasize good reconnaissance. Novice hackers often jump into a hack/exploit without doing proper recon and either fail or get caught. Experienced and expert hacke ...more
Welcome back, my budding hackers! Metasploit, one of my favorite hacking/pentesting tools, has so many capabilities that even after my many tutorials on it, I have only scratched the surface of it capabilities. For instance, it can be used with Nexpose for vulnerability scann ...more
If I told you to follow as many users as you could possibly follow, in order to get more Instagram followers, that may seem counterintuitive, right? If I told you I'm trying to brainwash/annoy you with how many times I could possibly say versions of the word "follow" in an ope ...more
Despite being disgusting, houseflies are actually beneficial to humans in a few ways. As scavengers, they help the environment by eating rotting organic matter, and make great food for pet tarantulas. Regardless of the advantages to their existence, having them in your home ca ...more
Want to make your own glass drinking cups? You don't need to be a glassworker to get creative. Just recycle some of your old beer, soda, or wine bottles into stylish toothbrush holders or glass cups. You can tie a loop of string that was dipped in nail polish remover around a ...more
Have you ever put together a basic survival kit for your home in case of an earthquake or natural disaster? If not, you should, because you'll want to be prepared should the worst happen. To cover your bare minimum necessities, gather at least seven days' worth of non-perisha ...more
Lenovo, the company that now owns Motorola, just announced two new entries in their wildly successful midrange Moto G series. The Moto G5, and its bigger brother, the Moto G5 Plus, were both shown off in detail at Mobile World Congress 2017 in Barcelona, Spain. Highlights for ...more
There are a lot of reasons for wanting to make sure your herbs last a long time. Maybe you know that your grocery store won't have decent parsley in the winter. Maybe you're taking a last-minute trip and don't want to throw away your perfect batch of basil. Or perhaps you're s ...more
We all have our favorite cooking oils, but not everyone knows that they're not all interchangeable. Each type of oil is best for certain jobs, and they all have different smoke points and flavor profiles, which are the two most important criteria in determining which one to us ...more
Amazon thinks that by simply removing an app from their Appstore, that they will stop users from accessing it. But with Android OS powering their Fire TV Stick and Fire TV, there really isn't anything they can do to prevent us from sideloading an APK onto the streaming media d ...more
The Problem If you are working on a car restoration project, then you are going to faced with rust damage. This problem can’t be overlooked, as the entire project depends on repairing and eliminating rust. This would be like laying down new carpet to a house that was flooded, ...more
WonderHowTo house favorite, Sam Nouyoun gives the lowdown on "fuming" super glue to develop latent fingerprints on smooth surfaces. What? How? The cyanoacrylate (the chemical in Superglue or Krazy glue) attaches to the water molecules in the steam. When it comes in contact w ...more
Having an efficient workflow is an integral part of any craft, but it's especially important when it comes to probing apps for vulnerabilities. While Metasploit is considered the de facto standard when it comes to exploitation, it also contains modules for other activities, su ...more
In Guardians of the Galaxy Vol. 2, Mantis resides in the shadow of an Ego who considers himself the actual heart of the universe. But when it comes Halloween costumes? Mantis will be the center of attention every time. The internet sure has noticed Mantis, and it's abuzz with ...more
To make soap, you need fat, and if you've seen Fight Club, you're probably well aware of where soapmaker Tyler Durden got his fat from. Liposuction clinics. If you're not willing to go that far for a perfect bar of homemade soap, you can just use some drain cleaner and America ...more
It appears that the new AR app from LEGO is inching closer to release. LEGO had the unique distinction of being featured on-stage by both Apple and Google to show-off the capabilities ARKit and ARCore, respectively. While the latter is still in a preview and available to only ...more
Your Xbox Wireless Controller is a great way to play games on both Xbox One consoles and Windows 10 computers. However, you don't need to have any of those devices to enjoy your controller with your favorite games — you can seamlessly connect the Xbox Wireless Controller to yo ...more
There are some ingredients I cook with so often I can never buy too many of them, and most of them are produce. Onions, garlic and fresh herbs are staples in a lot of dishes, and they may be inexpensive, but when you use them on a daily basis it can add up. Some foods are eas ...more
We're basically living in the future, so let's work like we are. For decades, we have, without question, opened a word processor like Pages, and clicked or tapped our way to starting a new document. What's wrong with that? It's unnecessary. We all have a digital assistant livi ...more
Your English teacher is a creep. The way he looks at your girlfriend, the way he always spends ages with the girls in the class going over their work but not the boys, just the way he is. You want to get rid of him, but you need some proof first. Step 1: Fire Up Kali If yo ...more
Coffee is a topic that everyone has a strong opinion about, especially when it comes to brewing the perfect cup. Even if you buy the best beans and grind them yourself, chances are you're skipping one necessary step to make sure your coffee tastes the best it can: cleaning you ...more
Believe it or not, you can put your money to use very efficiently in a new way: your credit or debit card can serve as a blade in desperate situations. (It might even be handier than dental floss as a brilliant substitution for specialized kitchen tools.) While I wouldn't take ...more
Commonly used for washing and scrubbing dirty dishes, the ubiquitous kitchen sponge can also be used to sprout seeds, loosen wallpaper, remove oil leaks, deodorize your fridge, and more. The porous, absorbent nature of the sponge also makes it perfect for keeping your vegetab ...more
One of the most popular things to do on Snapchat is to earn a Snapstreak. This occurs when you and one other friend have sent snaps (not chatted) to each other within 24 hours for at least three consecutive days. One you've passed the three-day mark, then you and your friend w ...more
Sound Recognition was introduced with iOS 14, and the accessibility feature uses on-device intelligence to detect 13 different sounds and then notify you whenever it hears one. Apple increases that number to 15 with the addition of two more detectable sounds in iOS 15 that it ...more