In this Computers & Programming video tutorial you will learn how to optimize a PC for the best performance. Head over to Smart PC Utilities and click on downloads. Here you can download and install Vista Services Optimizer. This works perfectly well for Windows 7 as well. Ope ...more
George3694 will show you how to jailbreak an iPhone or iPod touch firmware 3.0. This will work on the iPod touch first and second generation, the iPhone original and 3GS. Download Red snow software from the link provided. Click on browse download firmware and put it on your de ...more
Before cutting the rotors select a centering cone that fits about halfway through the center hole of hub-less rotor or bearing spacer to center the rotor to the spindle. After select two identical clamps that fit the rotor without interfering with the machined surfaces of the ...more
The joys of summer are many! If you, like me, live in a place where the summer is short, you’re going to want to maximize your fun in the sun by doing as many awesome things as possible before the sun goes back to wherever the hell it hibernates during the cold and dark times. ...more
It's been an eventful week for Google+. Facebook decided to up its game and start rolling out several major updates intended to address privacy concerns. We got a glimpse into the future of Google+ via an insightful discussion between +Bradley Horowitz and +Tim O'Reilly. And G ...more
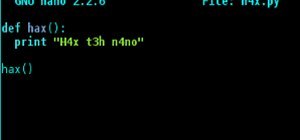
This morning, I received a message from a friend who was reading a hack log, and she had some questions about the commands used. This got me thinking, as Linux has a ton of commands and some can be archaic, yet useful. We are going to go over everything you need to know to rea ...more
A lot of different places have computers with controls on them for several things; some have controls for installing software, some for running software, blocking websites, opening certain file formats, etc. Obviously, not all places use the same methods, and not all of the m ...more
In this tutorial, Tom Howard shows us how to bleach jeans the proper way. This is far better than just placing your clothes in the washing machine the normal way. To do this the correct way, put your water level low (for one item) in your washing machine. Now, make sure the te ...more
Remove all those dust mites and pet dander from your pillows on a regular basis with a good wash in hot water. Pillows can be a little trickier to wash than other linens so keep you pillows fresh and new by following proper washing instructions. Pillows should be washed every ...more
In this video series, our expert homemake Betsy Sue, will teach you how to do laundry. Get step-by-step instructions for sorting dirty clothes, getting rid of stains and using the washing machine settings. You will also get tips for drying laundry, using dryer sheets and even ...more
In this DIY home improvement video series, learn how to pressure wash the exterior of your house—as well as the sidewalks, driveway and deck. Our expert will show you where to get a pressure washing machine, how to hook it up, what wands and tips to use, and how to start the p ...more
There are several virtual machine managers present in the market. However, the main functionality of all VMs are the same. Most people like to get free VM managers, so that they can install as many operating systems as they like over the host operating systems. One of these fr ...more
How to build an outdoor, homemade fire pit out of an old washing machine drum! It looks great and works fantastic. Fire pits are conventionally made from stone or bricks and as the name suggests, are made into a pit in the ground. The fire pit that l have just built is a littl ...more
We already know that Samsung's Galaxy S7 is one of the most versatile smartphones ever made, complete with edge-to-edge displays, water resistance, and a huge battery. But what's versatility without durability? How much punishment can the Galaxy S7 take? Let's play a game of S ...more
Whether it's the start, middle, or end of summer, it's prime-time grilling season. If you find yourself without a grill, however, it may seem as if half your summer plans of swimming by the pool while stuffing hot dogs in your face could be ruined. But have no fear as all is ...more
It feels great to wrap up in a big, fluffy towel after a steamy shower, but it's frustrating when that towel isn't quite up to the job. Over time, towels lose their ability to hold water and dry as needed thanks to daily use and the biggest culprit—laundry detergent. Why Laun ...more
Sometimes you just want to grill. It doesn't matter where you are, what you have, or whom you're with—you just want a delicious burger and you don't care what it takes. If you don't have a home grill or you're out camping in the wild, then it's the perfect time for your MacGy ...more
Is your favorite black T-shirt starting to look a little old? To restore a faded black fabric color to its former glory, add two cups of brewed coffee or black tea to your washer's rinse cycle. If you have the opposite problem and need to make your dirty white tees look super ...more
Genius or retard? Such an impossibly fine, fine line. Imagine if MacGyver got hit by a hillbilly stupid stick. Extremely amusing. And yes, washing machine parts are integral to this design!$%^&. Here's the tutorial: DIY%20a%20redneck%20roller-coaster. And here's the 'proof' ...more
Even if you decode the laundry symbols on the tags of your clothes and follow them perfectly, using the washing machine tends to change their shape and fade colors over time. And whether you spent $20 or $200 on them, there's nothing worse than having your favorite pair of jea ...more
Dry cleaning can be a pain the butt, not to mention super expensive, especially if you're wearing a lot of wool sweaters during the cold winter season. Thankfully, with a little time and effort, you can wash most of your "dry clean" or "dry clean only" clothing at home. Cotto ...more
There are countless methods and cleaners aimed at eliminating stubborn stains from everything to clothing, carpet, and furniture. But completely removing every last trace of a stain doesn't require an arsenal of chemical cleaners and repeated cycles in the washing machine. Mos ...more
You know how annoyed you get when you put a quarter into the vending or washing machine and it gets stuck? There's a quiet rage that boils inside you. Now, imagine that quarter is a sixty dollar video game, and it's stuck inside your brand new, four hundred dollar PlayStation ...more
Of all the places you'd think to check for bed bugs, I doubt that library books would be at the top of your list. As odd as it sounds, though, libraries and library books are some of the most common places for bed bug infestations. Libraries all over the country have reported ...more
Whites are the hardest color to keep looking bright and new after just a few months' time. Your sweat and oils quickly become stains, and colors from other clothes will eventually bleed into the fabric, discoloring your bright whites into something merely whitish. But before y ...more
You've been there. Those precarious few seconds between dropping your expensive smartphone right on its face and reaching down to survey the damage. Or maybe you got thrown in a pool while your device was in your pocket, or you dropped that sucker right into the toilet bowl. H ...more
Unless your work clothes require dry cleaning, you probably only go to the cleaner a few times a year. And for those few items in your closet for which you do, you have to then find the time and extra budget to make a trip all the way to the cleaners and back again. In the end ...more
The origins of vodka are shrouded in mystery, with both Russia and Poland laying claim to its invention. Some say Genovese merchants brought vodka (then known as aqua vitae, or the water of life) in the late fourteenth century to Russia. For many years, vodka wasn't just an al ...more
The easiest way around a security policy is to find users who don't follow it. The Have I Been Pwned database identifies accounts with information breached by major third parties like Yahoo and LinkedIn. With Maltego, hackers can locate breached accounts created using company ...more
The internet is constantly under siege by bots searching for vulnerabilities to attack and exploit. While conventional wisdom is to prevent these attacks, there are ways to deliberately lure hackers into a trap in order to spy on them, study their behavior, and capture samples ...more
Containers are isolated software instances representing applications, servers, and even operating systems—complete with all of their dependencies, libraries configuration files, etc.—and they're taking over the corporate world. The ephemeral, portable nature of containers help ...more
Metasploit is an extremely popular pentesting tool capable of enumeration, exploitation, and injecting shell code, and is a part of almost every hacking toolkit. So there's no way I could leave this out of our series on getting your Mac set up for hacking. Luckily for those o ...more
We're almost there to completing the setup of your Mac for hacking! Now that we have Git and Homebrew under our belts, it's time to take on something fairly easy, but very important for our hacking needs. Ruby is an object-oriented scripting language used to write powerful pr ...more
In the first part of my containers series, we learned how to install Docker on our local machine, pull down "hello-world" and Ubuntu containers, SSH into containers, and install software when in a container. Now, we're going to work on building, customizing, and storing our re ...more
While modern browsers are robust and provide a lot of functionality, they can be unlocked to do some pretty spectacular things with browser extensions. For hackers and OSINT researchers, these tools can be used to defeat online tracking, log in to SSH devices, and search the i ...more
In 2013, Offensive Security released Kali Linux, a rebuild of BackTrack Linux derived from Debian. Since then, Kali has gone on to become somewhat of a standard for penetration testing. It comes preconfigured with a collection of tools accessible by a menu system, tied togethe ...more
Android 7.0 Nougat has finally arrived—well, technically, it's in the process of arriving on Nexus devices across the globe. Google uses a staged rollout system to prevent excessive server load when issuing Android updates, which means even though Nougat has made its official ...more
I was on our new #nullbyte IRC channel when someone told me how tedious it is to install an OSX Virtual Machine on Virtual Box (I think it was wawa). We all know Linux rocks (gets acknowledgement from the crowd), but there are morons out there, multiplying at a never before se ...more
Welcome back, my hacker novitiates! Many of you have written me that you're having difficulty installing and running Metasploit on a variety of platforms. No matter if you're using Mac, Linux, or Windows, I strongly recommend you install BackTrack as your secondary OS, a virt ...more
INTRODUCTION Hello dear null_byters here we go again with our third part of this serie. in this third part of our series I'd like to do a demonstration or continuation on fuzzing, but I think I should leave for later because the next tutorials about fuzzing will require from ...more
Cross-site scripting is one of the most common vulnerabilities found on the web today, with repercussions of this type of flaw ranging from harmless defacement to sensitive data exposure. Probing for XSS can be tedious and time-consuming for an attacker, but luckily there are ...more
Local port forwarding is good when you want to use SSH to pivot into a non-routable network. But if you want to access services on a network when you can't configure port-forwarding on a router and don't have VPN access to the network, remote port forwarding is the way to go. ...more
This is the best how-to's website that I've ever seen, and I wanted to join it. It taught me a lot, but, because I'm here to learn too, please correct me if I'm wrong. You probably know that Ettercap is a very powerful tool for man in the middle attacks. You probably know tha ...more
With tools such as Reaver becoming less viable options for pen-testers as ISPs replace vulnerable routers, there become fewer certainties about which tools will work against a particular target. If you don't have time to crack the WPA password or it's unusually strong, it can ...more
Electronic warfare tactics work by jamming, disrupting, or disabling the technology a target uses to perform a critical function, and IoT devices are especially vulnerable to attacks. Wireless security cameras like the Nest Cam are frequently used to secure critical locations, ...more
Hello friends! This tutorial will teach you how to build a local pentesting lab on your Linux machine which will enable you to easily install common web applications so you can practice locating and exploiting their known vulnerabilities (or discover new ones!). In particular, ...more
OpenBSD implements security in its development in a way that no other operating system on the planet does. Learning to use the Unix-like operating system can help a hacker understand secure development, create better servers, and improve their understanding of the BSD operatin ...more
There's no doubt Kali has established itself as the most popular penetration distribution available. However, just because it's the fan favorite of beginners and security researchers doesn't make it right for everyone. Manjaro Linux is a beginner-friendly Arch-based distributi ...more
While SSH is a powerful tool for controlling a computer remotely, not all applications can be run over the command line. Some apps (like Firefox) and hacking tools (like Airgeddon) require opening multiple X windows to function, which can be accomplished by taking advantage of ...more
Configuring onion services for the first time can be tricky. A surprising number of system administrators make seemingly trivial mistakes that ultimately lead to catastrophic cases of de-anonymizing supposedly anonymous sites on the dark web. OnionScan is a tool designed to id ...more
Command injection is a technique used by hackers to execute system commands on a server, usually via a web application or some kind of GUI. This can happen when an application provides some sort of functionality to the user involving the use of system commands. When the input ...more
One of the best features of Android is the fact that it's open-source, giving developers the ability to use it on pretty much any device they can think of, like on a Windows PC using Andy. That's what drove the creators behind the Android-x86 project to port over the mobile OS ...more
It's easy to run Kali Linux from a live USB on nearly any available computer, but many publicly accessible laptops and desktops will be locked down to prevent such use. School, work, or library PCs can be secured with a BIOS password, which is often an easily recovered default ...more
Welcome back, my budding hackers. So many of you are interested in hacking Wi-Fi that I have decided to revisit my Wi-Fi Hacking series with some updated and more in-depth material. I strongly suggest that you look at some of my earlier posts, such as "Getting Started with Te ...more
PowerShell Empire is a post-exploitation framework for computers and servers running Microsoft Windows, Windows Server operating systems, or both. In these tutorials, we will be exploring everything from how to install Powershell Empire to how to snoop around a target's comput ...more
Hello Everyone! I wanted to share a free and open source note taking tool that I've been using for quite some time now. From what I can tell, it's a very safe a secure method keeping passwords, links, and personal stuff encrypted and online. TURTL https://turtl.it Turtl is ...more
Web applications are becoming more and more popular, replacing traditional desktop programs at an accelerated rate. With all these new apps out on the web comes various security implications associated with being connected to the internet where anyone can poke and prod at them ...more
After a long hiatus, we shall once again emerge from the shadowy depths of the internet to build an exploit. This time, we'll be looking at how to defeat a non-executable stack by using the ret2libc technique — a lean, mean, and brilliant way of exploiting a stack overflow vul ...more
WordPress did not become what is arguably the most popular blogging and CMS platform on the planet because it was difficult to use. Rather, its user-friendly and rich feature set led to it finding a home on somewhere north of 70 million websites—and that's just counting blogs ...more
Hi there again, aspiring hackers (and veterans as well)! I'm going to explain how to perform a dictionary attack on a WPA/WPA2 protected network with Wifite. Please note that this doesn't work with WPA Enterprise For that end, you'd have to use an Evil Twin to get the "Enterpr ...more