In this video, the poster is teaching YouTube users how to use Daemon Tools mount games image files. That’s very useful to many people that cannot burn ISOS or any other image files into a blank media (CD, DVD). With the tips provided by this video, anyone can use Daemon Tools ...more
Let's face it, CDs and DVDs are a thing of the past. We no longer use them as a storage medium because they are slow, prone to failure in burning, and non-reusable. The future is flash memory. Flash memory is cheap, fast, and efficient. Eventually, flash drives might even repl ...more
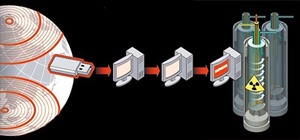
There are lots of Linux distros out there. Normally, you'll have to download the ISO and then burn the image onto a CD. But nowadays, it's easier and cheap to install it on a USB drive. A multiplatform program called UNetbootin can install a variety of Linux distros on a USB. ...more
This video tutorial from ozz3141 presents how to copy your DVD library to a Mac computer. To start, insert DVD you want to copy. It will mount on Desktop and DVD player will open. Close DVD player. Click File-New Finder window. From left pane select applications. Scroll down ...more
Need to back up all those XBox 360 games you've "purchased?" Hey, we're not gonna judge! Whatever your intentions, learn how to burn your precious games with Stealth Patch in this instructional video. Don't worry - your secret is safe with us. What You Will Need: +R Dual Layer ...more
Thanks Anonymous User For This Article, Not Bad Ok SoftzZz...!.!.!.: Step 1 Antivirus The best freeware antivirus is AVG Anti-Virus Free Edition 2011, and you can get him from this site. Step 2 Optimizing tool For me CCleaner is the easiest way to do some things, like: 1. ...more
With the mass arrests of 25 anons in Europe and South America, and the rumors of an FBI sweep on the east coast of America floating around, times look dicey for hackers. Over the past few days, a lot of questions have been posed to me about removing sensitive data from hard dr ...more
The Ubuntu CD does not contain much in terms of software applications. So how can we incorporate other programs that would be made available after booting from a live CD? There is a program called Remastersys. This program creates an .ISO image of the Linux system installed ...more
In this video tutorial, you will learn how to mount and unmount an .ISO, .bin and .cue image with daemon tools. This is useful because when you download a game, movie or an application, you usually get an .ISO, .bin or .cue file. 1. First you must search in Google "Daemon Tool ...more
In this video tutorial, viewers learn how to completely format a hard drive. Begin by downloading the Knoppix Live Boot CD. Then burn the newly download ISO onto a CD as a bootable disc. Use your BIOS to tell your computer to boot from the CD-ROM instead of the hard drive. Wit ...more
In this how to video, you will learn how to use Daemon Tools Lite. First, download Daemon Tools Lite and install the program. Next, download an ISO file from the internet. Once that is done, mount it on to Daemon Tools. To do that, open the program and then right click on it. ...more
Askabouttech shows how to mount an ISO with Daemon tools using Ubuntu. Right click on Daemon Tools in the tool bar and select "virtual CD rom". This will bring up a side window in which you will click "device". This will open another side window where you will click "mount ima ...more
In this video the tutor shows how to mount an ISO using Daemon tools. Using daemon tools you can install virtual drives and mount ISO files on them. First download and install the daemon tools from the link given in the video. After installing right click the daemon tools icon ...more
In this video the tutor shows how to mount ISO's using Power ISO software. To do this follow the simple procedure shown in this video. Download the Power ISO program from the link given in this video and install it. You need to purchase the key to install the software or you c ...more
In this video series, watch as computer expert Franklin Hitchcock teaches how to use the Nero Product Suite. Learn how to burn data CD's and DVD's how to compress and capture video and audio, the different settings and panel options, how to adjust burn speed, how to use Nero E ...more
This is my list of programs that I must have on my PC, but I think you can also use them, so here is the list: Antivirus The best freeware antivirus is AVG Anti-Virus Free Edition 2011, and you can get it from this site. Optimizing tool For me, CCleaner is the easiest way ...more
Did you know Kali 1.0.8? You probably did, and you probably know about the EFI boot option that has been added. That's a very interesting new feature because it allows Kali to be easily booted on Mac too, and every EFI-supported device. First three preview lines gone? As alw ...more
No more carrying around heavy laptops and thousands of Linux Live CDs and USBs to always be ready for pentesting on the fly! I hope you had a good Christmas and happy new year! Update1: Added the section "weaponizing your Android" where I talk about apps and fundamental Kali ...more
If you have never heard of a Virtual Machine (VM) before you might think it to be some new kind of gamers virtual reality system, and that would be incorrect. A virtual machine is a Virtually a real computer that exists inside of your own computer. You can run Kali inside of a ...more
I was on our new #nullbyte IRC channel when someone told me how tedious it is to install an OSX Virtual Machine on Virtual Box (I think it was wawa). We all know Linux rocks (gets acknowledgement from the crowd), but there are morons out there, multiplying at a never before se ...more
Being able to write your own hacking tools is what separates the script kiddies from the legendary hackers. While this can take many forms, one of the most coveted skills in hacking is the ability to dig through the binary files of a program and identify vulnerabilities at the ...more
Don't think because your MacBook is using FileVault disk encryption your device is secure or immune to hackers. Here's how to find out if that FileVault password is strong enough to withstand an attack from a motivated attacker. FileVault, created by Apple in 2003, is a hard ...more
Last week, I updated VirtualBox on my computer since I had skipped a few versions, then I could no longer copy text or paste text from my Kali virtual machine to my host OS and vice versa. Installing the Guest Additions didn't seem to do anything, and the bidirectional shared ...more
Yesterday, I wanted to remove BackTrack from my system and install Kali, and at the same time didn't want to damage my Windows 7 or my hard drive. I searched a lot of articles, but almost all of them wanted me to have a backup Windows 7 CD, which I don't possess. So, I decide ...more
One of the best features of Android is the fact that it's open-source, giving developers the ability to use it on pretty much any device they can think of, like on a Windows PC using Andy. That's what drove the creators behind the Android-x86 project to port over the mobile OS ...more
While Sony as a company is well-known in the United States, it smartphones are not. For years, Sony has stuck with a boxy design with sharp edges and large bezels — however, they're finally getting with the trends. As a result, the Xperia XZ2 Premium offers a rare combo: A sup ...more
Welcome back, my hacker novitiates! Many of you have written me that you're having difficulty installing and running Metasploit on a variety of platforms. No matter if you're using Mac, Linux, or Windows, I strongly recommend you install BackTrack as your secondary OS, a virt ...more
Any internet user will need to download files eventually, and most simply have faith that what they are downloading is trustworthy. This doesn't give much clarity into the contents of the file, but if the file's author published the original checksum, comparing it to the SHA-2 ...more
Welcome back, my apprentice hackers! As many of you know, I have been hesitant to adopt the new Kali hacking system from Offensive Security. This hesitancy has been based upon a number of bugs in the original release back in March of 2013 and my belief that BackTrack was easi ...more
The pictures we upload online are something we tend to think of as self-expression, but these very images can carry code to steal our passwords and data. Profile pictures, avatars, and image galleries are used all over the internet. While all images carry digital picture data ...more
There's no doubt Kali has established itself as the most popular penetration distribution available. However, just because it's the fan favorite of beginners and security researchers doesn't make it right for everyone. Manjaro Linux is a beginner-friendly Arch-based distributi ...more
Kali Linux is the obvious first choice of an operating system for most new hackers, coming bundled with a curated collection of tools organized into easy-to-navigate menus and a live boot option that is very newbie-friendly. But Kali isn't the only distribution targeted at pen ...more