In this tutorial, you'll learn how to exploit weak security questions to take control of a given Yahoo! Mail account in much the same way Sarah Palin's Yahoo! account was recently "hacked." (To access Sarah Palin's account you will need, in addition to the tutorial, some manne ...more
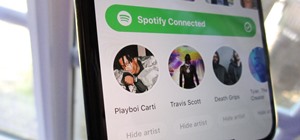
Some of us use our smartphones for almost everything. Manufacturers know this, so they try to make their devices as convenient as possible to use, but sometimes that convenience comes with a cost to security. The very same technology that allows you to easily share music with ...more
Welcome back, my greenhorn hackers! The Holy Grail of any hacker is to develop a zero-day exploit—an exploit that has never been seen by antivirus (AV) and other software developers, as well as intrusion detection system (IDS) developers. In that way, you can exploit systems ...more
Flash games are addicting, especially Bouncing Balls. But can you actually beat all of those high scores you see? Probably not, but you can if you use Cheat Engine. Watch this video tutorial to learn how to hack points in Bouncing Balls (10/11/09). Download Cheat Engine 5.5 i ...more
When it comes to earning high scores in a web game like Crazy Taxi or Crazy Cabbie, sure, you could, like, actually play it — but where's the fun in that? Cheat your way to the top with this hacker's how-to. Learn how to hack Crazy Cabbie on Facebook! This video tutorial show ...more
The interwebs is a great source of information, but sometimes said information is not always legit. That can be frustrating when it comes to making fun food, costumes, and arts and crafts for Halloween, like this bowl of "bloody" gummy worms. There are certain tricks you need ...more
If you are a photographer and are handy with a screwdriver and electrical tape, this is a really cool project to do. Basically, you "Frankenstein" a camera, taking a camera apart and rebuilding it with different lenses and the like, which makes for really cool photo effects.
When the much buzzed Facebook profile page redesign was released back in December, French artist and co-director of ad agency La Bande Originale Alexandre Oudin came up with an innovative way to maximize the visual possibilities of the page. His clever "hack" created a ripple ...more
In this eight minute video the host of the video conveys the methods and techniques that can be used for hacking the "Urban Rivals" video game. By use of Microsoft Word, the host types out the methods that are being used. This typing makes for a clear and easy to understand co ...more
Kipkay never fails to impress, and this so-called "condom hack pack" is no exception. Who knew there were so many useful uses for a condom besides the obvious! In this Kipkay two-part video, learn how to hack condoms for nine different uses. One condom hack is the "condom fir ...more
Turn a 'toy' radar gun into the real thing! Cops don't even have one like this! While this is a completely new and different design, the inspiration for this video is from an article by Ken Delahoussaye in MAKE Magazine. Just watch this video tutorial on how to hack a toy rada ...more
Welcome back, my greenhorn hackers! In my continuing effort to demonstrate to you how to hack the ubiquitous Windows 7, we will going after that notoriously vulnerable Adobe Flash that is on nearly every client Windows system (you are not likely to find it on servers). Flash ...more
Microsoft's built-in antimalware solution does its best to prevent common attacks. Unfortunately for Windows 10 users, evading detection requires almost no effort at all. An attacker armed with this knowledge will easily bypass security software using any number of tools. As ...more
We've always loved a good summertime hot dog, placed lovingly in a soft simple bun with ample ketchup and mustard. But after eating hot dogs this way and this way alone for the majority of our lives, we grew tired of the same old thing. Enter: The search for the 10 best hot d ...more
Thanks to Yifan Lu, it's been discovered that the operating system running on the Kindle Touch is written mostly in HTML5 and JavaScript, unlike the previous models which used Java. This is exciting, because when a device is hacked or rooted, that means homebrew programs can b ...more
So, how does someone keep their hacking life completely secret? What This Is: I'd like to know how hackers keep their hacking life secret. So with a bit of experience and knowledge obtained from elsewhere I want to share what I know, and also ask a few questions to become ev ...more
Get more money, deliver one hit kills, increase your experienc points... you can do all of these when playing Ninja Saga, all you need is the free game hacking program Cheat Engine. Here's how to use it to get what you want.
Welcome back, my hacker novitiates! Now, and more so in the future, wars will be fought hacker v. hacker. The number of soldiers, guns, tanks, and ships will be less important in your success in warfare than the number of well-trained hackers you have. Every nation and every ...more
Welcome back, my novice hackers! It has become clear from some of your questions that quite a few of you are unfamiliar with the hexadecimal system, or simply, hex. The hexadecimal system is used throughout computing and if you have never studied this Base16 numering system, ...more
What if you could have a secret hard drive connected to your computer that only you could activate? You can! Samimy shows you how to hack a remote controlled toy car and make a super secret hard disk drive in your computer, accessed via a secret activation key. This hidden eme ...more
What's your Twitter handle worth? If it's considered "desirable" (aka short and simple), it'll get you around 100 bucks, or, if you prefer, the affections of a teenage girl. A user with the handle @blanket found out the hard way that Twitter's security is atrocious when his a ...more
Tired of touch-tone hell? Get human with our cool phone hacks and cheats with the tips from this how-to video. Become a life hacker - we'll show you how to find phone numbers, cheat the computer and hack the call center system with our hacking tools. Watch this video tutorial ...more
Hi there, Crackers, Welcome to my 7th post (Part-1), this tutorial will explain about the basics of Batch Scripting. Why Batch? Batch is a really easy and interesting scripting language, it is used for malicious purposes, i.e. how can you exploit the victim's PC/life, furthe ...more
You must have read news about hackers dumping the data online, recent one was Ashely Madison. It's only the big companies' data, which gets noticed once it is out. There are many other small leaks which don't even get a mention. So this article is the first one of my series wh ...more
Today, learn the basics of lock bumping. Lock bumping is a lock picking technique for opening a pin tumbler lock using a specially-crafted bump key. One bump key will work for all locks of the same type. This video tutorial will show you how to hack into locks with lock bumpi ...more
Welcome back, my aspiring hackers! In recent tutorials, I have made reference to the name and location of the Linux devices in the file system, such as sda (first SATA or SCSI drive). Specifically, I have mentioned the way that Linux designates hard drives when making an imag ...more
If I could survive on one food for the rest of my life, it would be pizza. The irresistible smell of baking pizza instantly makes me feel both comforted... and hungry! While frozen pizza can satisfy your cravings, using fresh dough to make your own pizza is definitely much mo ...more
Welcome back, my aspiring hackers! As you have probably discovered by now, the file system in Linux is structured differently from Windows. There are no physical drives—just a logical file system tree with root at the top (yes, I know, roots should be at the bottom, but this ...more
Google Play has no shortage of Nintendo emulators: SuperGNES (Super Nintendo) Gameboy Color A.D. (Game Boy Color) My Boy! (Game Boy Advance) nds4droid (Nintendo DS) DroidEmu (SNES, NES, GBA, GBC, etc.) Those are just a few of what's available out there. The only problem with ...more
Welcome back, my tenderfoot hackers! As hackers, we often are required to get past antivirus (AV) software or other security measures. To do so effectively, we need to have some understanding of how AV software works. In this tutorial, we will take a cursory view of how AV so ...more
If you need to relieve an itch in your throat, you can try getting rid of it by scratching your ear. Or if you accidentally give yourself brain freeze while eating ice cream, you can press your tongue against the roof of your mouth and cover as much as surface area as possible ...more
To hack into Google images follow the following steps. You will first need to open a new internet browser window and go to Google, then load their images website. Next type into the search bar your image query and press search. Once you have gotten your search results paste th ...more
Welcome back, my greenhorn hackers! Throughout this series on Metasploit, and in most of my hacking tutorials here on Null Byte that use Metasploit (there are many; type "metasploit" into the search bar and you will find dozens), I have focused primarily on just two types of ...more
I don't like paying for repairs, and I don't like purchasing extended warranties. When one of my gadgets break, I perform emergency surgery and try and fix it myself. It doesn't always go well, but I've managed to resuscitate a few iPhones, an HDTV, an Android tablet, multiple ...more
In the previous article, we learned how to set up our VPS, configure our PHP server, and developed an in-depth understanding of how the payload works. With all that taken care of, we can get into disguising our payload to appear as an image and crafting the note in the greetin ...more
Welcome back, my hackers novitiates! As you read my various hacking tutorials, you're probably asking yourself, "What are the chances that this hack will be detected and that I'll land behind bars, disappointing my dear mother who already thinks I'm a loser?" In this tutoria ...more
Welcome back, my budding hackers! As I have mentioned many times throughout this series, knowing a bit of digital forensics might keep you out of a lot of trouble. In addition, digital forensics is a burgeoning and high paying career. Some knowledge and certifications in this ...more
The cold time of Christmas is upon us, and Icy Town is a winter-ific game you can play… and hack. With Cheat Engine and a little patience, you can hack and unlock floors in the game easily. This wintery video tutorial teaches you how to hack Icy Tower floors with Cheat Engine ...more
Containers are isolated software instances representing applications, servers, and even operating systems—complete with all of their dependencies, libraries configuration files, etc.—and they're taking over the corporate world. The ephemeral, portable nature of containers help ...more
If you move around a lot, you may notice that you can't play the same DVDs from country to country. The world is separated into different regions, and not all movies will play in all places. There are ways around this security measure, however, if you follow this tutorial. Th ...more
Never thought you could hack money in Bloons Tower Defense, did you? Well, you can. It's pretty easy and you just need Cheat Engine and some hacking skills. This video tutorial teaches how to hack Bloons Tower Defense 4 money (11/11/09). Just download Cheat Engine 5.5 and wat ...more
Though they share the same name, the HTC One and OnePlus One have completely different sound quality. HTC had put a lot of time and effort into fine-tuning their BoomSound technology, while OnePlus is still fairly new to the game, with brand recognition being a much greater ob ...more
Want to be the Donald Trump of Restaurant City? Watch this video tutorial to learn how to hack Restaurant City (02/21/10) with Cheat Engine 5.6. Hex: FFFFFFB8D02A0FF2 Restaurant City is a Facebook game that allows you to create and manage your own virtual restaurant. Descr ...more
In the digital age, camera's have gotten better, more advanced and more expensive. Even those throw-away cameras have taken the leap to digital-ness, which means more money. But you don't have to be confined by the one-time use of these single-use digital cameras anymore. Kipk ...more
Welcome back, my budding hackers! One of the most basic skills the forensic investigator must master is the acquisition of data in a forensically sound manner. If data is not captured in a forensically sound manner, it may not be admissible in court. In my Kali Forensics seri ...more
See a basic netbios hack, showing what happenes to ppl who leave files and folders shared over the Internet. Hack computers with open shares. Click through to watch this video on tricklife.com
Don't let Bejeweled Blitz get you down. It's not an easy game. Sometimes you just can't handle the degree of difficulty this notorious game imposes. But there are ways around this... Watch this video tutorial to learn how to hack Bejeweled Blitz on Facebook (11/16/09). For th ...more
!!! READ THIS FIRST !!! - 4 april 2009 - First of all: make sure that you're using FlashPlayer version 9 - A usefull tool to switch from version at any time is FlashSwitcher get it here: http://tinyurl.com/55up92 Howto: Buy an apple in the foodstore. Setup Cheat Engine: htt ...more
From Lifehacker's Tips Box, four short-cuts to life's small problems, urawaza-style: No Iron? If you're out an iron and you happen to have a hair straightener hanging around, it will do the trick (quite nicely). Also, works well as a dually useful traveling item, ladies. Warn ...more
Welcome back, my aspiring hackers! As I mentioned in earlier posts, the best hackers (or at least those not behind bars) have a keen understanding of digital forensics. If I am tasked to intrude upon an enemy's file server to retrieve war plans, such as in this tutorial, it i ...more
Restaurant City is a Facebook game that allows you to create your own restaurant. Watch this video tutorial to learn how to hack cash in Restaurant City (07/02/09). You need Cheat Engine 5.5 and RC Tools. Description of the app on Facebook: In Restaurant City you get to cre ...more
Welcome back, my aspiring hackers! Those of you who use Windows in a LAN environment understand that Windows machines can share directories, files, printers, etc. using "shares." This protocol dates back to the 1980s when the then dominant computer firm, IBM, developed a way ...more
My least favorite aspect of the winter season is how my fingers always turn into stiff, numb digits, unfeeling and seemingly incapable of making even the slightest movement. Yes, that might sound overdramatic, but if you hate wearing gloves like I do, you probably know exactly ...more
Open up your mobile phone and solder on a light sensing resistor to make an alarm go off when the phone is in the light. Possible uses?
See how to hack Pet Society from Playfish! Pet Society is the popular online game where you can design and take care of virtual pets. Check out this video tutorial to learn how to hack Pet Society for 2.14 billion paw points (11/13/09). Needed: Cheat Engine 5.5 HEX code: 544 ...more
Welcome back, my greenhorn hackers! Over the years, I have written many articles here on Null Byte chronicling the many the hacks of the NSA, including the recent hack of the Juniper Networks VPN. (By the way, my speculation in that article has proven to be correct. The NSA d ...more
Single sign-on (SSO) lets users login across different sites without having to manage multiple accounts. I'm sure most of us appreciate the convenience of seeing "Sign in with …" buttons that let us login with a single username. Hackers, however, see a possible avenue for expl ...more
Got a Canon Powershot whose resolution or functions are not cutting it for you? Then amp up its abilities - without flat out buying a new camera - by checking out this digital camera hack video. By modifying the camera's firmware you'll be able to add games as well as a manual ...more
Welcome back, my budding hackers! In previous tutorials, we've looked at some of the basic commands and concepts for using Linux. Along the way, I realized that I've failed to provide you with some basic background material on the stdin, stdout, and stderror. In human langua ...more
Is a cow up for adoption on FarmVille? Using this simple hack, change the cow's color in a snap! This video tutorial shows how to do the FarmVille pink-to-brown cow hack (10/14/09). Using this simple hack, one can change an adopted cow's color from pink to brown, and vice ver ...more