Individually addressable LEDs, also commonly called "NeoPixels" after the popular Adafruit product, are a bright and colorful way to get started with basic Python programming. With an inexpensive ESP8266 or ESP32 microcontroller, it's easy to get started programming your own h ...more
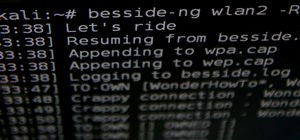
As most of you know, I am a strong advocate for using Linux for hacking. In fact, I would go so far as to say that you cannot be a hacker without knowing Linux well. I laid out various reasons for this in my "Why Every Hacker Should Know & Use Linux" article, and I even have a ...more
Hello guys, its been quite a while since my last post. (sorry for the lack of images) Well I guess I'm first up on the review board :P. So first thing to say: I ran USB persistence on Kali 1.10 by creating a persistence partition on my 16 GB drive. As for me, I had to delet ...more
Firstly let me start by giving credit to Lucid for their guide on Evilzone which inspired this idea, as well as the recent talk of anonymity on here. As the Archwiki states: Systemd is a system and service manager for Linux, compatible with SysV and LSB init scripts. systemd ...more
Backing up your files is a requirement in today's world of tech. In an instant, your storage device can fail. This is an unacceptable situation that should never happen to anyone. Storage is cheap, and backups are easier than ever to perform. Most of the time, this can be comp ...more
Anyone who has used Linux long enough is familiar with sudo. Short for superuser do (or substitute user do, depending on who you ask), it allows users to run commands as either root or another user on the system. From a hacker's point of view, sudo is often all that stands bet ...more
Friday's mission was to accomplish solving HackThisSite, basic mission 7, which required us to learn some basic Unix commands. If you have any prior experience using Unix commands, this should be a breeze for you if you sit and think for a second. These missions are for every ...more
Are you the expert hacker we're looking for? Do you have a great idea for an article on Null Byte? Do you have a passion to write, and more importantly... teach? We're officially looking for Null Byters on a weekly basis who are willing to take the time to educate the communi ...more
Our hacked Kinect series has demonstrated amply how the Kinect is changing the worlds of business, art, medicine and robotics. But where does it go from here? That will be determined by the thousands of dedicated DIYers out there doing work like you've seen here over the last ...more
In this instructional video, learn how to transfer files from your Windows PC to your iPhone or iPod Touch using DataCase. Datacase basically converts your iPhone or iPod Touch into a wireless drive that you can access your information on the Mac, PC, or Linux.
Real suffering is sitting through a thirty-second ad to watch a fifteen-second video, or watching your favorite music video in three-second fragments. Real suffering is this: “An error occurred, please try again later.” If you’re a modern human and multitask with multiple tabs ...more
WonderHowTo is made up niche communities called Worlds. If you've yet to join one (or create your own), get a taste below of what's going on in the community. Check in every Wednesday for a roundup of new activities and projects. This week: mathematical sculptures, burning Xb ...more
Sudo is a necessity on most Linux systems, most of which are probably being used as web servers. While the principle of least privilege is typically applied, sudo misconfigurations can easily lead to privilege escalation if not properly mediated. Which brings us to SUDO_KILLER ...more
Based on OTW's encouragement in his post on "How to Find the Exact Location of Any IP Address", I decided to make a gui(graphical user interface) which would hopefully make the process easier. However, because turning a python script into a standalone executable is a right pai ...more
Windows users have looked on with envy at Mac owners wrangling torrents with ease for years. Now, finally, a new Windows torrent client is making downloads easier, safer, and more customizable. Transmission, a go-to torrent client for Mac and Linux users since its creation in ...more
We're officially seeking Null Byters on a weekly basis who would enjoy taking their time to educate the community. Contributors will write tutorials, which will be featured on the Null Byte blog, as well as the front page of WonderHowTo (if up to par, of course). This is a job ...more
Picture this: the infrared sensor on your TV is not working and you are blaming it on your remote control batteries. Well, to make sure exactly what is going on, try testing TV remote to be sure. To the naked eye, you might not be able to see the infrared light, so you could t ...more
To the displeasure of many loyal Firefox users, Mozilla has been deploying what seems like a new marketing strategy to "catch up" to Google Chrome. I have no idea if this is because the version number is higher than theirs, but it is downright annoying. It's not all complaints ...more
Minecraft may seem like a game for just hardcore gamers and computer nerds, but it's totally not. It can hook anyone and everyone, from casual gamers to online addicts to total newbies—it can even turn its users into serial killers. And now, Notch and his Mojang crew have made ...more
Designer Brenden Macaluso's Recompute is an eco-conscious desktop PC constructed with sustainable cardboard. Everyone knows you're not supposed to get electronics wet, but seriously, you really better keep this one dry. Via I.D. Magazine: "This working desktop computer featu ...more
Hello null_byters, after some time out here we are again with another tutorial, continuing our beautiful series, today we will write our first real world bash script. BEFORE WE START Before we start today's lesson Let's recap what we learned in the previous lesson, right now ...more
Hi everyone. Recently I've been studying some topics about Assembly, memory and exploitation, and thought I could write something nice, easy and fast about it, just because I like to share what I learn, and probably sharing what you learn and trying to explain it to a strange ...more
Many users of the virtualization software VirtualBox may have noticed that the USB system has been pretty buggy for quite a long time. I've had my USB randomly duck out on me way too many times to count. This can really be difficult to deal with when you require access to the ...more
Previously, you'd need to install the Google Cast extension to cast webpages from your Chrome web browser to your Chromecast-connected TV, but as of March 24th, you don't need it anymore. Casting now works natively in Google Chrome (which had been available in the Beta version ...more
Pygame! And what you can accomplish with it. Another python article... (Blame Alex for getting me hooked on yet another coding language...) This little article will cover "Pygame", the set of modules that were designed with game developers in mind. Specifically ones who code ...more
With the release of the HoloLens, Microsoft has put itself in both a great position while giving the competition a serious target to aim for. This is normally the case for anyone that is first to the market with a new idea, and now we've finally got a good competitor HoloLens ...more
TWRP won't be ready for the Pixel 4 and 4 XL until months after release. But since you can already root with Magisk and tinker with the OS, you might find yourself in a situation where your phone won't boot, yet you don't have a custom recovery installed to fix it. Luckily, th ...more
Despite being one of the largest and most feature driven companies on the planet, Google can sometimes come up short. I have my Chromecast running 24/7, and while I use my phone to cast most of my content, I sometimes find a video while browsing Reddit or LiveLeak on my laptop ...more
Bucky from The New Boston serves up this Python video tutorial on how to program infinite loops and breaks in Python. This is the program you use to write all of your Python code down. Learn how to make an infinite loop and also how to use the break statement! Python is a dyn ...more
New to Ubuntu Linux? This computer operating system could be a bit tricky for beginners, but fret not, help is here. Check out this video tutorial on how to install Zekr (Qur'an Study Tool) on Ubuntu Linux, Windows, and Mac OS. Zekr is an open platform Quran study tool for si ...more
Welcome to the sixth Community Byte for coding in Python and beating the challenges presented to us by HackThisSite. These sessions are created to bring our community together, to learn from each other, and essentially grow together. Everyone is welcome, from novice programmer ...more
Android-enabled mobile devices are taking the world by storm, giving Apple's iPhone a run for their money. And if you're holding an Android cell phone in your hand, getting accustomed to all the flashy features can be daunting, especially if you're new to multimedia smartphone ...more
For many, the stock version of Android is often considered the epitome of what the operating system should look and feel like by default. It's clean and clear of unwanted extra apps that come pre-installed with the system, provides a fluid and fast user experience, and runs on ...more
This how-to is for everybody who faced the problem of intercepting personal data sending through the Internet and is looking for fast and secure method to protect his activity in the global network. For these purposes I recommend VPN connection (creation of special tunnel thr ...more
FaceTime audio calling is a great alternative to regular phone calls on your iPhone because it usually has better audio quality and fewer dropped calls than regular calls over cellular or Wi-Fi calling. Plus, it's easier to start group chats, and you have the choice to turn on ...more
Welcome back, my rookie hackers! The Golden Fleece of hackers is to develop a zero-day exploit, an exploit that has not been seen by antivirus (AV) software or and intrusion detection system (IDS). A zero-day exploit is capable of skating right past these defenses as they do ...more
Yesterday, the Free Software Foundation published an article written by Paul Kocialkowski. A software developer for the the Android fork system Replicant, Paul stated that his organization discovered, and later patched, a "backdoor" vulnerability that existed in older Samsung ...more
Welcome back, everyone! In this lesson, I'm going to go over the use of the echo function and variables, as well as basic syntax. You will need: A text editor - I personally recommend the free (and amazing) Notepad ++, but you can use any text editor you want, even Windows' ...more
Android phones finally have a true AirDrop alternative called "Nearby Share." The new feature was added through an update to the Google Play Services app that comes pre-installed on all Android devices in the US, so you don't even have to wait on a firmware upgrade — it's just ...more
It's important to know who you're dealing with after hacking your target's MacBook. Getting remote access is simple, but covertly gathering information about the user and their system can be a challenge. Continuing with our situational awareness attacks, we'll be further orie ...more
One of Android's biggest strengths is its ability to interact with other operating systems. When you plug your phone into your Windows PC, you instantly see all of the files it holds—and all it takes is a simple syncing app to do the same with Mac. To top that off, apps like P ...more
This video will give you an overview of a successful endgame fortress from Dwarf Fortress, giving you tips on achieving a similarly successful fortress throughout. Slaves of Arnok II: Dwarf Fortress, or Dwarf Fortress as it is more commonly known, is one of the most intimidat ...more
Oftentimes, seemingly insignificant, nondescript features have the most impact on enhancing our Android's usability. A great example is Nougat's inclusion of customizable Quick Settings tiles, which adds greatly to the user experience by letting individuals tailor their expand ...more
Hello ladies and gentlemen, I'm back with another informative(hopefully) article for you all. Once again I would like to apologize for my absence for about a week or so. I have some stuff going on with my life and university and I haven't found enough time to make a fully in-d ...more
Welcome my aspiring hackers and programmers! Today i will introduce you to a programming language that as a hacker you should have in your set of hacking/programming skills (except if you're only interested in web hacking/programming...then you should go learn some html or PH ...more
While the majority of reviews for the Google Nexus 4 have been positive, there are a few things that have irked customers. Two of the most common complaints are the lack of 4G LTE on the phone (which you can activate yourself) and the touchscreen's less than stellar responsive ...more
David Wang of the iPhone Dev Team has achieved what is considered quite a jaw-dropping hacking feat. Yesterday Wang posted a video of Google's Android operating system up and running on an iPhone. Via CNET: "The Android-on-iPhone hack is a notable technical accomplishment, bu ...more
We're officially seeking Null Byters interested in teaching others! Contributors will write tutorials, which will be featured on the Null Byte blog, as well as the front page of WonderHowTo (if up to par, of course). This is a job meant for anyone with the will to share knowle ...more
If you want to control electronic devices, such as a relay or motor, you can do so using MicroPython with an ESP8266 and web browser. Usually, you'd program an ESP8266 using Arduino, but C++, which Arduino uses, is not always the easiest programming language for beginners to l ...more
New to Ubuntu Linux? This computer operating system could be a bit tricky for beginners, but fret not, help is here. Check out this video tutorial on how to share files between Ubuntu (Host) & XP (Guest). VirtualBox is a family of powerful x86 virtualization products for ente ...more
In the last decade, the number of people working remotely in the US has increased dramatically, and so has their need for technology and software to supplement that remote work. Whether you work from home or a coworking office space, the requirement for highly compatible and h ...more
Oh, Mario. The guy that's been a part of our lives since as long as we can all remember. Well, Adam Ringwood and his friends did something pretty cool with one of Mario's most exciting games at the HackIllinois event in February 2016—they hacked a Chevrolet Volt's steering whe ...more
This is the first installment in a new series that I am calling "Hacker Hurdles." These are things, methods, techniques that make our job as hackers more challenging and difficult. Don't misunderstand me, these items don't make our task impossible, but rather more challenging ...more
Bootloops are a risk inherent to rooted devices — with great power comes great destroyability, after all. While custom recovery sometimes provides a quick fix when you flash the wrong Magisk module, with TWRP becoming more challenging to implement thanks to Android 10, the sol ...more
A new repository appeared in Microsoft's GitHub account a few months ago for a project called HoloJS. For those JavaScript developers out there that have been wanting to make HoloLens apps, this one's for you. Microsoft has been surprising the development world recently by fu ...more
Here's a quick and easy video tutorial on how to root any Qualcomm-based U.S. or Canadian Galaxy S4 Android smartphone. Windows, Mac, and Linux Tutorial included. Video: . Video: . Video: . Step 1. Go to Settings->More->About device then hit “Build Number” about 5-10 times u ...more
It's easy to have your password stolen. Important people like executives, government workers, journalists, and activists face sophisticated phishing attacks to compromise their online accounts, often targeting Google account credentials. To reduce this risk, Google created the ...more
Learn a quick fix that'll patch up your slow Internet connection on Ubuntu Linux 7.10
Correctly identifying the underlying technologies that run on a website gives pentesters a considerable advantage when preparing an attack. Whether you're testing out the defenses of a large corporation or playing the latest CTF, figuring out what technologies a site uses is a ...more
It's always a good idea to know how an attack works at the very basic level. Manual techniques for exploitation often find holes that even the most sophisticated tool cannot. Sometimes, though, using one of these tools can make things so much easier, especially if one has a so ...more