This video conning tutorial from someone who has seen too many episodes of MacGyver shows how to break into a Masterlock with the help of a handy Swiss Army knife. Watch this video demonstration and learn how to pick a padlock with a Swiss Army knife. You may not be MacGyver, ...more
This is a video demonstrating how to open a can with a Swiss Army Knife can opener. To begin, place the can on a flat surface. Open the can opener on the Swiss Army Knife. Make sure that the hook of the can opener is on the outer ring of the can and that the cutting part is on ...more
Ever wanted to be just like MacGayver. Well, you can't. And he's not real. But take some consolation in this how-to video. It is really easy to use a Swiss Army knife to open some padlocks. Just insert the thinnest tool into the lock, turn a bit and jiggle up and down. Watch t ...more
Learning how to maintain and sharpen your Swiss army knife is an important skill for campers and backpackers. You will need to have a sharpening stone that can be dry or wet. To use a wet stone simply add a little bit of water or homing oil. Keep the blade at an angle of 5 to ...more
This parlor trick video aptly demonstrates how to open a bottle of wine with an ordinary swiss army knife when that feisty cork screw goes missing. This video is a great alternative for college students who seem to inevitably misplace or loan their cork screws and want to seam ...more
The Swiss army knife has a lifetime warranty and is the brand that MacGuyver used in his series so you know that it's good. The keychain side of the knife contains a bottle opener while the other side contains a can opener with a sharp cutting edge. The bottle opener has a fla ...more
This video shows you how to use a Swiss Army knife can opener. It is easy to confuse the can opener with the bottle opener. The can opener has a small screwdriver tip and a sharper edge. Cans of spaghetti are good for a quick meal on the train. Put the bottom part of the can o ...more
This video shows you how to use a can opener, like the ones found on Swiss Army knives. There's also a strange fruit in this video, something called lychees. So, if you're ever in need of opening a can of lychees in the woods, this is the video to watch.
There are over 60-something Android apps cluttering my app drawer. While I'm constantly on the look out for new mods and apps to install, the default way of managing them is cumbersome and just feels unintuitive. I mean, who on Earth would wants to individually manage each app ...more
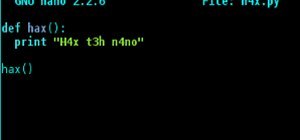
For over 20 years, a tiny but mighty tool has been used by hackers for a wide range of activities. Although well known in hacking circles, Netcat is virtually unknown outside. It's so simple, powerful, and useful that many people within the IT community refer to it as the "Swi ...more
If you're going exercising, either at the gym or outside, you're going to need a backpack, gym bag, or pockets to hold your water bottle, wallet, keys, smartphone, and anything else you've got on you. Health Emporium US LLC looks to ease some of the trouble with carrying all ...more
This video teaches you how to pick a lock using only a tweezer from a swiss army knife and a safety pin. Only use this information for proving that you're cooler than your other friends.
The swiss army triplet is a unique one-way rudiment that can be played in both right and left hand leads. Unlike most of the other rudiments, this rudiment isn't designed to alternate. As its name suggests this rudiment has a 'triplet' feel.
Keys always seem to multiply. You start out with your house keys and car keys, and the next thing you know, your keychain is full and you have no idea what half of them even unlock. If you want to make your keys lighter and less bulky, redditor mattfrancis13 has a solution. H ...more
Watch to learn how to say the names of some weapons, like a machete and a grenade, in French. une balle - bullet une grenade - grenade un fusil - rifle un pistolet - pistol un révolvaire - revolver une machette - machete un canif - penknife un canon - cannon un couteau - knif ...more
Carving a net needle from wood is probably easier than you think as long as you have your trusty Swiss army knife at hand. It has a wide array of available tools in a small unit. First you will need a piece of balsa wood. It should be 1/8 of an inch thick by 3 inches wide and ...more
This tutorial covers the basics of creating homemade CGI with PFTrack, a Swiss Army knife of visual effects software. Using PFTrack, PictureBandit takes you through the different features of PFTrack, and shows you how to use it to match move your scene. Make your video project ...more
Boomerangs are traditional Australian throwing sticks. They can be used as weapons or as sport. This video shows you how to throw one properly. These are not the returning boomerangs. These are longer and used as multi purpose tools equivlant to a Swiss army knife. They used e ...more
This video tutorial is in the Home & Garden category which will show you how to use a multimeter to check for continuity, measure resistance and voltage and many more values. Multimeters are like the electrical engineer's Swiss army knife. Multimeters can be of digital or anal ...more
First, get out a Swiss Army Knife and clean your hands. Then, take out the main blade. Next, on the right hand side of the IPod, stick the blade through between the gap to open the casing of the IPod. Then, turn the ipod upside down, so that the display side is facing the grou ...more
Styling gel is the Swiss army knife of hair styling—an all-purpose tool that can help you achieve any goal or look. You may even want to take some on your next camping trip. You will need: the gel hairstyling product of your choice a blow-dryer Tip: Avoid using gels that con ...more
One can of tuna fish is as versatile as a Swiss army knife. Just stock up on this stuff when traveling or camping. Watch this tutorial. You can easily pull two hours of light from one can. Look deeper into WonderHowTo. You can poach an egg in a can. You can make a spin top ...more
MacGyver. How can he not be a WonderHowTo hero? The ultra resourceful secret agent, always handy with his Swiss army knife, is inspiration to all tinkerers, hackers, and DIYers across the world. But who's the real man behind MacGyver? Lifehacker recently interviewed the man ...more
Mac users know why they love Apple. Of course, there are limitations. An entire universe of shortcuts is unavailable to the average user. That's where MacPilot comes in. Combining the awesome power of UNIX with Mac's simplicity, MacPilot allows you to unlock over 1,200 featur ...more
We know our Null Byte readers would like to see some iPhone-hacking scenarios on the site soon, but until we get some of those up, we understand that some of you actually use an iPhone as your primary phone. If that's you, and you would like an easier way to get information fr ...more
There are many tools out there for Wi-Fi hacking, but few are as integrated and well-rounded as Bettercap. Thanks to an impressively simple interface that works even over SSH, it's easy to access many of the most powerful Wi-Fi attacks available from anywhere. To capture hands ...more
Your Galaxy S5 is jammed to the brim with all sorts of electronic sensors. These are capable of reading humidity levels, ambient temperature, air pressure, and much more. Yet, while this data is constantly being collected by your phone, there aren't any built-in apps that are ...more
With all of the advancements in the smartphone world, we can virtually use them for anything. You can use your smartphone as a mobile hotspot, an Xbox controller, a car locator, and a security camera. Heck, you can even turn it into a Swiss Army knife. And now you can even use ...more
We all have apps that we use most frequently, or system preferences that we're regularly adjusting. Whether it's Netflix or a new game that you're hooked on, there are times when you want quick and easy access versus searching for them, even if they're on your home screen. In ...more
If MacGyver had a Nexus 7, he'd most definitely have TWRP installed. It's the softModder's Swiss Army knife for all things modding. You can flash custom ROMs, install add-ons, recover from a disaster, and much more. But even with a wide array of modding features, TWRP, which ...more
The iPhone X ushered in the Swiss Army Knife-like Side button, which can perform numerous functions, such as summoning Siri and opening Apple Pay through click gestures. This has carried over into the iPhone XS, XS Max, and iPhone XR, so if you've upgraded to one of these devi ...more
Google and Samsung are the biggest players in the Android world. Despite a rocky launch, Google's Pixel 2 XL became one of the premier Android devices of 2017, headlined by fast performance and a pure version of Android. Still, many users prefer Samsung's offerings, and their ...more
The latest Google Play Services update has somehow broken major functionality in both Titanium Backup and Substratum. Titanium Backup has suddenly become stuck at zero percent while restoring, and Substratum simply fails to apply themes anymore. Both of these apps do require r ...more
Hello, ladies and gents! Today I will be discussing the fun and excitement of backdoor on an OSX system. Note: A lot of what I am going to say is directly based off of this article by Patrick Mosca. Please give him your gratitude and leave mine at the door! Step 1: Reverse S ...more
Team Win Recovery Project (TWRP) is a custom recovery for Android devices and the one used by most softModders, mainly because it has touch-based actions, as compared to the more time-consuming button-based approach that ClockworkMod (CWM) uses. With TWRP, you can flash new R ...more
Sending and receiving files between Android devices has no shortage of options—Bluetooth, email, MMS, and Wi-Fi are just a few of the more popular ones that we use. While the choices for this functionality are plenty, problems can arise with connectivity issues and file size ...more
I have literally played Madden, watched YouTube videos, and listened to music on my phone all at the same time. Some would call this pathetic, but I call it talent. Life is way too short, so I need to get the most out of it when I can. Thank goodness for multitasking, which sh ...more
Browser customization is one of Firefox's best attributes. You can personalize your Firefox with extensions, add-ons, themes, and so on. And if all of that still doesn't cut it, you can even customize the Firefox Menu button to say whatever you want. To start off, you'll need ...more
Pull up outside any construction site and you'll see tools scattered about—hammers, jigsaws, nail guns, hydraulic pipe benders—these are the tools of the trade. You would be hard-pressed to build a home or office building with just your hands! On that same page, security profe ...more
Who doesn't love cartoons? Whether you want to take up a creative hobby over the holidays, learn animation for an exciting new side hustle in 2021, or buy the dream gift for the person in your life who loves all things animated, this deal is one to take advantage of today. Rig ...more
With the rise of website encryption (TLS), sniffing passwords from network activity has become difficult. However, it's still possible to quietly exfiltrate a target's network traffic in real time to extract passwords and sensitive information. Pertaining to macOS, there are t ...more
Backdooring a powered-off MacBook is easy when a few minutes of physical access is allowed. That attack works well if the hacker also shares a Wi-Fi network with the victim, but this time, I'll show how to remotely establish a connection to the backdoored MacBook as it moves b ...more
The LG V30 has finally been announced and was rumored to be released sometime in September, but September has come and is almost gone, while LG fans have been waiting anxiously. The V series offers a more robust media experience when compared to LG's other flagship, the LG G6. ...more
One of the ultimate goals in hacking is the ability to obtain shells in order to run system commands and own a target or network. SQL injection is typically only associated with databases and their data, but it can actually be used as a vector to gain a command shell. As a les ...more
Command injection is a technique used by hackers to execute system commands on a server, usually via a web application or some kind of GUI. This can happen when an application provides some sort of functionality to the user involving the use of system commands. When the input ...more
The misconception that macOS is more secure than the Windows operating system is far from the truth. With just one small command, a hacker can completely take over a MacBook and control it remotely. The sheer volume of Windows computers currently in operation around the world ...more
Local port forwarding is good when you want to use SSH to pivot into a non-routable network. But if you want to access services on a network when you can't configure port-forwarding on a router and don't have VPN access to the network, remote port forwarding is the way to go. ...more
Apple gave the Messages app a massive makeover with iOS 10, with a slew of options that made iMessages on the iPhone a lot more fun. While not quite as comprehensive, iOS 11 builds upon that success and makes the app more user-friendly and all-inclusive. iOS 11 brings plenty ...more
Lenovo brought out the big guns for CES 2014, with the Vibe Z showcased as the Chinese company's' first foray into the LTE smartphone space. Slated for a February release, the ultra-thin and extremely light smartphone will certainly be in the running for top smartphones of thi ...more
WhatsApp is the go-to messaging app for millions worldwide and its easy to see why. The app can be considered the Swiss Army Knife of texting thanks to numerous features like Group Chats and Status Stories, in addition to striking a great balance between ease of access and ove ...more
File inclusion can allow an attacker to view files on a remote host they shouldn't be able to see, and it can even allow the attacker to run code on a target. To demonstrate these vulnerabilities, we'll be practicing PHP file inclusion using the Damn Vulnerable Web App. We'll ...more
In my previous article, we learned how to generate a vulnerable virtual machine using SecGen to safely and legally practice hacking. In this tutorial, we will put it all together, and learn how to actually hack our practice VM. This will provide some insight into the methodolo ...more
Microsoft recently released "Seeing AI," an app aimed to help the blind understand their surroundings. As Microsoft puts it, "the app narrates the world around you by turning the visual world into an audible experience." We asked Matthew Chao, the brother of one of our founde ...more
Smartphone games are getting pretty good these days, but they still can't beat the retro appeal of a good emulator. I mean, who wouldn't want to have their all-time favorite console and arcade games tucked neatly in their front pocket? Classics ranging from Super Mario Bros. t ...more
Computers all over the world rely on a program called "libssh" to use the SSH communications protocol, which allows trusted users to log in and administer computers remotely. Due to a flaw in libssh, fooling a computer into granting SSH access is as easy as telling it you alre ...more
While there aren't as many ways to customize your iPhone like there is on Android, there are still a lot of apps out there that can help streamline and enhance your experience beyond Apple's own default options — and we've hand-picked over 100 essentials. No matter if you've ...more
While hackers adore the command line, working with the GUI (graphical user interface) of an operating system has some advantages. This is especially true when it comes to post-exploitation. When we can control the mouse and keyboard of a remote computer, we can truly say we ha ...more
Brand loyalty is one of the main factors behind our decision to choose a particular mobile device, but it doesn't have to be the entire equation. Educated consumers know that certain devices simply fit their budget and usage better than others, which means you can't always let ...more
Apple's spring event, where the company will announce a new iPad model, is just around the corner. We also expect to see the long-awaited Apple Pencil (3rd generation), also known more simply as Apple Pencil 3, with several significant enhancements that promise to make it an i ...more
Rooting. As an Android user, I'm sure you've heard the word once or twice. According to Kaspersky, 7.6% of all Android users root — but for the 92.4% who don't, we wanted to talk to you. Rooting allows you to remove barriers and open Android to a level of unprecedented contro ...more