This is a Computers & Programming video tutorial where you will learn how to enable or disable the UAC option on your computer. UAC stands for User Account Control and this tutorial is for Windows Vista. With UAC enabled you are more secure. First, click ‘Start’, type in ‘msco ...more
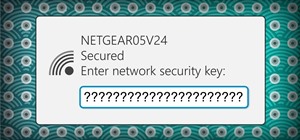
This video shows you the method to find if someone else is using your Internet connection. There are two methods for this. The first method involves opening the start menu and click on 'Run'. Type cmd in the text box which opens as a result of clicking on 'Run'. Type NET VIEW ...more
In this Computers & Programming video tutorial you will learn how to get widescreen videos on YouTube from normal videos. This can be done in Sony Vegas Movie Studio. Go to project > properties > video. Here you set the template width to 640, height 360, frame rate 30, field o ...more
The Replace Color tool lets you select one color and paint over it with a different color. To use the Replace Color tool, choose whether you want to select replacement colors from the swatches or from the image itself using the From drop-down. This is not always the best metho ...more
There are many ways to open a bottle, but you have to admire the simplicity and karate-esque action required in Instructable member Carleyy's scrap wood method. Don't be deterred by the use of power tools in the video below. All you really need is a piece of scrap wood, one nu ...more
In this episode of the Southwest Yard & Garden series, John White discusses common plant problems with the help of Dr. Natalie Goldberg an extension plant pathologist. The common shrub problem discussed is Powdered mildew, which is shown on a japonica shrub. The common tree pr ...more
Since the day of the Xbox 360 release, storage space for the device has been overpriced beyond belief. OEM 250GB HDD models still cost $110 USD! A 250GB hard drive should not destroy my wallet, Microsoft. Storage space, especially on HDDs, is cheap. You can buy a removable 2TB ...more
Skating backwards can be challenging but an instructor from Expert Village shows us two easy ways to learn. Several important things to keep in mind before you begin is to not be afraid of falling, make sure your body is relaxed, and your knees should not be locked. Now, from ...more
In this step by step video, you will learn how to pick a lock with a home made tension wrench and a modified safety pin or bobby pin. This lock picking technique is actually pretty simple but may take a bit of practice before you can pick a lock in 30 seconds or less; so if yo ...more
In this video tutorial we learn how to assign a macro to a button or a check box in Excel. The first thing you want to do is to place the macros you want to use in the spreadsheet. You can assign a macro to any object within Excel. Next draw the shape in the spreadsheet that y ...more
Locked out of your car and need to break in ASAP? Unlace a shoelace from one of your shoes and you've got yourself the only tool you need to open your car door from the outside. Don't Miss: 6 Easy DIY Ways to Open Your Car Door Without a Key Simply make a slipknot in the mid ...more
This video teaches you how to use Photoshop to remove people from a picture but you can essentially use this method to remove anything you want from a picture. First, click on the lasso tool and highlight a figure you want to remove. Drag the highlight adjacent to the figure a ...more
This video tutorial by VvCompHelpvV gives you two methods to achieve the Sin City effect in your photos using Photoshop. The Sin City effect is making the main subject of the photo appear colored while the rest of the photo looks black and white. In the first method the subjec ...more
Don't let a missing corkscrew deter you from uncorking your bottle of wine at your next party, picnic or romantic dinner at home. Following up on a previous post on how to open a bottle of wine using just a towel and a flat, vertical surface (a wall or a wide tree trunk), list ...more
This video shows the method to create a photo montage in Sony Vegas. Go to 'Options' menu & Preferences. Go to the 'Editing' tab & 'New still image length (seconds)' and put the corresponding value and hit 'OK'. Open the pictures from explorer and you have a montage in which p ...more
Hello everyone and welcome to Part II - The Ultimate Guide: Diagnosing & Fixing Connection Issues. In this tutorial we will discuss more advanced methods that I took in order to fix our home network. I have also attached a link to download the FREE eBook - so feel free to down ...more
Crakintosh.tk shows viewers how to easily SSH into their iPhone of iPod Touch with an easy method! First, you will need Cydia. Open up the program then go to Manage and click Packages. You will need to click Authorize SSH and Install this. Wait for this to download. Next, go t ...more
In this video it is demonstrated that how to delete temporary files in Windows XP. There are two different methods for deleting temporary files. First of all go to and click "start" then go to "run" and type temp now click on ok, then a window will appear, in this window there ...more
INTRODUCTION In this world of Internet era, almost everyone wants to create theirs own web presence by either hosting their own blog, articles, photos, videos, reviews, etc etc . But some people choose their own way and decide to have something bigger! What is it? Its a websi ...more
This video shows you how to remove a tattoo from a photograph using Photoshop. First, select the tattoo using the pen tool, to get a very accurate line around the tattoo. Make sure the "Paths" button is punched in. Drag the mouse and click several times to make a path around t ...more
This video shows us the method to make simple GIF animations in Photoshop Elements 6. First we have to make a file with different layers. Click on the icon below the 'Layer' option to make a new layer in the file. After finishing the file, go to 'File' and the 'Save for Web' o ...more
This video shows the method to turn off pop-up blocker in Internet Explorer and Firefox. Firstly, open Internet Explorer and go to 'Tools' option. Go to 'Internet Options' and click on the 'Privacy' tab. You will see an option of 'Block pop-ups' at the bottom of the window. Yo ...more
This video shows the method to make multiple backups while restoring a iPhone. See ' iPhone and iPod touch : About Backups' on your iPhone. Scroll to the bottom and see the location of the backup. You can rename the backup folder so that the device thinks there is no backup an ...more
This video shows us the method to use Blackberry email more effectively. Firstly, let us go to the place for typing your emails. Click on the leftmost icon at the bottom of the home screen. Now press the button on the left side of the track ball and choose 'Compose Email'. Now ...more
This video demonstrates the steps to restore your iPhone or iPod Touch to original factory settings. This is a way to undo or repair any damage to your phone caused by downloading unauthorized files or corrupt files. Be aware that this will delete all the files that are on you ...more
Need some advice on fly fishing? Fly fishing is a distinct and ancient angling method of fishing, most notably as a method of catching trout or salmon. Fly fishing is also well employed today for a large variety of species other than trout and salmon, including pike, bass, pan ...more
There are two ways in which you can crochet in the round. One is by making a loop with a chain of 2 or 4 stitches, the other is with an adjustable ring. Start with the chain method, and once you are comfortable single crocheting in the round, try to move on to the adjustable r ...more
Do you want your horse to be the best turned out at the next show? Then follow this simple guide, showing both methods of plaiting to make your horse look like the star he or she is! All you need is a body brush, water brush, bucket of water, mane comb, needle, and plaiting th ...more
An insertion pin allows you to stretch the size of your piercing one size at a time. The tapered shape allow you to increase the size of your piercing in a gentler manner. This how to video teaches the method on inserting the pin easily and comfortably. Watch this tutorial and ...more
To Android users, especially advanced ones, rooting their phones or tablets is becoming a necessity. Rooting Android could be complicated, if you do it all by yourself, even with a step-by-step tutorial. However, what Kingo Android Root offers you is a true one-click experienc ...more
It'd be a financial burden to have to buy new shoes every time a current pair gets scuffed up, but thankfully there are some easy DIY tricks for saving us that trip to the shoe store. Scuff marks can easily be remove from shoes and sneakers using common household items found i ...more
While blackheads are a little different from your run-of-the-mill acne and zits, they are still annoying when they appear on your face and, thankfully, can be banished with a number of DIY home remedies incorporating common household products. Blackheads are created when oil ...more
Functioning as an extension of your iPhone, the Apple Watch makes monitoring and receiving notifications convenient with just a glance, leaving your iPhone in your purse or pocket. But just like on your iPhone, these notifications can begin to stack up, so let's show you the o ...more
When it comes to modding an Android device, a custom kernel can take you farther than almost anything else. Most offer the ability to overclock your processor for performance gains, change your CPU governor, or even under-volt to increase battery life, among other features. O ...more
Every step in the evolution of computing brings an in-kind leap forward in user input technology. The personal computer had the mouse, touchscreens made smartphones mainstream consumer devices, and AR headsets like the HoloLens and the Magic Leap One have leveraged gesture rec ...more
It seems nowadays the word "easy" has taken on an alternate meaning. When I see "easy," I expect a quick and painless process, but when it comes to flashing or installing a custom ROM, easy means anything but. That's the main reason I've avoided installing CyanogenMod on my S ...more
Apparently it is possible to reduce 64,000 possible Master Lock padlock combinations down to just 100. The entire process is clearly illustrated in the below how-to from Mark Edward Campos. For an enlarged version, click here. Looking for something a little more interactive? W ...more
Welcome back, my novice hackers! More and more, the world is turning to and adopting the smartphone platform as the digital device of choice. People are not only using smartphones for voice communication, but also web services, email, SMS, chatting, social networking, photogr ...more
Now that the transfer tool for migrating your Google Play Music library to YouTube Music is rolling out, more fans of the former, which will meet its end in 2020, are giving its replacement a try. New converts will find three newer features front and center. Your Mix, Discove ...more
Whether you have the original Nexus 7, or the 2013 Nexus 7 tablet, rooting it will give you access to tomorrow's features, today. Sure, without root there's lots you can use it for. It's helped me get out of bed, became my own personal bartender, and a lot more. But with a r ...more
Beta software can be exciting because you get to experience cool new features before most other people. But it can have unwanted consequences such as bugs, UI glitches, and horrible battery life that'll make you wish you never installed it. If that sounds like you with iOS 16 ...more
Heads up! We've done a new, more thorough review of the best Android file-sharing apps. You can check that out here. Our old file-sharing app roundup can still be viewed below for posterity. Update: The 4 Best File-Sharing Apps for Android (2018) We've come to a point where ...more
It's easier than you might think to hack into Wi-Fi routers using just one unrooted Android phone. This method doesn't require brute-forcing the password, a Windows OS for converting PowerShell scripts into EXE format, a reliable VPS for intercepting hacked Wi-Fi passwords, or ...more
With a cheap computer, smaller than the Raspberry Pi, an attacker can create a remote hacking device. The device can be attached to a target router without anyone's knowledge and enable the hacker to perform a variety of network-based attacks from anywhere in the world. As th ...more
Need root on your Samsung Galaxy S3? Phone not getting the Jelly Bean update? Stuck on the Samsung screen? Phone bricked? Need to restore back to stock? Odin can help! What is Odin? Odin is a Windows-only program, designed by Samsung themselves, used to root, flash, upgrade, ...more
Changing the carrier name from an unlocked iPhone's status bar has been possible to do ever since Cydia released Zeppelin earlier this year. The application comes with preset logos you can use such as Pac-Man, Space Invaders, the Assassin insignia of the Assassin Order from As ...more
If you have a ton of photos and videos on your iPhone, backing up to iCloud is probably a no-go since it only provides 5 GB of free storage. Yes, you can buy more storage, but who wants to do that? And what happens if you run out of storage, stop backing up, and your phone get ...more
Welcome back, my tenderfoot hackers! One of the issues we often encounter with Metasploit is how to add new modules. Although Rapid7 (Metasploit's owner and developer) periodically updates Metasploit with new exploits, payloads, and other modules, at times, new modules appear ...more
With all the kitchen sink debris that goes down the drain, it should be no surprise that your garbage disposal sometimes gets a little smelly and needs some extra cleaning. Using common household items from your kitchen or medicine cabinet, you can easily clean your garbage di ...more
When it's most important for me to browse the web incognito, I always seem to forget to enable private browsing. If that sounds like you, it's time you stop making that mistake for good. Manually deleting the cache and browser history is a thing of the past, and as it turns ou ...more
Seemingly lost in the fanfare of the numerous features and specs of the Nexus 5 were a few highly innovative and handy add-ons—a low-power step detector and step-counting sensor—useful for tracking fitness data. Both of these sensors are supported by Android 4.4 KitKat, but t ...more
Last night, I was reading a riveting National Geographic article on the green-eyed tree frog, until I was quickly interrupted by an annoying popup asking me to "create a free account" or "sign in." Really, I'd like to do neither. I just want to read about tree frogs. This popu ...more
Deep down inside, Kindle Fires are actually Android tablets — the only trouble is, Amazon has layered so much of a skin on top of it all that you can't normally use Android's main app store, the Google Play Store. The Amazon Appstore, which comes bundled with Kindle Fire devic ...more
When it comes time to sell your smartphone or trade it in for your annual upgrade, you'll have to make sure that all of the sensitive data the device accumulated while you owned it is properly erased so that no one else can access it. This process is referred to as a "Factory ...more
Rice water refers to the cloudy water that is leftover after washing rice in a bowl, or the excess water drained from a pot used for cooking rice in boiling water. Whichever method you prefer, rice water can be saved in a separate container once cooled, then used for a number ...more
This how-to is for everybody who faced the problem of intercepting personal data sending through the Internet and is looking for fast and secure method to protect his activity in the global network. For these purposes I recommend VPN connection (creation of special tunnel thr ...more
To make your own fabric softener at home, simply mix together six parts water, three parts white vinegar, and two parts hair conditioner into one solution. Once you're done mixing, use ½ cup of the solution for every load of laundry during the rinse cycle to soften your clothe ...more
It's 1976. The hottest arcade game on the market is Blockade (or Blokade), an 8-bit maze game for 2 players. You and your opponent must move your characters around the screen in 90-degree angles, leaving a solid line behind them. Whoever runs into one of the solid lines first, ...more
Need help getting started on this week's WTFoto Challenge? Look no further! In this tutorial, I will teach you how to create simple chalk symbols and writing in Photoshop. So read through this post and try it out yourself—or I'll tell your cousin what you said when you were dr ...more
Many windows users, if not all, run into a virus infection once in a while. This is unavoidable when using Microsoft's operating system. Without digressing too much, the fact that Windows is such a popular OS with no controlled software sources makes it easy for viruses and ma ...more