The seated leg extension is used to isolate the quadriceps muscles. The quadriceps muscles are located on the front of the thighs. As you might have guessed, there are four muscles that make up the quadriceps. Each muscle works in unison to extend the knee. In everyday life, t ...more
Here is an exercise that really works the gluteus muscles. It is relatively easy to perform. However, for this exercise to be effective, it does require a bit of skill and proper technique. A workout mat is recommended. Get on your hands and knees. Ensure your back is flat. S ...more
If you want to improve balance and strength in the leg muscles, try the single leg deadlift (also called the single leg Romanian deadlift). This exercise is primarily going to work your hamstrings and butt. The single leg deadlift comes with a high degree of difficulty because ...more
What is Google Dorking? Well, simply put, "Google Dorking" is just an efficient way to utilise keywords in order to perform very specific searches on a given subject. In this case, one would look for websites/servers that are vulnerable to attacks or are configured improperly ...more
With the mass arrests of 25 anons in Europe and South America, and the rumors of an FBI sweep on the east coast of America floating around, times look dicey for hackers. Over the past few days, a lot of questions have been posed to me about removing sensitive data from hard dr ...more
The war between horror movie monsters has been going on for the better part of the last century. We're talking vampires, werewolves, ghosts, zombies and mutant flying creatures, each of which has had their fair share of the limelight in film. But it comes and goes. Once movieg ...more
Not every DIY project is as executable as, say, making a potato gun. Occasionally, we observe a quixotic project that is just plain wonderful. Consider rich guy Philip Anschutz and his eponymous Anschutz Entertainment Group (AEG). His ambition to bring an NFL team to Los Angel ...more
In this instructional video you will learn how the WWE choke slam is performed. Be sure to understand the stunts performed should not be done by just anybody but by professionals. Now, whoever the attacker is they want to place their right hand on the very top of the defenders ...more
The butterfly is the most difficult strokes in swimming. However, the butterfly stroke is also one of the most beautiful. Get expert tips and advice in this swimming video tutorial. Take Action: One of the most beautiful & technical strokes. Begin with dolphin kick. Arms rea ...more
Learn how to defend against headlocks, sucker punches, bear hugs, kicks, and more in this free training video series on mixed martial arts and standing self defense. Part 1 of 15 - How to Perform standing self-defense moves with MMA. Perform standing self-defense moves with MM ...more
Learn the fundamentals of Tae Kwon Do in these free online self-defense videos, including kicks, punches, blocks, stances and other moves for tae kwan do white-belts. Part 1 of 15 - How to Perform beginner tae kwon do techniques. Perform beginner tae kwon do techniques - Part ...more
lessons, including the cat stance, roundhouse kicks, center punches, and a demonstration of the Duan Chuan move. Part 1 of 15 - How to Perform basic kung fu moves. Perform basic kung fu moves - Part 2 of 15. Click through to watch this video on expertvillage.com Perform basic ...more
In these instructional video dance lessons, our expert will demonstrate intermediate-level Irish step dances, including treble shuffles, cuts, kicks, and hop moves, as well as combination clicks and stamps. Additionally, you will learn how to do the butterfly combo, complete w ...more
In this series of expert video clips, you will learn more about the fun and exciting hobby of hacky sack. Our hacky sack expert will show you a variety of different moves and tricks as well as introduce you to a few different games to play. In these educational videos you will ...more
Whether you're performing a factory reset to get your device ready for sale or trade-in, or you're wiping your device in the hopes of fixing software issues, there's a right way and a wrong way to go about it. Sure, it seems like a simple task on the surface, but if you're not ...more
Yuto Miyazawa kicks ass at electric guitar. Seriously, this kid is out of this world. What other nine-year-old is invited to perform Crazy Train, on stage, with Rock-n-Roll God Ozzy Osbourne? Named the "youngest professional guitarist" by the Guinness Book of World Records, Y ...more
It's been said time and time again: reconnaissance is perhaps the most critical phase of an attack. It's especially important when preparing an attack against a database since one wrong move can destroy every last bit of data, which usually isn't the desired outcome. Metasploi ...more
With the number of web applications out there today, it comes as no surprise that there are just as many vulnerabilities waiting for hackers to discover. Finding those vulnerabilities can be a difficult task, but there are plenty of tools available to make the process easier. ...more
Like an overbearing mother, Apple will constantly nag you through annoying red bubble alerts about iOS updates that are ready to install. Fortunately, you don't have to take this issue lying down, as there are ways to prevent your iPhone from receiving OTA updates and their co ...more
A century-old opera is getting a revamp in the UK after swapping dusty wigs and curtains for augmented reality overlays and Snapchat filters. Adding augmented reality and games alongside a musical recording of "The Cunning Little Vixen," the Welsh National Opera is ensuring t ...more
Spotlight makes finding apps, contacts, emails, songs, and old messages extremely easy on an iPad, iPhone, or iPod touch. You can even search for Wikipedia articles online, as well as perform general web searches. The only problem is that Apple kicked Google Search results to ...more
SSH is one of the most common protocols in use in modern IT infrastructures, and because of this, it can be a valuable attack vector for hackers. One of the most reliable ways to gain SSH access to servers is by brute-forcing credentials. There are a few methods of performing ...more
While Wi-Fi networks can be set up by smart IT people, that doesn't mean the users of the system are similarly tech-savvy. We'll demonstrate how an evil twin attack can steal Wi-Fi passwords by kicking a user off their trusted network while creating a nearly identical fake one ...more
Legendary drum-and-bass artist Squarepusher, the Warp records labelmate of fellow electronic music legend Aphex Twin, is back with his fifteenth album called Be Up a Hello, which is set to drop on Feb. 1. To kick off the launch, the artist has just released an amazing new mus ...more
Web applications are a prime target for hackers, but sometimes it's not just the web apps themselves that are vulnerable. Web management interfaces should be scrutinized just as hard as the apps they manage, especially when they contain some sort of upload functionality. By ex ...more
Apple's iOS 13 has been available for beta testing since June, and the stable release pushed out to everyone on Thursday, Sept. 19. To help you make the most out of iOS 13 for iPhone, we've rounded up everything you'll want to know, whether a colossal feature, small settings c ...more
The art of privilege escalation is a skill that any competent hacker should possess. It's an entire field unto itself, and while it's good to know how to perform the techniques involved manually, it's often more efficient to have a script automate the process. LinEnum is one s ...more
Your favorite music-streaming app is taking artists from its popular RapCaviar playlist on tour to five major US cities. That's right, put down your smartphones and pick up your credit card because these tickets are going to sell fast. Don't Miss: How to Recover Deleted Spoti ...more
A few days before Christmas last year, we saw the first glimpse of HoloSuit, a new motion controller by startup Kaaya Tech. This full-body motion controller is designed as a tracksuit with sensors that can be used to control devices such as a computer or Microsoft HoloLens, an ...more
Welcome back everyone! It's been quite a while hasn't it? Today we're going to kick off the second part of the Python training series by introducing modules. We'll start off by explaining what a module is and we'll give an example. So, let's get started! What Are Modules? Mo ...more
If you ever find yourself in a car that's submerged under water, your first instinct should be to try and open either the window or the door in the first few seconds of touching water. Unfortunately, if you wait any longer than that, the lopsided ambient water pressure subject ...more
We've been so worried about volumetric scans possibly robbing celebrities and performers of their agency and right to control their image that, somewhere along the way, we forgot that scans may not always be necessary to produce passable holographic performances. That's the d ...more
One of the first steps when pentesting a website should be scanning for hidden directories. It is essential for finding valuable information or potential attack vectors that might otherwise be unseen on the public-facing site. There are many tools out there that will perform t ...more
When you're gaming on your Android phone, does it sometimes feel "slow" and you can't figure out why? That means a drop in performance, which is when the frame rate dips, causing some noticeable stutters and lag. There's not really a way to know what's wrong unless you made th ...more
It always helps to be prepared for the worst. This applies to our phones now more than ever, as we depend on them to be our record keepers for text messages from friends, family, and coworkers. If you ever lose or severely damage your phone, having a backup of your precious te ...more
Each generation of smartphones ushers in a new set of top-of-the-line specs, with processing power, battery size, and display resolution growing by the year. These headlining features get the most press, but there's one unsung hero that has the potential to make the biggest di ...more
Smartphones have become such a big part of our lives these days that they're now closely associated with our personal identities. No longer is it Ford versus Chevy, rock versus rap, or PC versus Mac—now, you're either an Android person or an iOS person. Don't Miss: 10 Things ...more
In the late nineteenth century, the advent of the motion picture wowed audiences with a new storytelling medium. Nearly a century and a half later, augmented reality is establishing a new frontier in film. At the 2020 edition of South by Southwest (SXSW) Film Festival, kickin ...more
If reaching up to access Camera controls like the flash, HDR, and timer wasn't bad enough, it's gotten a lot more tedious on recent iPhones like the X, XS, and 11 series thanks to their tall displays. If you have a jailbroken iPhone, however, you can easily fix this issue usin ...more
The quality and length of your sleep will almost always dictate how the rest of your day unfolds. Sleeping fewer hours increases your chances of spending the day in a tired and cranky state, while having a restful night's sleep contributes greatly to being alert and productive ...more
Rooting. As an Android user, I'm sure you've heard the word once or twice. According to Kaspersky, 7.6% of all Android users root — but for the 92.4% who don't, we wanted to talk to you. Rooting allows you to remove barriers and open Android to a level of unprecedented contro ...more
The Xposed Framework is still alive and kicking despite the fact that development has slowed down a bit lately. Rovo89 is the only true developer behind Xposed, so it's really a one-man show. This means the popular root mod doesn't typically support the latest Android version, ...more
If you ever need to spice up a party, drinking games can really get things started quickly. The objectives are generally to complete tasks or challenges, but it's really all a thinly-veiled excuse for increasing everyone's alcohol intake in a hurry while testing levels of ineb ...more
I've been on a customizing kick over the past few weeks, showing you sweet mods for your Samsung Galaxy Note 2 like interactive live wallpapers, app and settings backgrounds, status bar tweaks, and more. But, I'm not done yet. There's still plenty to softMod on your Note 2, an ...more
You know the drill: After booting up your iPhone, you need to swipe up or press the Home button, then punch in the passcode to unlock Face ID or Touch ID. It's the way things have always been — but it doesn't have to be. Instead, you can unlock your iPhone using just your voic ...more
Penetration-testing frameworks can be incredibly useful since they often streamline certain processes and save time by having a lot of tools available in one place. Of course, the most popular pentesting framework is undoubtedly Metasploit, but there are many others out there ...more
No operating system is stricken with as many vulnerabilities as Windows, and it's often a race to release the latest patches to fix things. From an attacker's point of view, knowing which patches are present on a Windows machine can make or break successful exploitation. Today ...more
So you've managed to get a shell on the target, but you only have measly low-level privileges. Now what? Privilege escalation is a vast field and can be one of the most rewarding yet frustrating phases of an attack. We could go the manual route, but like always, Metasploit mak ...more
Cases and stickers are always great, but they aren't the only way to customize an iPhone. The software on your device is full of customization options, from a better-looking home screen and cooler lock screen wallpapers to app icon changes and a system-wide dark mode. There's ...more
Despite newer phones having larger batteries, after a few months, my battery life drops significantly. I started researching solutions after my third phone. No matter who I asked, the most recommended solution was always Greenify. And unlike other solutions, you don't need roo ...more
Last year, Razer kicked off a new trend by building a smartphone from the ground up with mobile gamers in mind. At the time, many thought the Razer Phone solved a problem that no one really had — but a year later, we're starting to see that gaming phones are perfect for more t ...more
Despite Huawei's ongoing battle with the US government, the Chinese company has continued to release phones in the US under its Honor brand. The Honor X series has been consistently released for several years, offering midrange specs at ridiculously low pricing, and the Honor ...more
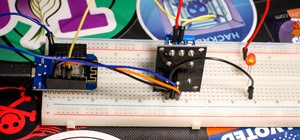
Electronic warfare tactics work by jamming, disrupting, or disabling the technology a target uses to perform a critical function, and IoT devices are especially vulnerable to attacks. Wireless security cameras like the Nest Cam are frequently used to secure critical locations, ...more
For a friendly mobile game, Animal Crossing: Pocket Camp has an overwhelming number of items and collectibles — from fruit to fish to friends. Even though it can be difficult to keep up, this guide will be a great stepping stone to creating the campsite of your dreams without ...more
Innovation Congress starts tomorrow, but its creator, Jason Keath, spoke to Next Reality today about the future of augmented reality. Innovation Congress is an event meant to discuss strategies for businesses to stay competitive in the future, with technology trends shifting ...more
Full disclosure — I have almost zero Street Fighter experience. The first time I played the game was at Barcade, way back in ... 2017. Yes, to the shame of gamers everywhere, this reviewer is a Street Fighter noob. Fortunately, my inexperience does nothing to hinder my apprec ...more
Virtual reality is all the rage these days, especially with devices like the Oculus Rift, Gear VR, and HTC Vive hitting shelves lately. But before any of those fancy, expensive headsets ever made it to the market, Google came up with a thrifty and inventive substitute in the f ...more
There are few things more annoying in life than getting interrupted—especially when you're in a groove, jamming out to your favorite song. If we can all agree on that sentiment, then why is it that our phones mute the music we're listening to for a few seconds whenever a notif ...more
The Oculus Rift is finally shipping to customers in more than 20 countries, and we're getting a good idea of how the device holds up from the initial reviews. You'll see some common threads throughout: along with an impressive virtual reality experience, the device is very com ...more
Cheap Chinese knockoffs have been around for ages, but recently, skyrocketing demand has led to a massive influx of counterfeit smartphones. Sellers on Craigslist seem to have no trouble getting ahold of these fake devices, then passing them off as the real deal and turning a ...more