Whether you use shadow puppets or marionettes, put on a fanciful puppet show with these tips. Step 1: Decide on script Decide on the puppet show script you wish to use. Write your own dialogue for a creative, personalized touch, or use an already-written script. TIP: Puppet ...more
Why justify the cost of buying a corsage from your local florist? Make an affordable corsage yourself that reflects your personal style. You Will Need * Flowers * Leaves * Scissors * Wire cutters * Floral wire * Floral tape * Baby’s breath or other filler * Colored elastic tap ...more
Learn how to play "Underneath Your Clothes" by Shakira, an acoustic guitar tutorial. Follow along with this demonstration, tabs and lyrics here: Standard Tuning: Capo On 1st Fret Em Bm You’re a song C D Written by the hands of God Em Bm Don’t get me wrong cause C D This migh ...more
Let magician Ryan Oakes show you how to make an egg magically balance on its end! This easy trick will amaze your family and friends! You will need an egg, salt and a handkerchief. Sometimes we use materials that require adult supervision... like scissors so make sure you have ...more
Sometimes science looks like magic and that's exactly what Ryan Oakes is going to demonstrate with this cool trick. You will need pepper, bowl of water and liquid soap. Sometimes we use materials that require adult supervision... like scissors, so make sure you have friends an ...more
The United Kingdom has long been known as an international hub of yellow tabloid journalism. The News Of The World, one of the nation's largest tabloids, is famously in court right now because of the deplorable methods it used to acquire salacious information about interesting ...more
The developing team Techland gets a free pass. Having thoroughly enjoyed their previous title, Call of Juarez: Bound in Blood, this sequel was bought on day one by good ol' fashion blind faith. After playing for most of today, it's still to early to tell if the game is a mess ...more
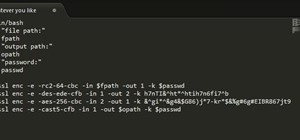
This is the first of a multi-part series on steganography techniques. Steganography, the art of hiding things in plain sight, has existed for a long time, and in many forms. When you manipulate the alphabet to have your own cipher and decipher, this is considered steganography ...more
On October 7th, the IndieCade Conference will open its doors to some of the most innovative minds in the independent gaming industry. The three day event located in Culver City, California includes presentations by notable indie designers, workshops, galleries, and mixers. On ...more
Exploring a new city is tough if you're all by your lonesome. But if you have your iPhone on you, you're not alone at all... there's tons of great apps available for discovering the city around you. We've previously featured an app that helps you decide on what bar or club to ...more
A couple months ago, the world was supposed to end. It didn't. But that didn't stop the Centers for Disease Control and Prevention (CDC) from warning citizens of one global possibility besides complete destruction—ZOMBIES. They used the farcical flesh-eating living dead as an ...more
The African Soft Fur Rat though new to the pet trade is a unique little rodent with unusual qualities. Not only is this little rat a great step up for people who feed reptiles it is virtually odorless and that is definately a plus for those who would like to have a pet rat or ...more
Got a knack for speeding? Like running red lights? Believe or not, the police have better things to be doing than pulling you over, like catching real criminals. That's why more and more cameras are popping up at known speeding zones and on street corners—so the cops can clean ...more
There can be areas of preparation you may not have anticipated before you start your project of installing your laminate flooring. Concrete Preparation If you are installing your laminate flooring over a concrete slab, you may not notice until you remove the old carpet that ...more
Here's a quick, simple prank to pull on anyone in under 2 minutes. It works especially great for someone who has tons of icons on their desktop! It makes the computer look the same, but nothing on the desktop works! Here's how it goes... You're target leaves their desk for a ...more
This post taken from FrontierVille Post - click through to see the original and for better formatting. Another new goal that was added is the sunflower goal. As the sunflower crop is relatively new to the game, you will see this goal pop up at some point soon! It is likely to ...more
Whether you are protecting your children or hiding personal information, there are ways to block unwanted websites from your computer. Follow this tutorial and learn how to accomplish this on a Windows PC easily. Step 1: Block websites Block web sites on Internet Explorer by o ...more
Get out your army pants and prepare to conquer your backyard. Learn how to play Capture the Flag with this video Step 1: Choose teams Divide the players into two teams of equal size. Step 2: Find playing field Find a large outdoor playing field that includes both open and ...more
A gerbil makes a great “starter pet” for a child. Gerbils are friendly, fun to watch, quiet, and clean little guys whose cages don’t get smelly as fast as some animals’. You Will Need * A gerbil * A large wire cage or 20-gallon glass aquarium * Bedding * Gerbil food * Fresh gr ...more
Learn how to play hide-and-seek. If you need a rainy day activity for the kids, or just want to relive your childhood, hide-and-seek is a great game for everyone. You Will Need * A place to play * Someone to be "it" * People to hide Step 1. Designate hiding spots Designate ...more
It's the coolest pool party game ever named after a 13th-century explorer. Marco Polo is a perfect way to cool down and have fun. You Will Need * Friends * A pool *Warning Never run along the side of a pool. Children should always swim with adult supervision. Step 1: Grab ...more
Remember that scene in The Matrix when Trinity uses a realistic Nmap port scan, followed by an actual SSH exploit (long since patched) to break into a power company? Well, believe it or not, but that scene is not far fetched at all. If you want to exploit vulnerabilities and r ...more
Social engineering is described as the clever manipulation of the natural tendency of human trust. All of the passwords, locks, and encryption in the entire world are useless against a good social engineer who can charm or trick you into giving it up. But what once started as ...more
WonderHowTo is made up of niche communities called Worlds. If you've yet to join one (or create your own), get a taste below of what's going on in the community. Check in every Wednesday for a roundup of new activities and projects. Thanks to all of our moderators and contrib ...more
Today's article serves as a general guide to keeping Windows 7 and Vista clean. The goal is to clean up your messy computer and have it running at maximum performance in no time. The question at hand is—what is your computer's performance like? Not great? Do you think it coul ...more
Welcome to Minecraft World! Check out our advanced tutorials and come play with us on our free server. As of the 1.0 release, Minecraft has an end. That is to say, The End and the The End has Dragons. This guide is for those of who are want to visit The End and kill an Ender ...more
+Nik Cubrilovic discovered last week that Facebook could track your web activities even after you logged out of your Facebook account. After some blatant denials from Facebook spokespeople, Facebook decided to fix the logout issue, but not before +Michael Arrington, on his new ...more
Sometimes a simple drowning trap is too boring, and you want something that's a little more stylish and exciting. That's where this trap comes in! This is what I like to call "The Mangler". It consists of a set of pistons that chomp together, literally chewing up your enemies ...more
ACTION MOVIES The Hunger Games (2012) Set in a future where the Capitol selects a boy and girl from the twelve districts to fight to the death on live television, Katniss Everdeen volunteers to take her younger sister's place for the latest match.Dir: Gary Ross With: Jennife ...more
Did you know there is hidden data in your digital pictures? Well, there is, and that data might be a security risk to you. Think back at all of those pictures you're in and are connected with. I'm sure some of those you'd like to distance yourself from. And surely you wouldn't ...more
Today's guide is on creating a password protected folder on Windows 7 without any additional software. Yes, you heard that right. No extra software at all! This guide is intended for beginners. But please note, this method should not be used to store financial or otherwise hig ...more
Welcome to Minecraft World! Check out our advanced tutorials and come play on our free server. Welcome back to Minecraft World's Ultimate Survival guide! A few days ago, we reviewed a good way to start off right when you spawn, plus a small rundown of the mobs. Now we will co ...more
As Google+ became available to more people, it started running into issues of accounts being suspended due to names that did not sound "real". According to Google+'s community standards, names that users "commonly go by" were encouraged, but not pseudonyms. Those who were usin ...more
Giveaway Tuesdays has officially ended! But don't sweat it, WonderHowTo has another World that's taken its place. Every Tuesday, Phone Snap! invites you to show off your cell phone photography skills. Submit your best shot to our weekly competition for a chance to win an awes ...more
A Self-Protection Guide 1) You can help protect yourself from violent crimes. Self-protection involves:Avoiding crime * Without a doubt prevention is your best prevention against crime.Knowing what to do in case of an attack* An attack can happen despite your best efforts to p ...more
There are a few ways to make trapdoors, but out of all of them, this one is my favorite. It's fast, completely hidden, and both opens and closes. This particular trapdoor can be used for a variety of purposes, such as hiding your valuable possessions, having a secret entrance ...more
We've talked about the deep web before, but we never really covered the details of what's out there. It occurred to me that a nice list of resources would be very helpful to all of you anons out there. Think of this like a helpful brochure to the hidden web. However, I should ...more
It turns out that the popularity of soft circuit electronics has leaked out of the interwebs and into the hands of the U.S. military. Soft circuit electronics allow you to literally sew electronics circuits into fabric using flexible conductive thread instead of wire. Soft cir ...more
Today isn't actually Pi Day, but I was unable to get this article out in time. Pi Day was actually yesterday, March 14th (3.14), so let's call this a post-Pi Day treat! I've usually stuck to computers and security in the past, so I thought I'd toss things up a bit and give yo ...more
TOP MOVIES 2011 The Artist (2011) Hollywood, 1927: As silent movie star George Valentin wonders if the arrival of talking pictures will cause him to fade into oblivion, he sparks with Peppy Miller, a young dancer set for a big break.Dir: Michel Hazanavicius With: Jean Dujard ...more
With the mass arrests of 25 anons in Europe and South America, and the rumors of an FBI sweep on the east coast of America floating around, times look dicey for hackers. Over the past few days, a lot of questions have been posed to me about removing sensitive data from hard dr ...more
You've probably seen those deep-web images floating around on the Internet. Usually, it goes something like this: There is a towering iceberg and the deeper the underwater portion extends, the more “hidden” and “exotic” the content is described to be. Sometimes these images ar ...more
Welcome to Minecraft World! Check out our advanced tutorials and come play on our free server. Harvesting items from animals no longer requires wasting precious time chasing after them. During last Saturday's Weekly Workshop, we built a few different kinds of animal harvester ...more
Previously, we talked about how to secure Firefox. Today, we will talk about securing a Chromium based Browser. Why? Because Chrome recently beat Firefox in holding more customers. It is obvious that Google Chrome tracks our every move online, so what alternatives is out ther ...more
When your computer first connects to a nework, it sends out a request on the network to lease an IP from the router. The router then leases your computer an unused IP address, which is used as a unique routing address for sending traffic that is meant for you, to you. As every ...more
You Want White Teeth Without Expensive Over-The-Counter Products? Here's An Inexpensive, Effective Solution. Everywhere you look there are products for whitening teeth. You could spend a fortune on products you have to use everyday. This tutorial will show you a natural, inex ...more
STANDP'S CUSTOM DESKTOP "ASK NOT WHAT YOUR DESKTOP CAN DO FOR YOU...". http://standp-how-to-vidzzz.wonderhowto.com/corkboard/new-post/text/ Showing newest posts with label tips-n-trick. Show older posts DEC 07 Computer Backup If you have taken good care of your computer th ...more
Definitions Aging If you bought a bottle of Twelve Year Old Scotch, and you hang on to if for nine years, guess what you have? A bottle of 12 year old Scotch. Scotch Whiskey is different from wine in the aging process. Only bad things can happen after its bottled. Keep it in ...more
WonderHowTo is a how-to website made up of niche communities called Worlds, with topics ranging from Minecraft to science experiments to Scrabble and everything in-between. Check in every Wednesday evening for a roundup of user-run activities and how-to projects from the most ...more
WonderHowTo is a how-to website made up of niche communities called Worlds, with topics ranging from Minecraft to science experiments to Scrabble and everything in-between. Check in every Wednesday evening for a roundup of user-run activities and how-to projects from the most ...more
Welcome to Minecraft World! Check out our tutorials, post to the community corkboard, and come play on our free server! Hey, it's iDwarf bringing you another redstone competition! The last one was fairly successful for being new. As you all know, I will be running these compe ...more
Introduction The 3 major anonymity networks on the Internet are Tor/Onionland, I2P and Freenet. If you feel confused on which one is the "best" one to use the answer is simple. Use all three! Each anonymity network is designed for a different specific purpose. One network al ...more
In my recent Darknet series, I attempted to connect the dots on the Deep Web. I covered the two largest anonymity networks on the Internet today, Tor and I2P. While my initial four articles were meant as an introduction, I ended up receiving a lot of interesting comments and m ...more
Do you need to email your wife your Social Security number? Send confidential business plans to your partner in Thailand? Send your hacker buddies the recovered hashes from last night's breach? Try using GPG, a valuable and easy to use open-source encryption program. In my fi ...more
WonderHowTo is made up of niche communities called Worlds. If you've yet to join one (or create your own), get a taste below of what's going on in the community. Check in every Wednesday for a roundup of new activities and projects. This week has been an exciting one. The com ...more
Here is the final part in Null Byte's series on mastering the skills in The Elder Scrolls V: Skyrim. We have already covered the slick and brutal methods to raise our Spellcasting and Combative skills. Skyrim's intelligent new leveling system has trumped the former methods of ...more
Social network fatigue sets in when it starts to feel impossible to keep up with all that new content from your friends, followers, and acquaintances on a daily basis. You lose track of stuff you wanted to read more about, and you miss important news from your friends, but are ...more
Facebook unveiled a lot of changes last week, and, as usual, it's causing a lot of consternation and controversy. People within my Facebook, and on Google+, keep asking how to remove the ticker, and are trying, and mostly failing to make sense of the changes. I've decided to ...more
Welcome to the Google+ Insider's Guide to all things Google+. We're dedicated to keeping you updated with all the latest news, tips and tricks on Google+, and this official index will serve as a one-stop catalog of all our How-To articles, as well as all the news & updates we' ...more
If you follow indie games at all, you've probably heard of Bastion. During its development, it took home numerous Best in Show prizes from E3 and other game conventions while building up an incredible amount of buzz in the games press. Part of what is intriguing about Bastion ...more