Over the years, I have enjoyed playing with Asterisk. I have found Asterisk to be extremely powerful and fun to play with. There are several books and many scattered how to articles out there, but most are outdated and the information required to build Asterisk from beginning ...more
How to Use Your Mac as a Server: Turn your Mac Mini into a server! Yes, that's right, with a little know-how and a little spunk, you can turn an inexpensive Mac Mini computer into a server to provide services over you network. You won't even need the Mac OS X Server, just the ...more
How to Use Your Mac as a Server: Turn your Mac Mini into a server! Yes, that's right, with a little know-how and a little spunk, you can turn an inexpensive Mac Mini computer into a server to provide services over you network. You won't even need the Mac OS X Server, just the ...more
How to Use Your Mac as a Server: Turn your Mac Mini into a server! Yes, that's right, with a little know-how and a little spunk, you can turn an inexpensive Mac Mini computer into a server to provide services over you network. You won't even need the Mac OS X Server, just the ...more
How to Use Your Mac as a Server: Turn your Mac Mini into a server! Yes, that's right, with a little know-how and a little spunk, you can turn an inexpensive Mac Mini computer into a server to provide services over you network. You won't even need the Mac OS X Server, just the ...more
How to Use Your Mac as a Server: Turn your Mac Mini into a server! Yes, that's right, with a little know-how and a little spunk, you can turn an inexpensive Mac Mini computer into a server to provide services over you network. You won't even need the Mac OS X Server, just the ...more
How to set up your Playstation 3's (PS3) media server.
Probably SSH is not as clean and fast as other useful tools like netcat, but it has some features which are very useful, and when you'll need them, here's how to behave with that huge amount of computers all over your house. Probably, you already know what SSH means, but for ...more
Last weekend, some unlucky Gmail users inadvertently had their email accounts wiped out. Actually, it was 0.02 percent of all Gmail users—or roughly 40,000 of the 200 million who use the email service, due to an "unexpected bug" which affected copies of the data. Gmail does ma ...more
As a web developer, I often read articles about hackers (from the lowly to the knowledgeable) infiltrating websites via the dreaded 'SQL Injection' method and completely taking control, changing, gaining access, or destroying the owner's data. As a fellow web developer, I'm su ...more
Use an old PC that has been setup as a server to perform helpful tasks such as backing up computers on your network, storing media files in a central location, share one printer with every computers computer in the house. Visit www.VitaminCM.com for the full article.
How to Use Your Mac as a Server: Turn your Mac Mini into a server! Yes, that's right, with a little know-how and a little spunk, you can turn an inexpensive Mac Mini computer into a server to provide services over you network. You won't even need the Mac OS X Server, just the ...more
Installing Joomla on a Windows server can be tricky, on Windows running IIS even more so. Installing Joomla 1.5 in this scenario has caused many frustrations.In this video, we take the process step by step and jump over the hurdles that cause some people to wind up pulling the ...more
Systm is the Do It Yourself show designed for the common geek who wants to quickly and easily learn how to dive into the latest and hottest tech projects. We will help you avoid pitfalls and get your project up and running fast. Search Systm on WonderHowTo for more DIY episod ...more
Have you ever wanted to make your own Minecraft server on Windows? This tutorial will teach you how, without having to download Hamachi. The whole process is a lot simpler than you might think, and it will only take a few minutes! You will need: Firefox web browser Computer ...more
WikiLeaks. In recent weeks, it's been the hottest topic on the web. It's been attacked on a multinational level by political influence peddling. First, U.S. Senator Joe Lieberman swayed Amazon's decision to stop hosting WikiLeaks. Then, Tableau Software removed graphs from th ...more
After years of being a PC technician and Windows System administrator, I had the blind hatred for Apple that I thought I was suppose to have. I swore that I'd never even touch an iPod, let alone buy an Apple product. But I found a new career that drug me out of the Windows ser ...more
Have you ever noticed that whenever you setup your voicemail account after getting a new cell phone number, it asks you to create a security pin to access your voicemail from other phone lines? When you call your home or cell number from another phone, after a few rings your ...more
In this video tutorial, viewers learn how to setup Microsoft Outlook 2007. Begin by opening the Outlook Express 2007 program. Then click on Tools and select Account Settings. Under the Email tab, click on New. Now type in your name, email address and password. Then click on Ne ...more
This video demonstrates the technique to setup a Yahoo email on an iPod Touch. You start going into settings and then clicking account. On the next screen you will click "Other" and then click on "Pop". At this point you enter your name and email address that you use for your ...more
Using a simple peice of software XAMMP to streamline the setup process of apache+php+mysql
This is a how-to –video on using hydra 5.4 to crack FTP passwords. This video is intended for educational purpose only. It reveals the basics of hacking a FTP server using dictionary search technique. Here are the steps involved. 1) Download the software hydra 5.4 form the ...more
Interested in teaching an online course using your own server but can't quite figure out how to install everything you'll need? This video demonstrates how to setup a MySQL database for use with Moodle, the free, open source course management utility, which requires a MySQL da ...more
This new episode of Full Disclosure shows you how to use a SSH Tunnel to secure your data when you are on an untrusted LAN (ex. Coffee Shop, School's network, or Defcon). Furthermore, you can use the SSH Tunnel to bypass the LAN's internet filters. The SSH tunnel protocol work ...more
In this tutorial, we learn how to configure Outlook 2007 to work with Gmail. First, go to the start menu and then open up Outlook. From here, go to tools and then options. After this, go to the mail setup tab and then click e-mail accounts. Then, click on "new" and then next. ...more
In this tutorial, we learn how to open ports on a Linksys router for your DVR. First, make sure your internet is connected and your DVR is connected to Linksys. Next, log into your Linksys router online and set up your DVR to the "DHCP" section. When you have the information f ...more
In this Software video tutorial you will learn how to setup email in Microsoft Office Outlook 2007. Suppose you have a Yahoo email id and you want it in Outlook, go to tools > account settings > email > new and fill out the details. Then check the box next to ‘manually confi ...more
Carole Gallesie from Creative Media Web shows viewers how to set up a new account in Microsoft Outlook Express. Express is preferred because it is a scaled-down version of the popular email client and it is easier to navigate. From your Windows desktop, go to the start menu, a ...more
Tool is selected, followed by email accounts and a selection is made at the "add new email account" option , the "next" button is clicked. Pop3 is selected and the next button. The required information is filled in such as name, amail address, incoming and outgoing mail server ...more
Hello, everyone. My friend and I recently released a Defense of the Ancients (DotA) map that went viral and thought I should share it with Minecraft World on WonderHowTo since you guys helped me out when I first started making videos! We were featured on Kotaku, RockPaperShotg ...more
Technology: The Less You Know the Better? I'm sure everyone is now aware of GPS technologies and tracking techniques these days, with the release of numerous documents (even lawsuits) on big name companies like Apple, Microsoft, and Google. Yes, 2011 was a good year for eye-o ...more
Welcome to Minecraft World! Check out our tutorials, post to the community corkboard, and come play on our free server! Tired of building the same old TNT cannon over and over again? Looking for something explosive to occupy your time for the next few hours? Try making this a ...more
OpenVPN is the open-source VPN (Virtual Private Network) client, used over the PPTP (Point to Point Tunneling Protocol). It allows you to connect to a remote network over a secure, encrypted connection and mask your IP addresses over all ports. Since there is only one "hop," t ...more
This video tutorial shows how to open a port for torrent downloading on your computer. Click Start menu, type cmd command in Search area. In cmd window type ipconfig and press Enter. Remember or write down your IP adress. Type exit and press Enter to close cmd window. Press ...more
Although Grand Theft Auto 4 was released, many people are still going to want to play GTA San Andreas. Here's how to download and install GTA San Andreas Multiplayer. First, go to Google and search GTA San Andreas Multiplayer. Then, click on the first result that comes up. Go ...more
Sharing a laptop's wireless Internet connection with other computers connected to its Ethernet port is a great skill to know. It can be good for a number of reasons; Your computer may not have proper hardware to have a standard setup, or you may have an awkward network topolog ...more
Welcome to Minecraft World! Check out our advanced tutorials and come play on our free server. Redstone gives you the power to construct an endless number of possible machines, mechanisms, and devices. With redstone one can move more efficiently, send messages long distance, ...more
You'll see a lot of Linux action going down here at Null Byte. We use Linux for hacking-related stuff because it provides a more relaxed programming environment, making it easy to write exploits and tools. Linux has many features Windows is lacking, such as full control over t ...more
With so many wireless iOS networking apps for the iPhone, iPad, and iPod touch available, there’s very little reason to connect any of these devices to iTunes, except to update the software. Besides, importing and exporting photos using iTunes has never been one of the best fe ...more
Welcome to Minecraft World! Check out our tutorials, post to the community corkboard, and come play on our free server! A moving walkway could be a great addition to a courtyard, airport, or even a mansion. It's very unique and simple to do! If you end up incorporating this t ...more
Some of you might be using Tor to host hidden services, and some of you might not even know what hidden services are. If the latter's you, do not miss this article. Why? Because you can host your websites and services on the I2P darknet. It's safe and secure—it's anonymous. I ...more
Welcome to Minecraft World! Check out our full tutorials and make sure to post to the community forum if you have any questions or cool builds you want to share. All of these tricks were taught as a part of one of our old community workshops for the 1.2.3 update, but the majo ...more
Welcome to Minecraft World! Check out our tutorials, post to the community corkboard, and come play on our free server! The workshop last Saturday revolved around how to build a Hidden Passageway, and the turnout was great. We had around eight of us in TeamSpeak, and even I l ...more
WonderHowTo is a how-to website made up of niche communities called Worlds, with topics ranging from Minecraft to science experiments to Scrabble and everything in-between. Check in every Wednesday evening for a roundup of user-run activities and how-to projects from the most ...more
Welcome to Minecraft World! Check out our tutorials, post to the community corkboard, and come play on our free server! Looking to build an awesome one-way entrance into your base? Why not create an awesome drawbridge so that no one can enter without your permission? This sty ...more
Big brother is watching when you're playing around on another system—and big brother is that system. Everything from operating systems to intrusion detection systems to database services are maintaining logs. Sometimes, these are error logs that can show attackers trying vario ...more
Have you always wondered how to make a customizable and efficient TNT cannon in Minecraft? Are you looking to raid some bases on a PVP/factions/griefing server, but don't know where to start? Well, this tutorial will go over how to make a TNT cannon, and the different ways you ...more
Welcome to Minecraft World! Check out our tutorials, post to the community corkboard, and come play on our free server! Are you looking to clean up the look of your Minecraft with something other than a simple texture pack? Do you sometimes experience lag spikes that drop you ...more
Welcome to Minecraft World! Check out our tutorials, post to the community corkboard, and come play on our free server! Have a ton of saplings in Minecraft, but just don't know what to do with them? To some players, saplings seem like useless pieces of in-game junk, but that' ...more
Are you tired of wasting diamonds and iron on creating hoes? Are you looking for a fun way to farm melons? Or do you simply want to show off to your friends? This tutorial will go over how to make a jaw-dropping semiautomatic melon farm. Not only will you be the talk of the se ...more
There are many impressive accomplishments in Minecraft, too many to name in fact. Sprawling builds, complex machines, and massive servers are the hallmark of Minecraft and things keep getting bigger and better. No one doubts the epic scale Minecraft has reached, but every once ...more
Welcome to Minecraft World! Check out our tutorials, post to the community corkboard, and come play on our free server! The workshop last Saturday revolved around creating a working movie screen in Minecraft, and everyone joined in to see how it works. But this tutorial is fo ...more
Backing up your files is a requirement in today's world of tech. In an instant, your storage device can fail. This is an unacceptable situation that should never happen to anyone. Storage is cheap, and backups are easier than ever to perform. Most of the time, this can be comp ...more
Welcome to Minecraft World! Check out our advanced tutorials and come play on our free server. This past Saturday we had a great turn out for the Weekly Workshop, and we even managed to get a few of you in TeamSpeak. Thanks to all who joined in, hope you learned some awesome ...more
Wondering how to set up Mozilla Thunderbird? Follow these simple steps: 1. When you first launch Thunderbird you are asked to create a new account. First click Email account and click Next. 2. Complete your name and email address then click Next. 3. Next you are asked for s ...more
“Zero-zero is a big score.” Ron Atkinson "Part 0? Are we in computer science class or what? We aren't talking about arrays here, are we?" No, nothing to do with arrays. This article is simply for if you are thinking of creating a new WordPress blog and want to do that on a M ...more
Imagine for a moment that a VPN is like putting on a disguise for your computer. This disguise works to change your IP address, secure your traffic with encryption, and mask your location to bypass regional restrictions. This makes it a helpful tool for both whistleblowers and ...more
Hello fellow Null-Byters! This is my first post so please be respectful and constructed criticism is much appreciated. I am no professional, however I believe that it is important to understand technologies before you go poking at them and trying to break them, I therefore dec ...more
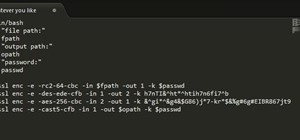
SSH is a powerful tool with more uses than simply logging into a server. This protocol, which stands for Secure Shell, provides X11 forwarding, port forwarding, secure file transfer, and more. Using SSH port forwarding on a compromised host with access to a restricted network ...more
SSH local forwarding is a must for covering your tracks and getting out there to do your work. Also called SSH tunneling, this process will put one or more steps between your machine and the machine you're working on, for security and other purposes. It can be a bit daunting f ...more